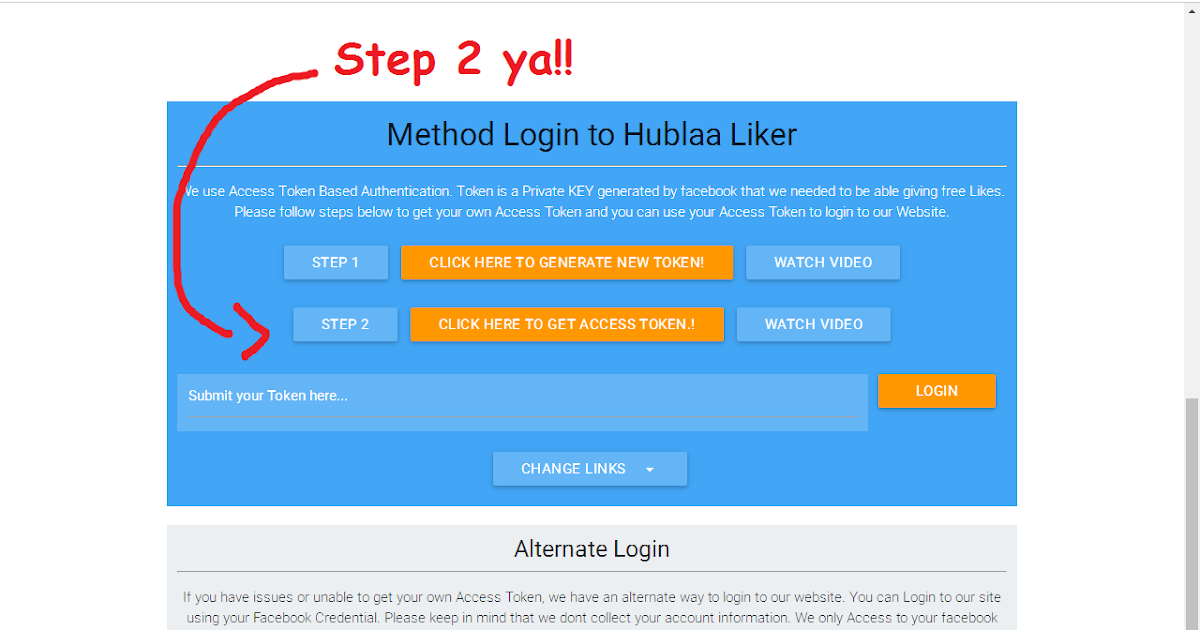
Private Token
⚡ ALL INFORMATION CLICK HERE 👈🏻👈🏻👈🏻
Private Token
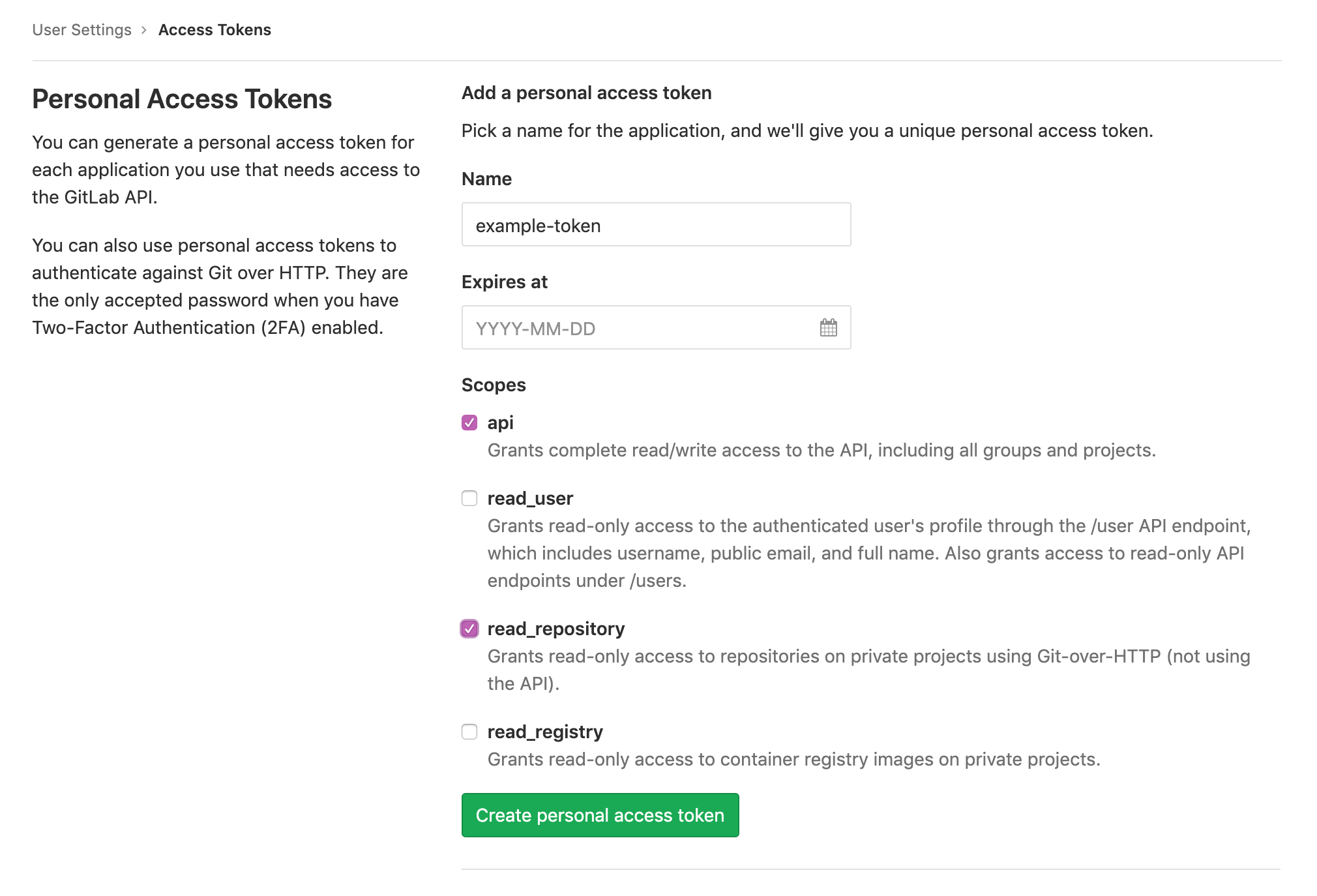
Automate GitLab via a simple and powerful API. All definitions can be found
under /lib/api .
Documentation for various API resources can be found separately in the
following locations:
Going forward, we will start on moving to
GraphQL and deprecate the use of
controller-specific endpoints. GraphQL has a number of benefits:
It will co-exist with the current v4 REST API. If we have a v5 API, this should
be a compatibility layer on top of GraphQL.
Although there were some patenting and licensing concerns with GraphQL, these
have been resolved to our satisfaction by the relicensing of the reference
implementations under MIT, and the use of the OWF license for the GraphQL
specification.
API requests should be prefixed with api and the API version. The API version
is defined in lib/api.rb . For example, the root of the v4 API
is at /api/v4 .
Example of a valid API request using cURL:
The API uses JSON to serialize data. You don't need to specify .json at the
end of an API URL.
Most API requests require authentication, or will only return public data when
authentication is not provided. For
those cases where it is not required, this will be mentioned in the documentation
for each individual endpoint. For example, the /projects/:id endpoint .
There are three ways to authenticate with the GitLab API:
For admins who want to authenticate with the API as a specific user, or who want to build applications or scripts that do so, two options are available:
If authentication information is invalid or omitted, an error message will be
returned with status code 401 :
You can use an OAuth2 token to authenticate with the API by passing it in either the
access_token parameter or the Authorization header.
Example of using the OAuth2 token in a parameter:
Example of using the OAuth2 token in a header:
You can use a personal access token to authenticate with the API by passing it in either the
private_token parameter or the Private-Token header.
Example of using the personal access token in a parameter:
Example of using the personal access token in a header:
When signing in to the main GitLab application, a _gitlab_session cookie is
set. The API will use this cookie for authentication if it is present, but using
the API to generate a new session cookie is currently not supported.
