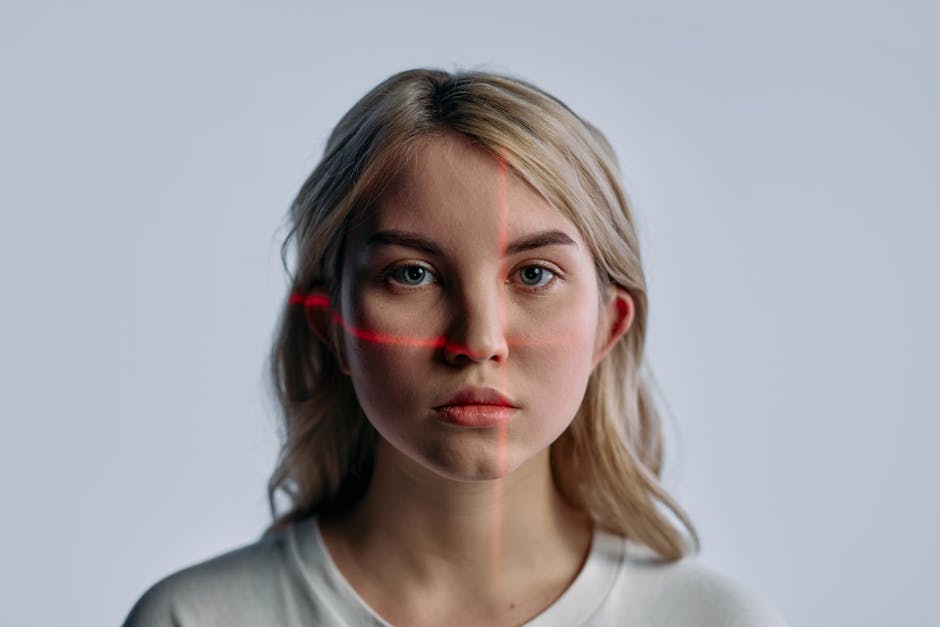
The CEO Voice Note Trap: Why "Detection" Is Only Half the Battle
You’re sitting in the SOC on a Tuesday afternoon when a frantic message lands in your inbox. It’s an urgent voice note from the CEO, directed at the CFO. The request? An immediate, "off-the-books" transfer for an acquisition that nobody in the M&A department has ever heard of. The voice sounds perfect. It has the same cadence, the same slight rasp in his throat, and the same annoying tendency to trail off at the end of sentences.
Ten years ago, we’d call this vishing. Today, we call it a nightmare. As an analyst who spent four years watching call centers bleed money to social engineering, I can tell you that the attackers have stopped trying to sound like humans and started training machines to mimic them flawlessly.
According to McKinsey 2024: over 40% of organizations encountered at least one AI-generated audio attack or scam in the past year. That is not a marginal increase; that is a fundamental shift in the threat landscape. If your organization doesn't have a strategy for validating a suspicious voice note, you are effectively running an open-door policy for attackers.
The First Question: "Where Does the Audio Go?"Before you even think about installing a deepfake detector or plugging that audio file into an API, stop. Ask yourself the most important question in security architecture: Where does the audio go?
If you upload that voice note to a "free" cloud-based detector to see if it’s fake, you’ve likely just handed an encrypted, verified, and high-fidelity sample of your CEO’s voice to an unknown third party. If that detector is being run by a startup in an unregulated jurisdiction, your CEO’s biometric signature is now part of their training set. Congratulations, you’ve just helped the attackers build a better deepfake for the next round.
In enterprise incident response, we treat audio files like sensitive PII. If the tool processes data in the cloud, you need a Data Processing Agreement (DPA) and a clear understanding of the data retention policy. If the vendor says they "anonymize" data, demand to see the technical spec. If they can’t prove the audio is purged from RAM and disk immediately after the forensic analysis, don't use it.
Detection Tool Categories: Beyond the Marketing FluffWhen you start shopping for a deepfake detector, you will see a lot of "99.9% accuracy" claims. Ignore them. Those percentages are usually generated in labs on clean, high-bitrate studio audio—not the compressed, noisy, background-cluttered nightmare that actually arrives in your corporate Slack or WhatsApp.
