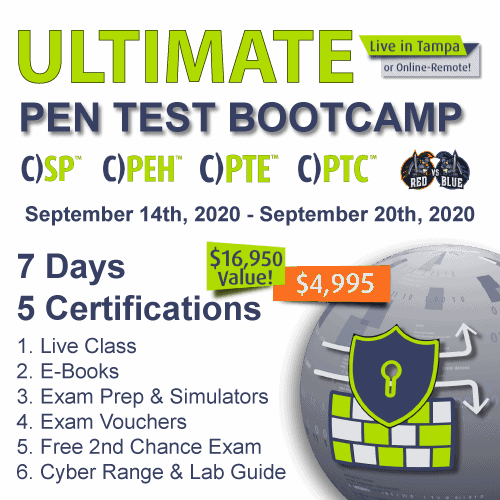
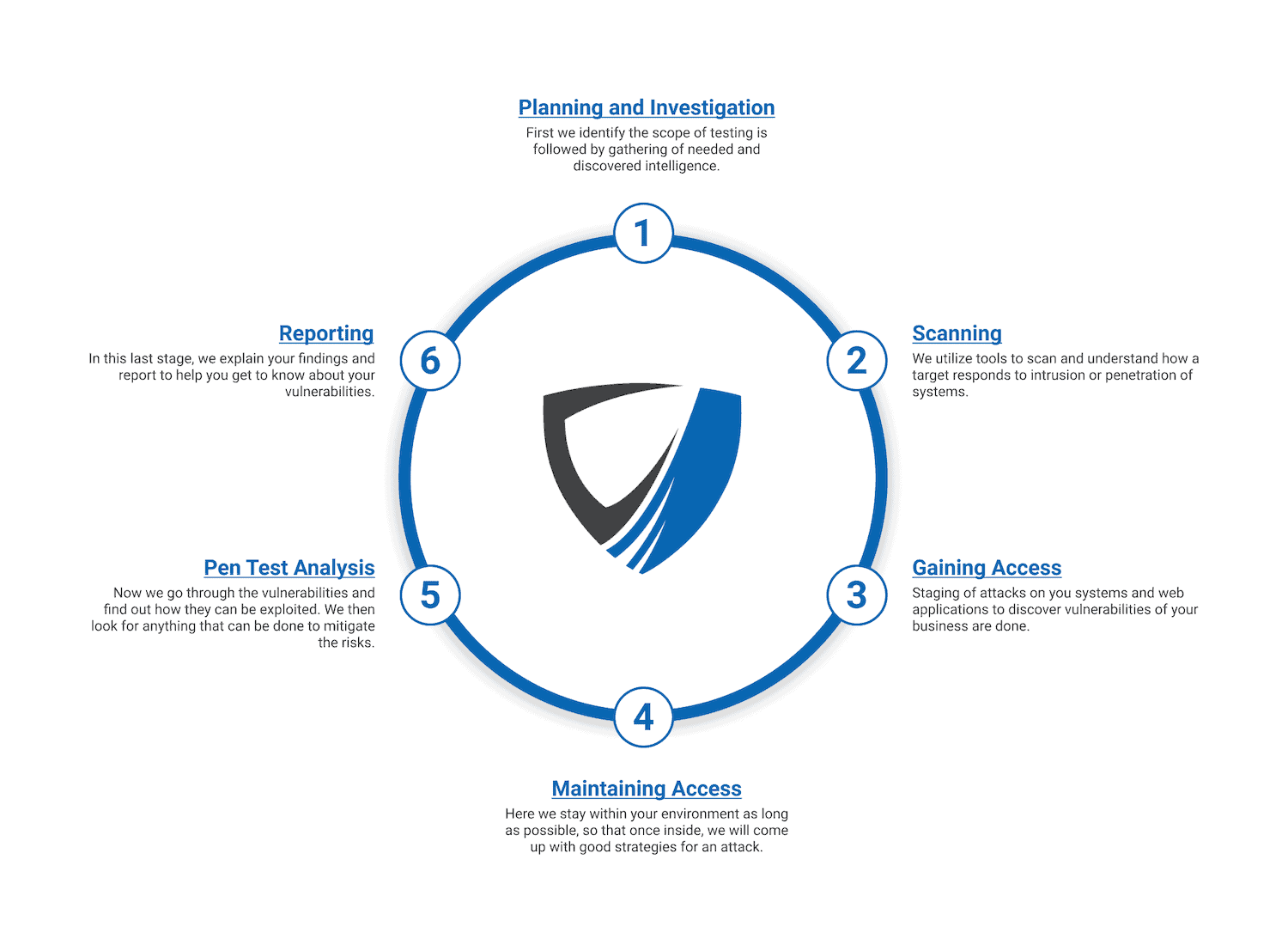
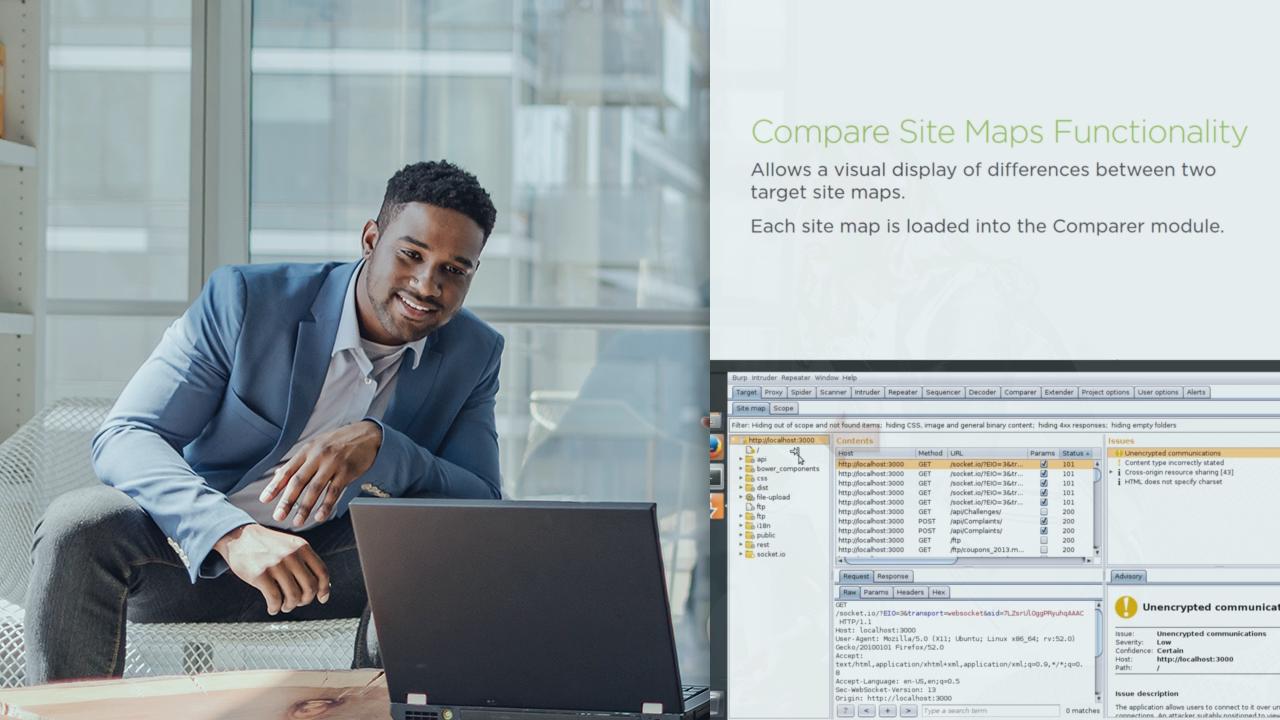
Tampa penetration testing

🛑 👉🏻👉🏻👉🏻 FOR MORE INFORMATION, CLICK HERE 👈🏻👈🏻👈🏻
Big Chubby Girls Anal Porno
Videoskaseros.Com
Rollin Thunda Feat. Jada Stevens
Kendra pierced pussy
Fucking and creampie for my hot wife
Mom Fucked Son Video Online
South african camgirl spreading thick pussy photo
Tampa penetration testing

































204">203">200_.jpg">








































.jpg.aspx)