All About Doxing 2022
⭕🔱🇰🇦🇱🇮™🔱⭕
Doxing often involves hackers attempting to embarrass or shame individuals by publishing confidential information, images or videos obtained from their personal accounts. Initially, doxxing was used by hackers to "out" the identities of fellow bad actors/hackers. However, more recently, it has been used to attack users with opposing viewpoints.
In a doxing attack, hackers might publish someone's:
👀Real name
👀Telephone number
👀Social Security number
👀Home address
👀Employer
👀Credit card numbers
👀Bank account numbers
👀Personal photographs
👀Social media profiles
How does doxing work
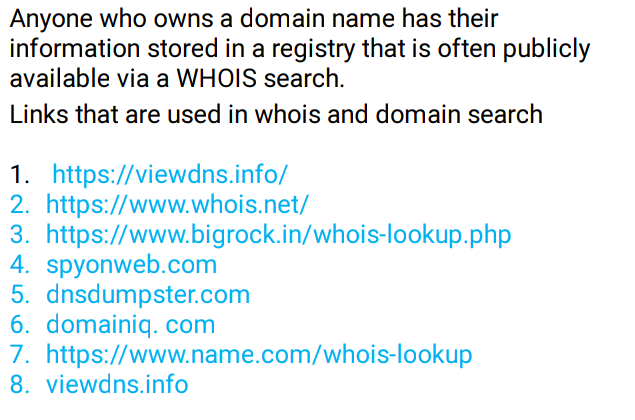
Running a WHOIS search on a domain name
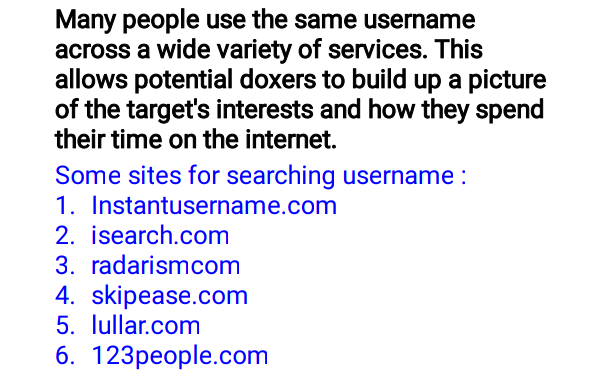
Tracking Usernames
Phishing
Stalking Social Media
Checking Goverment Records
Google Dorking
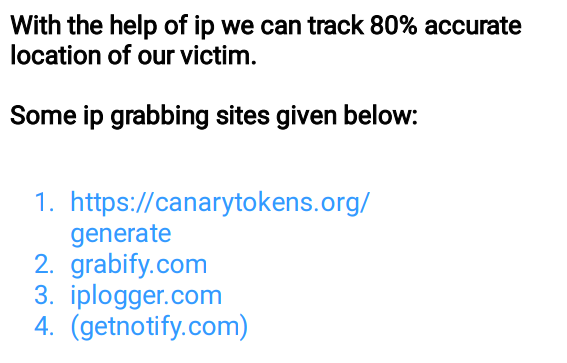
Tracking IP address
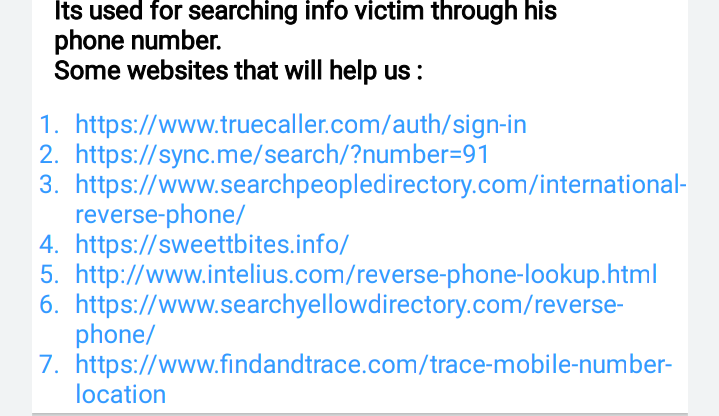
Reverse Mobile phone lookup
Packet Sniffing
Data Brokers(Leaked Data)
Searching on Darkweb
Examples of Doxing
1. Celebrity Doxxing
It’s not uncommon for journalists to find out a celebrity’s personal life information and to publish such gossip on their media platforms. However, doxxing isn’t your regular entertainment news. Here, the hacker publishes the celebrity’s sensitive information such as their payment card info, email address, social security number or phone numbers.
