The Idea of dns multiplexing in other side
AnonymousDuring my observation of DNS network traffic passing through a firewall, I noticed an interesting pattern: the firewall initially allows the first packet in DNS tunneling to pass, but eventually, the Deep Packet Inspection (DPI) system detects the unusual traffic behavior and blocks it. A potential solution to bypass this restriction, with added noise and fewer limitations on DNS server IPs, is the DNS multiplexing technique.
Let me walk you through the traditional approach that often gets blocked:
Traditional Approach (Blocked by DPI):
- Client sends a DNS request to a less restricted DNS server.
- The request reaches the ISP firewall, where various checks occur. Most restrictions and traffic filtering happen at the ISP level, as we observed.
- If it passes the ISP firewall, the request is forwarded to the infrastructure firewall. Further checks are done here before proceeding.
- Note: Points 2 and 3 may be handled by the same physical server or infrastructure, but we treat them as separate based on the distinct behaviors they exhibit during packet inspection.
- If the packet passes through all of these checks without being blocked, it can finally reach the DNS server and, ultimately, your intended tunnel server.
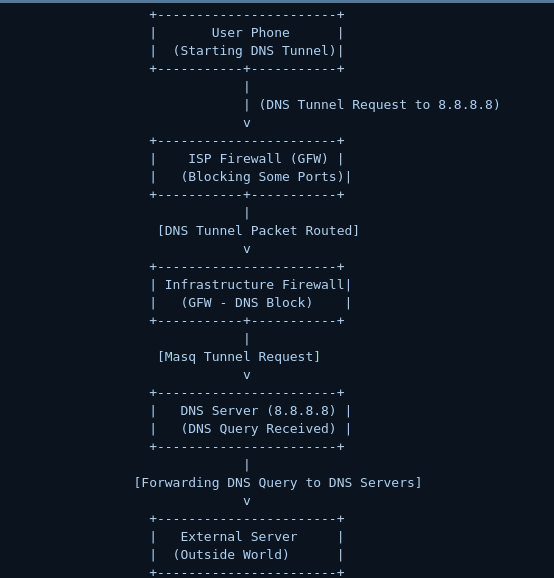
Issues with the Traditional Flow:
- Limited Access to DNS Servers: One of the key challenges is that there are fewer open DNS servers available with mobile ISPs these days. ISPs may block access to external DNS servers, limiting your ability to tunnel through these servers when the internet cuts off. Once that happens, it becomes your problem to figure out alternative routes.
Slow Speed: DNS traffic is often heavily throttled or blocked, which results in slower speeds. There's a limited ability to send DNS requests without triggering network filters or having your IP blocked by public DNS servers.
Solution: DNS Multiplexing Using a Middle Proxy
From the documents we've gathered, we found that datacenters tend to have much fewer restrictions on DNS traffic compared to mobile ISPs. Many government and local infrastructure services rely on public DNS servers located outside the country. This gives us an opportunity to leverage these external DNS servers in a more effective way.
The idea is as follows:
How DNS Multiplexing Works:
We tested a simple setup using dnsmasq as a forward proxy, coupled with multiple public servers and a client. The concept is to send your DNS request to a datacenter, which acts as a middle proxy that multiplexes the request over multiple servers (as many as needed). All these requests go through a single firewall—one that is far less restrictive than mobile ISP firewalls.
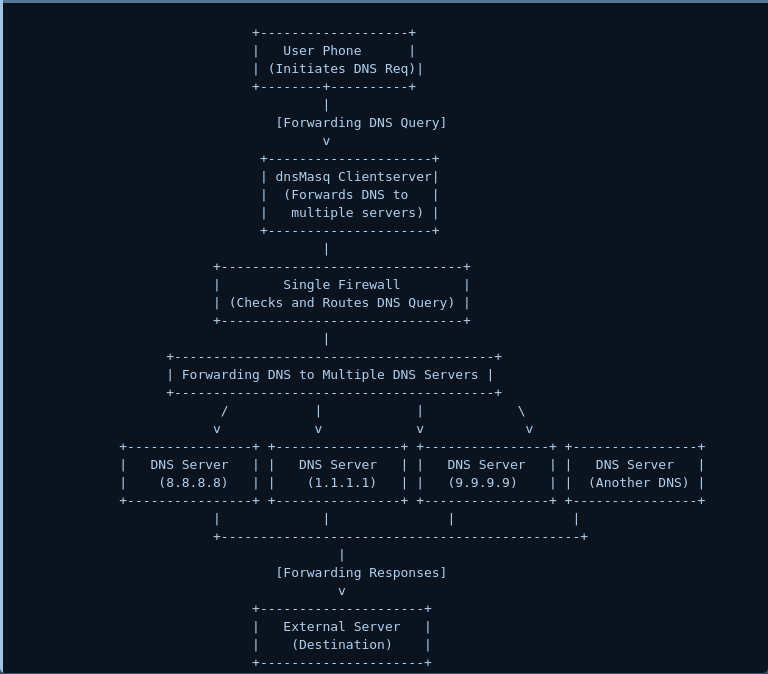
Advantages of This Approach:
- Higher Availability of DNS Servers: In our tests, we found that datacenters offer many more open and less restricted DNS servers compared to mobile ISPs.
- Greater Flexibility: With DNS multiplexing, you have more freedom to customize your DNS requests. You can introduce noise, padding, or other techniques to make your traffic appear more benign and harder to detect.
Increased Privacy and Anonymity: Because your DNS requests are routed through multiple servers, they take different paths, making it much more difficult for DPI systems to detect and block them. This results in reduced visibility and enhanced anonymity for the user.
By using DNS multiplexing through datacenters and middle proxies, you gain much more control over your DNS traffic, improve speed, and bypass many of the common restrictions found in mobile ISPs.