The primary user of this authentication method is the web frontend of GitLab itself,
which can use the API as the authenticated user to get a list of their projects,
for example, without needing to explicitly pass an access token.
Introduced in GitLab 9.0. Needs admin permissions.
Impersonation tokens are a type of personal access token
that can only be created by an admin for a specific user. They are a great fit
if you want to build applications or scripts that authenticate with the API as a specific user.
They are an alternative to directly using the user's password or one of their
personal access tokens, and to using the Sudo feature, since the user's (or admin's, in the case of Sudo)
password/token may not be known or may change over time.
For more information, refer to the
users API docs.
Impersonation tokens are used exactly like regular personal access tokens, and can be passed in either the
private_token parameter or the Private-Token header.
All API requests support performing an API call as if you were another user,
provided you are authenticated as an administrator with an OAuth or Personal Access Token that has the sudo scope.
You need to pass the sudo parameter either via query string or a header with an ID/username of
the user you want to perform the operation as. If passed as a header, the
header name must be Sudo .
If a non administrative access token is provided, an error message will
be returned with status code 403 :
If an access token without the sudo scope is provided, an error message will
be returned with status code 403 :
If the sudo user ID or username cannot be found, an error message will be
returned with status code 404 :
Example of a valid API call and a request using cURL with sudo request,
providing a username:
Example of a valid API call and a request using cURL with sudo request,
providing an ID:
The API is designed to return different status codes according to context and
action. This way, if a request results in an error, the caller is able to get
insight into what went wrong.
The following table gives an overview of how the API functions generally behave.
The following table shows the possible return codes for API requests.
Sometimes the returned result will span across many pages. When listing
resources you can pass the following parameters:
In the example below, we list 50 namespaces per page.
Link headers are sent back with each
response. They have rel set to prev/next/first/last and contain the relevant
URL. Please use these links instead of generating your own URLs.
In the cURL example below, we limit the output to 3 items per page ( per_page=3 )
and we request the second page ( page=2 ) of comments of the issue
with ID 8 which belongs to the project with ID 8 :
Additional pagination headers are also sent back.
If using namespaced API calls, make sure that the NAMESPACE/PROJECT_NAME is
URL-encoded.
For example, / is represented by %2F :
If your branch or tag contains a / , make sure the branch/tag name is
URL-encoded.
For example, / is represented by %2F :
When you work with the API, you may notice two similar fields in API entities:
id and iid . The main difference between them is scope.
For example, an issue might have id: 46 and iid: 5 .
That means that if you want to get an issue via the API you should use the id :
On the other hand, if you want to create a link to a web page you should use
the iid :
When working with the API you may encounter validation errors, in which case
the API will answer with an HTTP 400 status.
When an attribute is missing, you will get something like:
When a validation error occurs, error messages will be different. They will
hold all details of validation errors:
This makes error messages more machine-readable. The format can be described as
follows:
When you try to access an API URL that does not exist you will receive 404 Not Found.
If you need to include a + in a query parameter, you may need to use %2B instead due
a W3 recommendation that
causes a + to be interpreted as a space. For example, in an ISO 8601 date, you may want to pass
a time in Mountain Standard Time, such as:
The correct encoding for the query parameter would be:
There are many unofficial GitLab API Clients for most of the popular
programming languages. Visit the GitLab website for a complete list.
Access one or more resources and return the result as JSON.
Return 201 Created if the resource is successfully created and return the newly created resource as JSON.
Return 200 OK if the resource is accessed or modified successfully. The (modified) result is returned as JSON.
Returns 204 No Content if the resuource was deleted successfully.
The GET , PUT or DELETE request was successful, the resource(s) itself is returned as JSON.
The server has successfully fulfilled the request and that there is no additional content to send in the response payload body.
The POST request was successful and the resource is returned as JSON.
Indicates that the resource has not been modified since the last request.
A required attribute of the API request is missing, e.g., the title of an issue is not given.
The user is not authenticated, a valid user token is necessary.
The request is not allowed, e.g., the user is not allowed to delete a project.
A resource could not be accessed, e.g., an ID for a resource could not be found.