2. Faulty Doxxing
Sometimes, doxxing is done by internet vigilantes who can’t be bothered to properly research or investigate their victims to ensure they have the right person. Instead, they wrongly link people to activities or situations that are unrelated to them. Due to such “faulty” doxing, hence the name, innocent people face:
- reputation loss,
- employment loss,
- harassment,
- physical harm, or
- loss of life.
3. Revenge Doxxing
Sometimes, people use doxing as a means of taking revenge. They publish their enemy’s some publicly identifying information online to cause them shame.
4. Swatting Doxxing
Another method of doxing is known as “swatting.” This occurs when a person wrongly accuses someone of a crime and sends police (or a SWAT team, hence “swatting”) to the victim’s address to cause them harassment. However, often such doxxing can prove fatal for the victim.
5. Crime Doxxing
While the swatting is done for fun, there are some people that use doxxing to execute serious crimes like murder. They reveal their enemies’ personal information online and provoke others to harm them. The motive can be personal revenge or showing disagreement or hatred towards any specific cause, religion, activity or race.
How you get doxxed?
🖤 Username Doxing
🖤Whois and Domain More
🖤Stalking Social Media
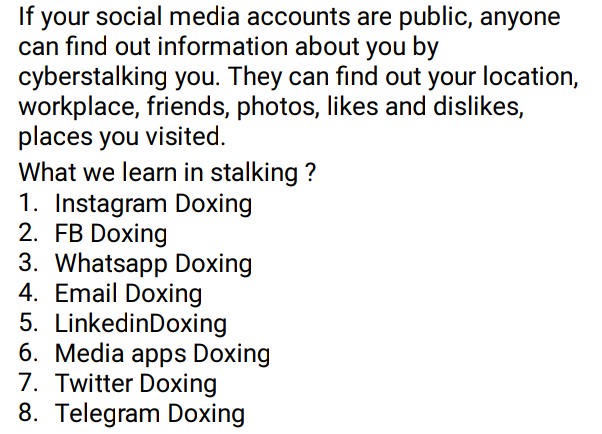
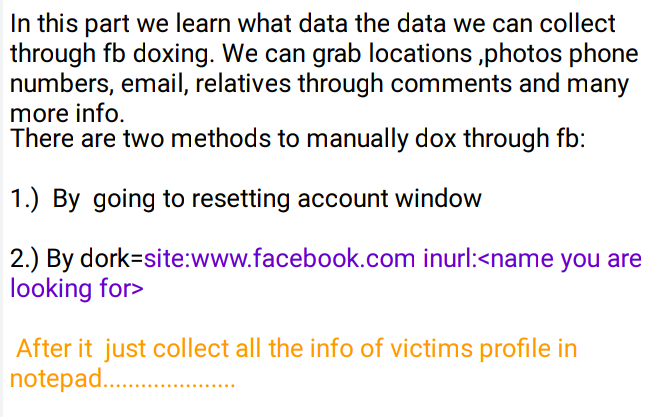
🖤Facebook Doxing
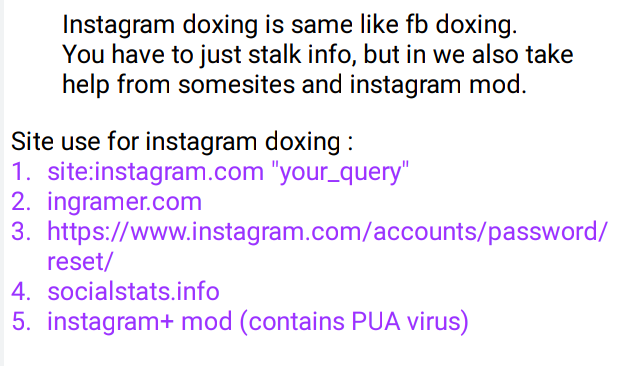
🖤Instagram Doxing
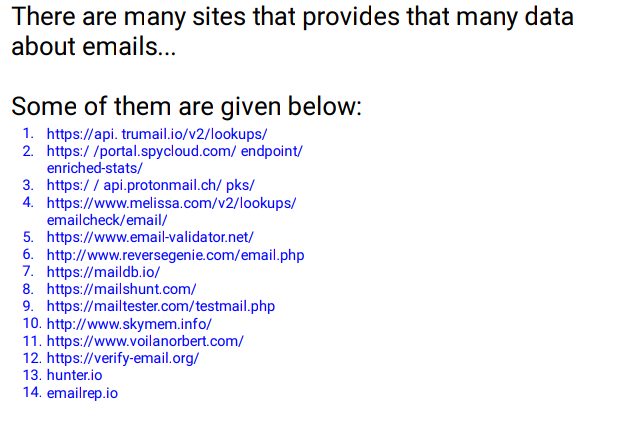
🖤Email Doxing
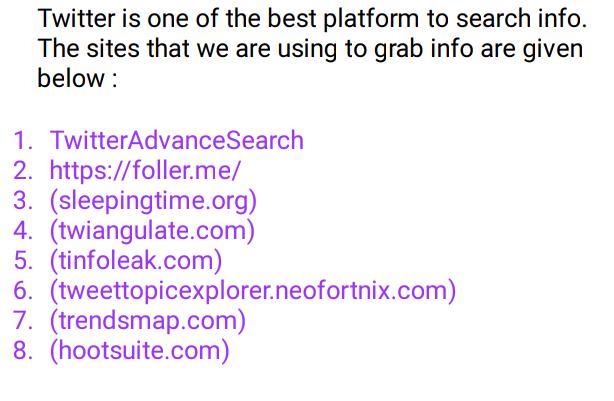
🖤Twitter Doxing
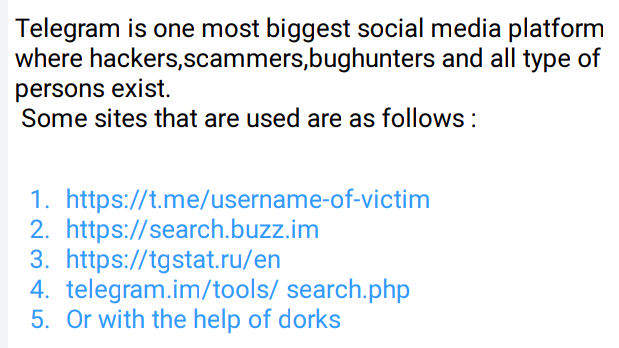
🖤Telegram Doxing
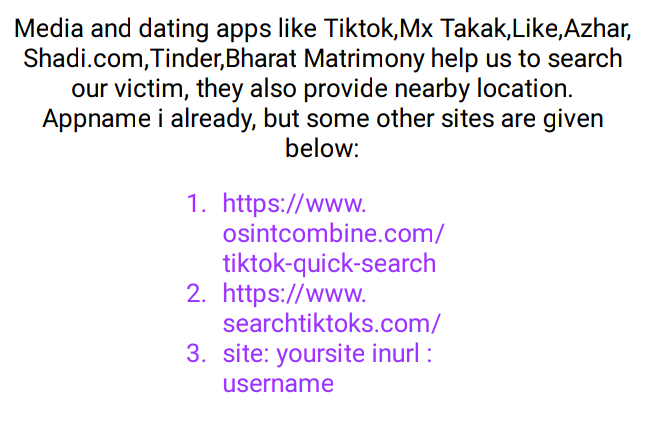