Here is how the current market breaks down, and what you need to know about the trade-offs:
Category Privacy Risk Analysis Speed Best Use Case Cloud APIs High (Data leaves your perimeter) Medium High-volume automated screening Browser Extensions Very High (Hooks into your browser) Fast Consumer-level protection On-Device/Client-Side Low (Audio stays local) Slow (Hardware dependent) On-Prem Forensics Lowest (Air-gapped) Variable Sensitive CEO fraud investigation The Checklist for "Bad Audio": Why Tools FailIf you trust a detector blindly, you will get burned. Detectors look for artifacts—the digital "fingerprints" left by the Generative Adversarial Network (GAN) or the diffusion model. However, real-world audio destroys these fingerprints. Before you run a file, check for these "bad audio" edge cases that render most detectors useless:
Transcoding Artifacts: Was the audio recorded on an iPhone, sent over WhatsApp, then re-recorded on a PC? Every time audio is re-encoded, the forensic noise is stripped away. Codec Noise: Low-bitrate compression (like what you find in VOIP or instant messengers) acts as a lossy filter. It hides the very inconsistencies that detection algorithms look for. Background "Canned" Noise: Attackers now add "authenticity noise"—the sound of a busy office, a hum of an AC, or distant traffic—to mask the metallic or robotic glitches of AI generation. Frequency Clipping: Does the audio sound like it was recorded in a tin can? Clipping destroys the high-frequency metadata where most AI models show their work.If you encounter any of these, a detector will likely return a "false negative" (labeling a deepfake as "Real"). Never accept a "Real" result at face value if the audio quality is degraded. Treat that "Real" result as "Inconclusive."
Accuracy Claims: A Word of CautionI hate marketing claims that say "99% accuracy" without mentioning the conditions. It’s intellectually dishonest. An accuracy claim is meaningless without context. For example, "99% accuracy on 48kHz WAV files" is a vastly different statement than "99% accuracy on WhatsApp-compressed OGG files."

In my work, I ignore the aggregate accuracy score. I focus on the False Acceptance Rate (FAR). In our field, a false positive is annoying (we have to double-check). A false negative (trusting a fake) is catastrophic. When evaluating a tool, ask the vendor for their FAR under degraded network conditions. If they don't have that data, they aren't selling a security tool; they’re selling a placebo.
Real-Time vs. Batch Analysis: The Tactical DifferenceShould you use a detector in real-time? That depends on your threat model. If you are dealing with a live vishing call, you don't have time to run a 30-second forensic batch analysis. You need instantaneous feedback. But real-time detection is inherently less accurate because the model has less data to work with.
For an urgent CEO fraud attempt, use a two-tier approach:
Click here Immediate Heuristic Screen: Run the audio through an on-device local script that flags obvious spectral inconsistencies. If it hits, kill the transfer request immediately. Deep Forensic Batch Analysis: If the heuristic screen is inconclusive, send the file for a deeper, multi-pass analysis. This takes time, but accuracy increases exponentially when you can run a full pass-through of the file. The Safest Way: Secondary VerificationHere is the hard truth: There is no "Golden Bullet" detector. Technology will never fully replace human verification in a high-stakes environment. If you receive a suspicious voice note, treat it as a "medium-confidence" indicator, never as proof.
The only truly safe way to verify a request involving financial transactions is through secondary verification. If the request comes via a voice note or a phone call, you must switch channels.
Set these rules for your organization today:
Challenge Protocol: If the CEO calls with an urgent request, the recipient must have a "challenge phrase"—a pre-agreed-upon piece of information or a specific question that a deepfake wouldn't know the answer to. Channel Switch: If a voice note arrives, the response must never be a reply to that message. The recipient must initiate a new, separate communication channel—such as an internal encrypted messaging app or a video call—to verify the request. Out-of-Band Authorization: For any transfer above a set threshold, the voice request is merely an "information trigger." It must be followed by a formal, multi-party authorization process that is independent of the audio request.At the end of the day, detection https://instaquoteapp.com/background-noise-and-audio-compression-will-your-deepfake-detector-fail/ software is just another tool in your kit. It's not a decision-maker. It’s a traffic light. Sometimes, it stays green when it should be red. Always keep your eyes on the road. Don't trust the AI; trust your process.