A conflicting resource already exists, e.g., creating a project with a name that already exists.
Indicates the request was denied. May happen if the If-Unmodified-Since header is provided when trying to delete a resource, which was modified in between.
While handling the request something went wrong server-side.
Number of items to list per page (default: 20 , max: 100 )
The index of the current page (starting at 1)
Is unique across all issues and is used for any API call
Is unique only in scope of a single project. When you browse issues or merge requests with the Web UI, you see the iid
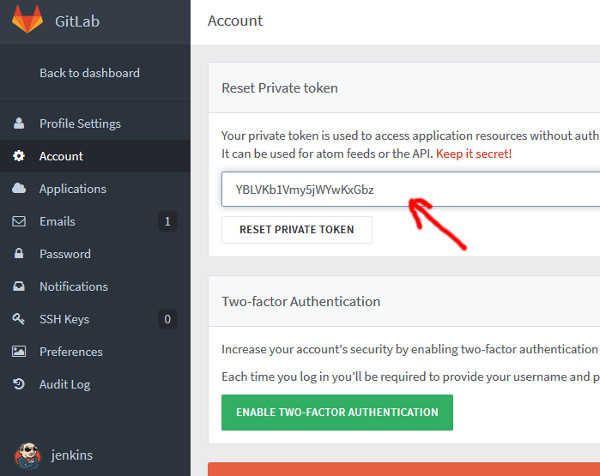
curl - Gitlab API: How to generate the private token - Stack Overflow
Readme · Api · Help · GitLab | Personal access tokens
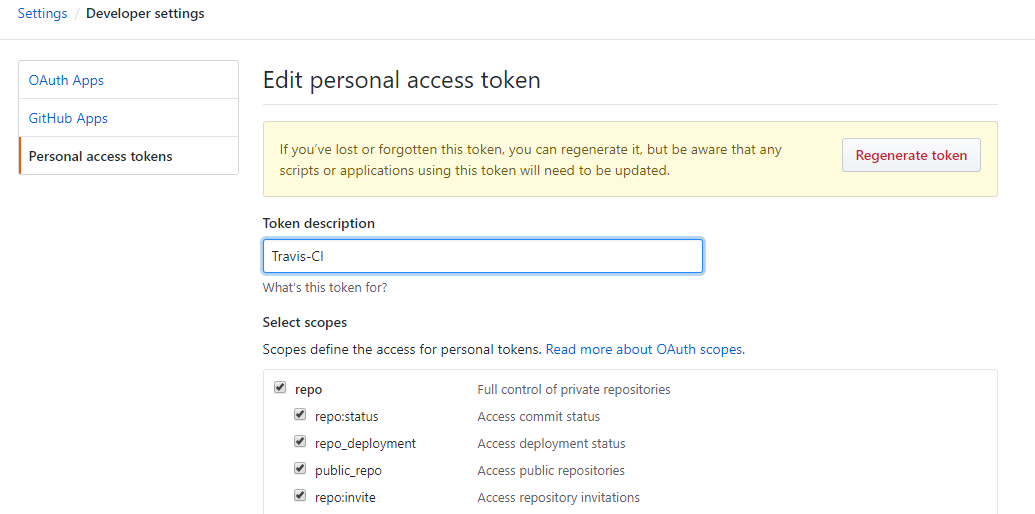
Creating a personal access token - GitHub Docs
Readme · Api · Help · GitLab | Private tokens
Readme · Api · Help · GitLab | GitLab CI job token
In this article
Creating a token
Using a token on the command line
Further reading
© 2021 GitHub, Inc.
Terms
Privacy
Security
Status
Help
Contact GitHub
Pricing
Developer API
Training
About
You should create a personal access token to use in place of a password with the command line or with the API.
Personal access tokens (PATs) are an alternative to using passwords for authentication to GitHub when using the GitHub API or the command line .
If you want to use a PAT to access resources owned by an organization that uses SAML SSO, you must authorize the PAT. For more information, see " About authentication with SAML single sign-on " and " Authorizing a personal access token for use with SAML single sign-on ."
As a security precaution, GitHub automatically removes personal access tokens that haven't been used in a year.