🖤Media And Dating Doxing
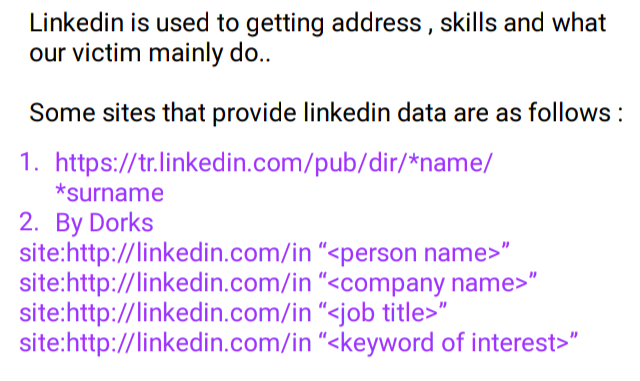
🖤LinkedIn Doxing
🖤Indian Goverment Data Doxing

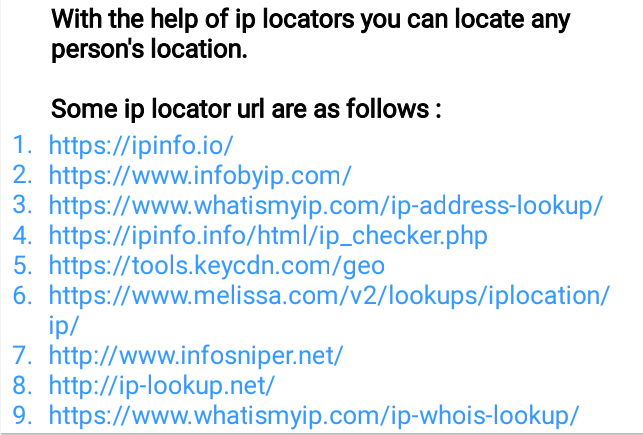
🖤IP Locators
🖤Reverse Phone Lookup
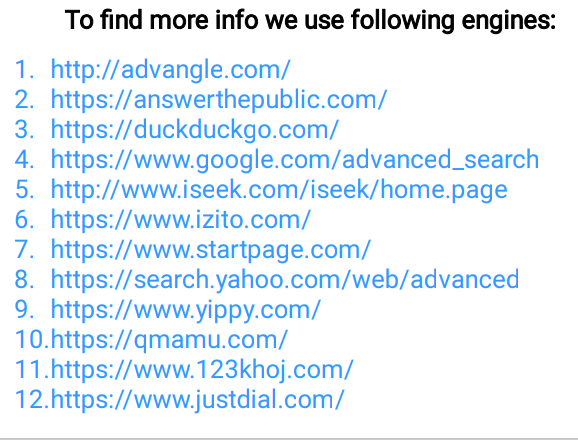
🖤Search Engine Doxing
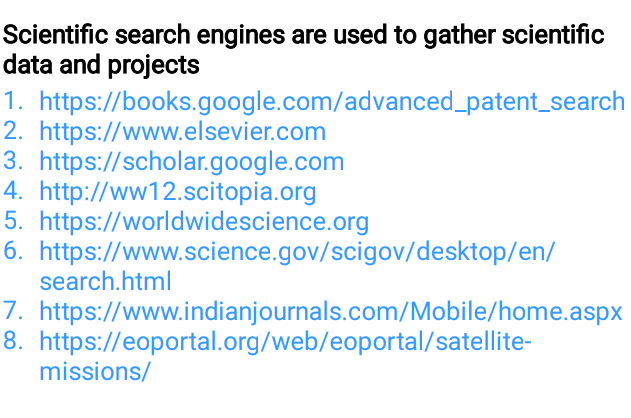
🖤Scientific Search Engine
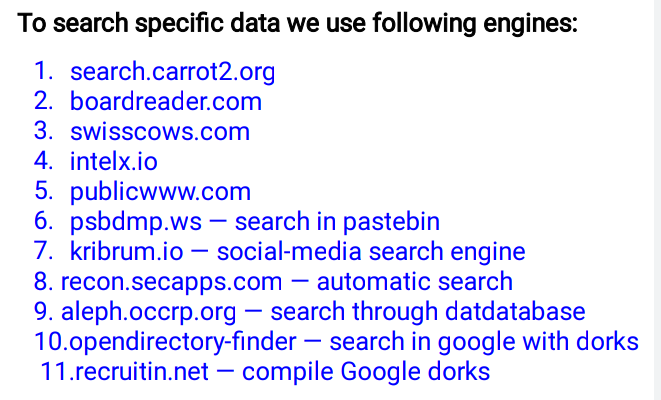
🖤Specific Search Engines
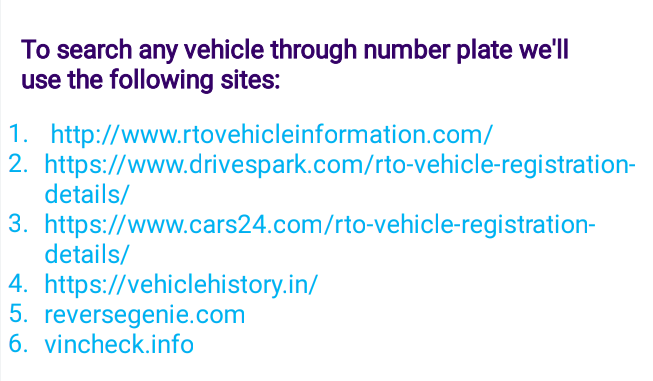
🖤Vehicles Search
🖤Archives Data
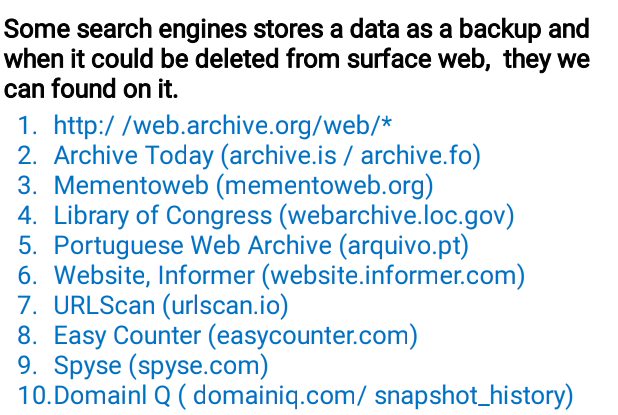
🖤Directories
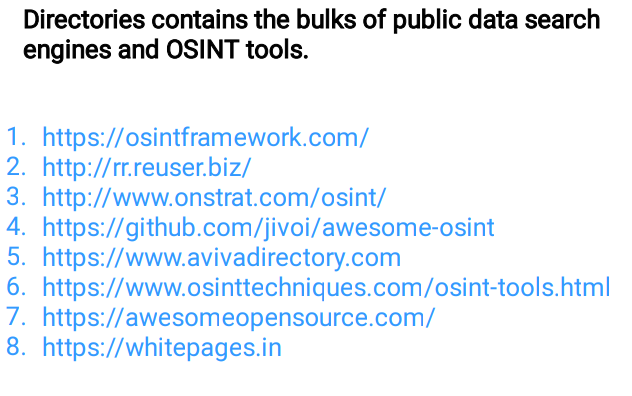
🖤Mac Address
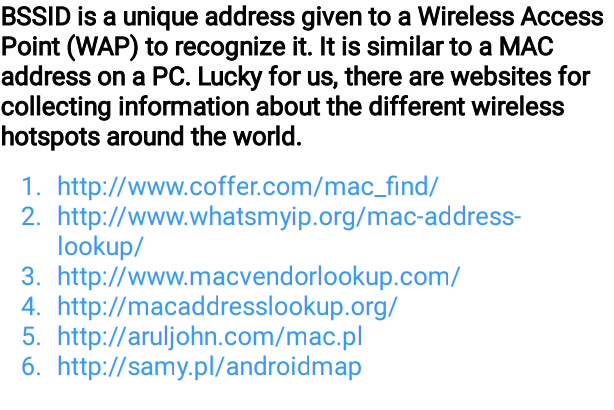
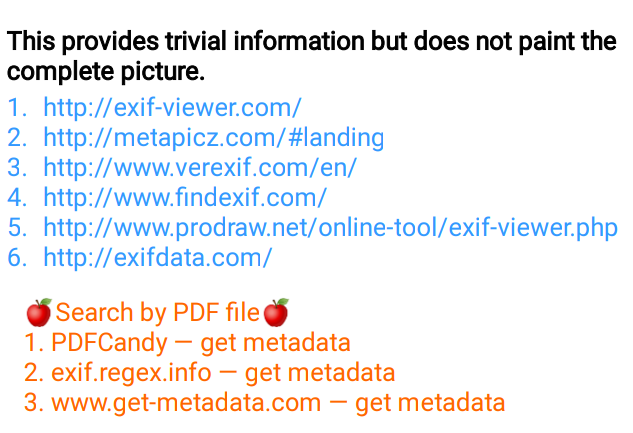
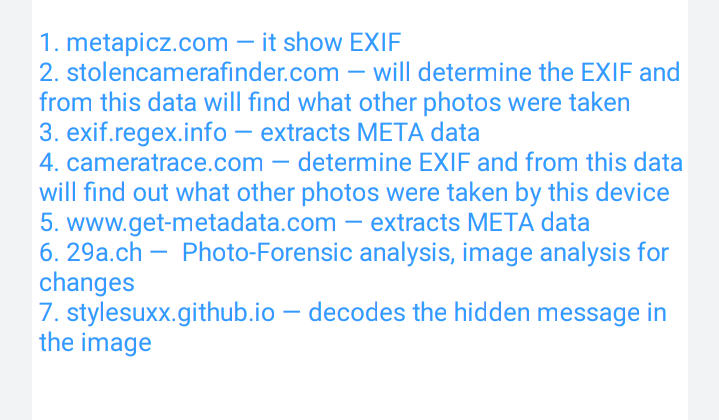
🖤EXIF Data
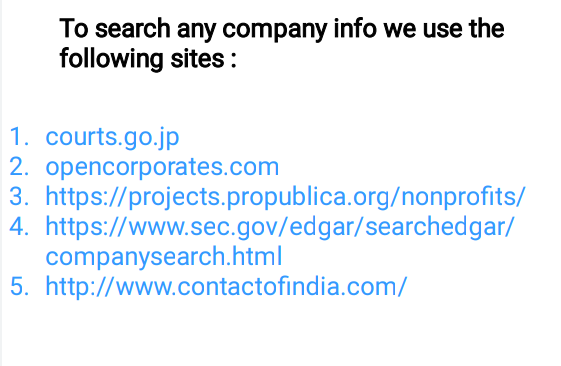
🖤Company Search
🖤PNG and JPEG Exif
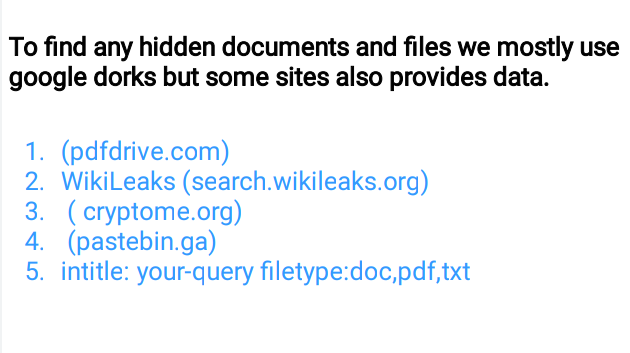
🖤Documents Doxing
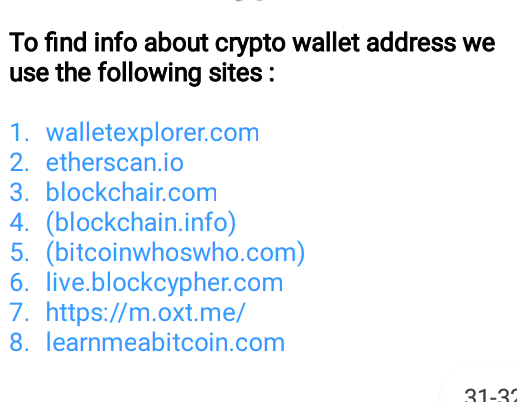
🖤Crypto Doxing
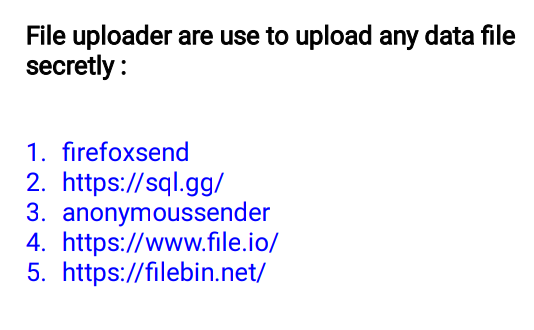
🖤File Uploader
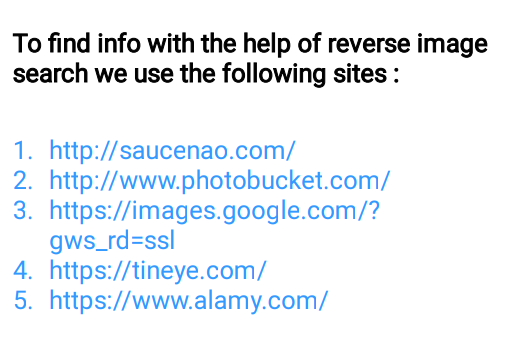
🖤Reverse Image Search
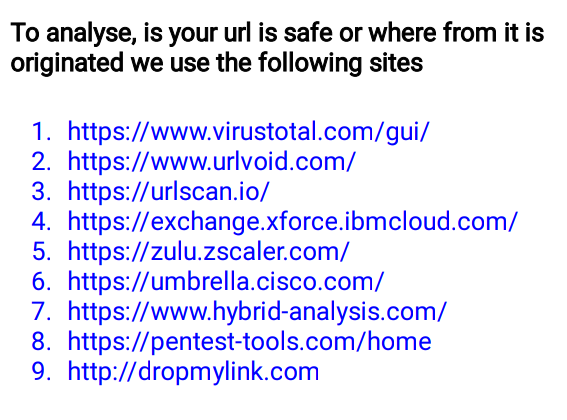
🖤URL Analysis
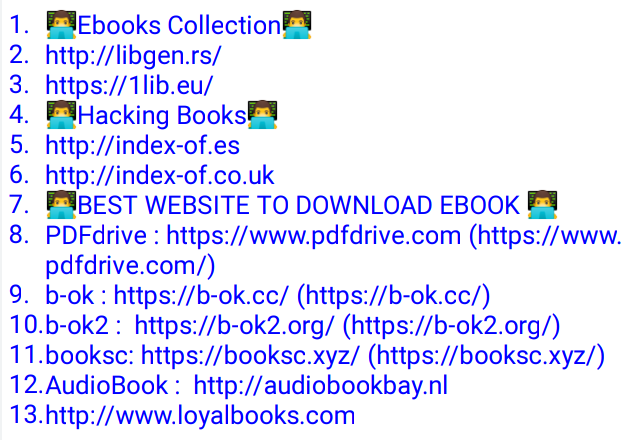
🖤Ebooks and PDFs
🖤Fake Mails
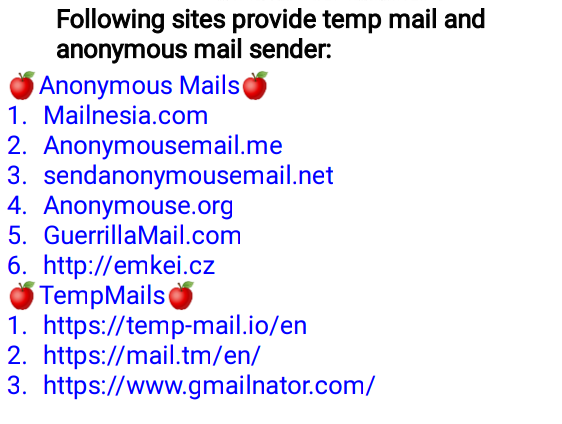
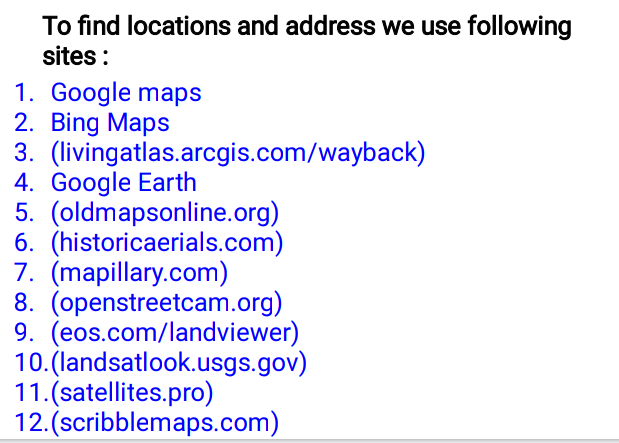
🖤Maps Data
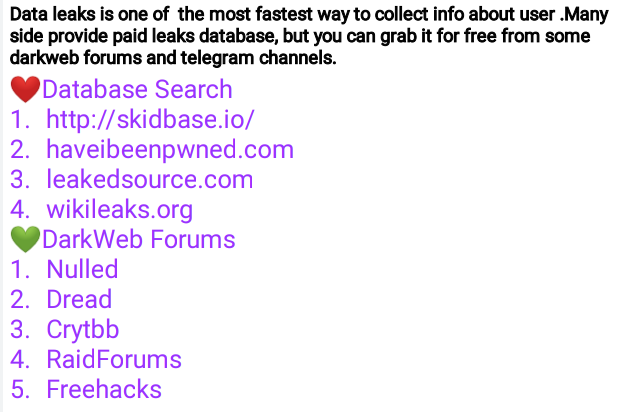
🖤Data Leaks
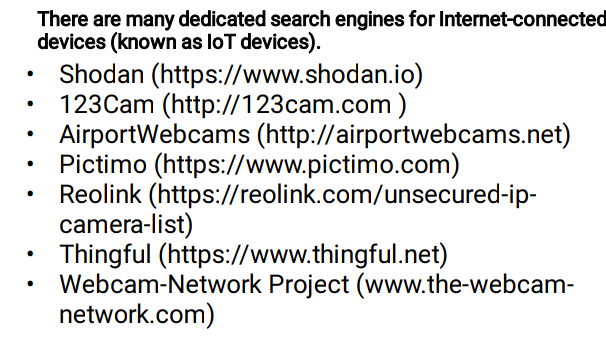
🖤IOT Search Engines
How to clear your tracks?
While doing doxing don't forget to use vpn,and proxies . Some tools that will help you remove your searches
❤️🔥 Data Destruction Tools
DBAN https://dban.org
The free version supports HDD only.
Eraser www.heidi.ie/eraser/ Open source; supports SSD.
CCleaner www.piriform.com/ccleaner Drive wiper and Windows trace cleaner.