Verify your email address , if it hasn't been verified yet.
In the upper-right corner of any page, click your profile photo, then click Settings .
In the left sidebar, click Developer settings .
In the left sidebar, click Personal access tokens .
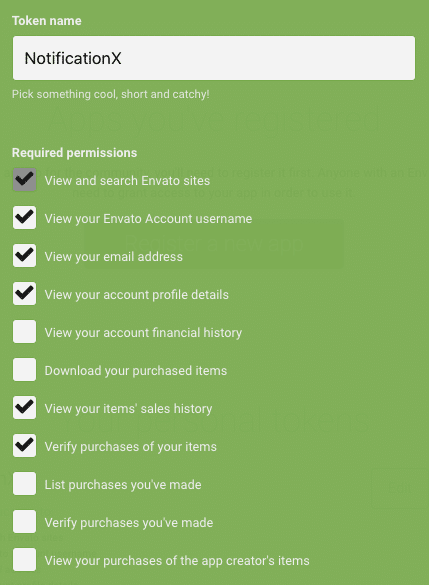
Give your token a descriptive name.
Select the scopes, or permissions, you'd like to grant this token. To use your token to access repositories from the command line, select repo .
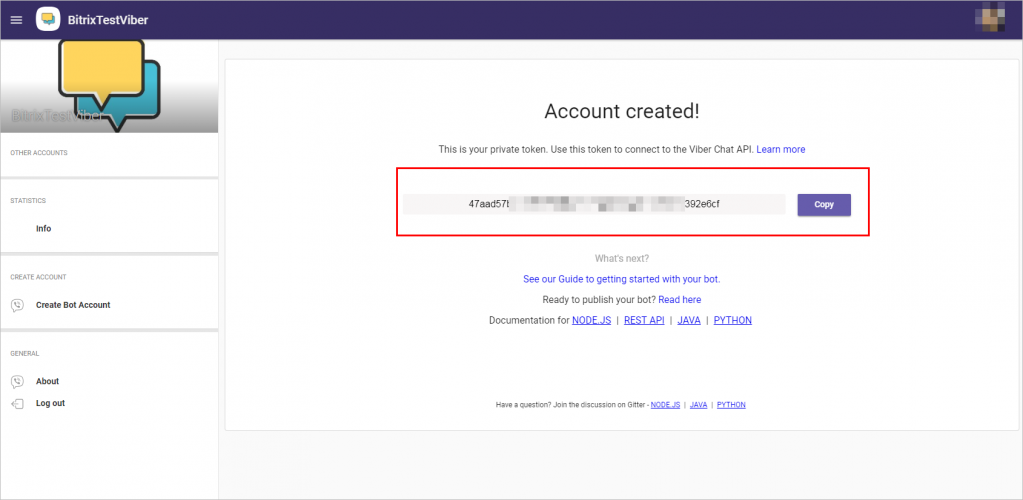
Click to copy the token to your clipboard. For security reasons, after you navigate off the page, you will not be able to see the token again.
Warning: Treat your tokens like passwords and keep them secret. When working with the API, use tokens as environment variables instead of hardcoding them into your programs.
To use your token to authenticate to an organization that uses SAML SSO, authorize the token for use with a SAML single-sign-on organization .
Once you have a token, you can enter it instead of your password when performing Git operations over HTTPS.
For example, on the command line you would enter the following:
Personal access tokens can only be used for HTTPS Git operations. If your repository uses an SSH remote URL, you will need to switch the remote from SSH to HTTPS .
If you are not prompted for your username and password, your credentials may be cached on your computer. You can update your credentials in the Keychain to replace your old password with the token.
Can we contact you if we have more questions?
Optional
All GitHub docs are open source. See something that's wrong or unclear? Submit a pull request.
Family Nudist Seks
Victorinox Outdoor Master Mic
Outdoor Porn Gif
Long Pee Girl Porn
Junior Retro Nudist Foto
:filters:format(jpeg)/f/39898/2550x1646/ec9bec33e6/storyblok-2018-05-16-11-13-20-1.jpg)




















.png)