SDelete https://technet.microsoft.com/
en-us/sysinternals/sdelete.aspx
Erases data according to DOD 5220.22-M.
❤️🔥 SSD Data-Erasing Tools
Tool URL
Intel Solid State Drive Toolbox https://downloadcenter.intel.com/download/26574?v=t
Corsair SSD Toolbox www.corsair.com/en-eu/support/downloads
Samsung Magician www.samsung.com/semiconductor/minisite/ssd/download/tools.html
SanDisk SSD https://kb.sandisk.com/app/answers/detail/a_id/16678/~/secure-erase-and-sanitize
How can I protect myself from Doxing?
- Adjust your social media settings:Ensure that your profiles, usernames/handles are kept private
- Remove any addresses, places of work, and specific locations from your accounts
- Set your posts to “friends only"
- Avoid discussing personal information that could be used against you, as well as anything that can identify your address, workplace or contact information
- Use a Virtual Private Network (VPN) and aIf you must use public wi-fi, turn off the public network sharing functionality on your device
- Use strong passwords
- Vary usernames and passwords across platforms
- Hide domain registration information from WHOIS (a database of all registered domain names on the web)
- Don't be afraid after getting doxed its your publicly shared information, so don't worry about it, otherwise attacker use you, don't pay money if you get doxed.
- Be Safe From Cat Phishing
Join CIDHUB For More Knowledge
Is doxing is Illegal ?
Doxxing is immoral and illegal, and if you are discovered bothering individuals and disclosing their personal information, you could face serious legal consequences, including imprisonment. Detecting and prosecuting these types of crimes is often challenging for law enforcement.In India you get punishment under IT ACT 2000 for doxing or identity theft.
What is legal Way of Doxing ?
We can say that Open Source Intelligence is the legal way of Doxing.
Intelligence agencies use OSINT to track events, equipment such as weapons systems, and people. These are the 'targets of interest' (ToIs). But hackers use OSINT to identify technical vulnerabilities as well as human targets for phishing and social engineering attacks.Law Firms. Lawyers and private investigators can ethically and legally utilize OSINT techniques – especially information found on social media platforms – in legal and litigation intelligence to collect evidence and research about any suspect or potential juror.
If you are interested to learn advance level open source intelligence and ethical hacking check Here.