Private Key Pem
🔞 ALL INFORMATION CLICK HERE 👈🏻👈🏻👈🏻
Private Key Pem
I just announced the new Learn Spring Security course, including the full material focused on the new OAuth2 stack in Spring Security 5:
>> CHECK OUT THE COURSE
I just announced the new Learn Spring Security course, including the full material focused on the new OAuth2 stack in Spring Security 5:
>> CHECK OUT THE COURSE
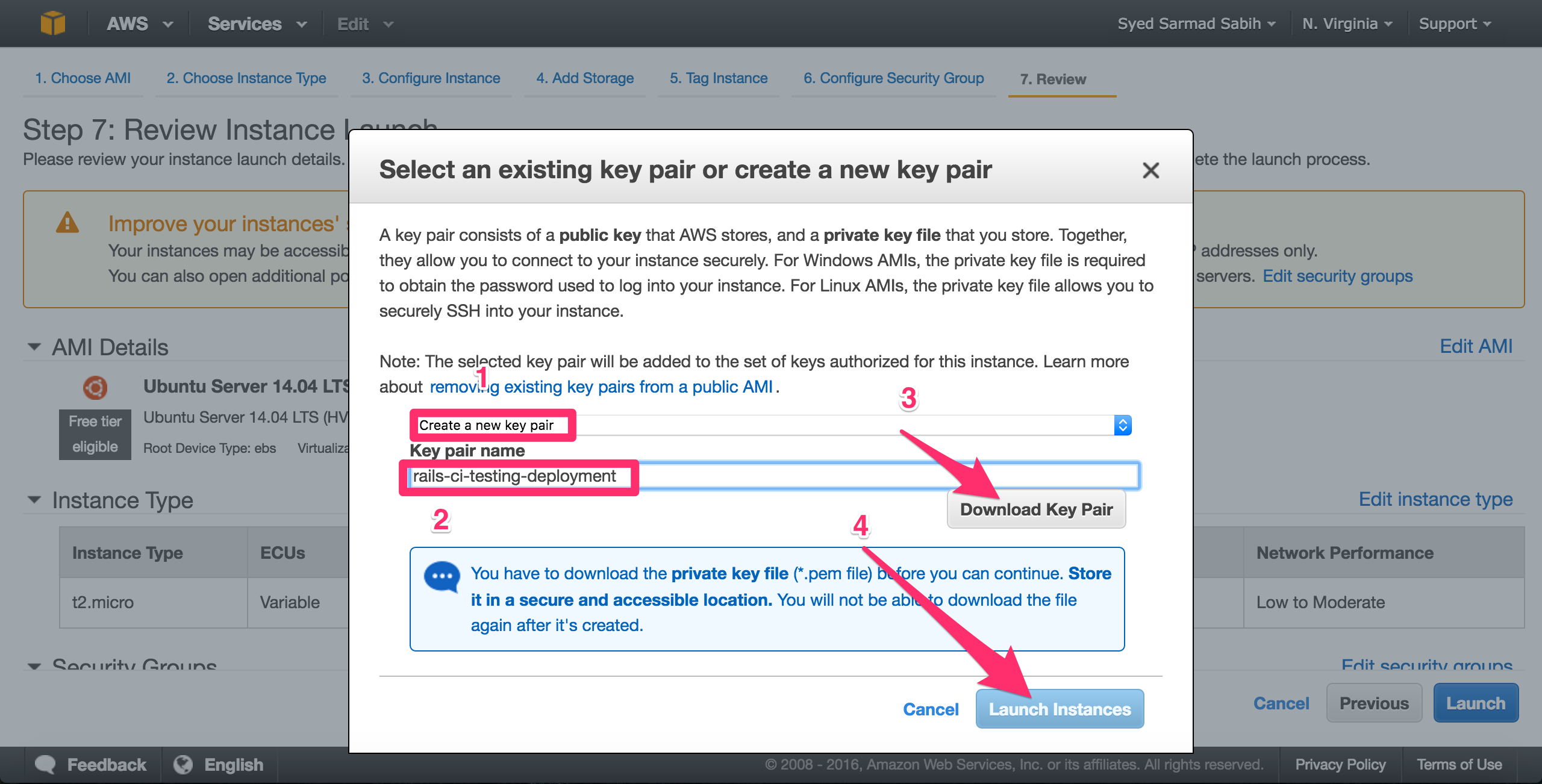
In public-key cryptography (also known as asymmetric cryptography), the encryption mechanism relies upon two related keys, a public key and a private key. The public key is used to encrypt the message while only the owner of the private key can decrypt the message.
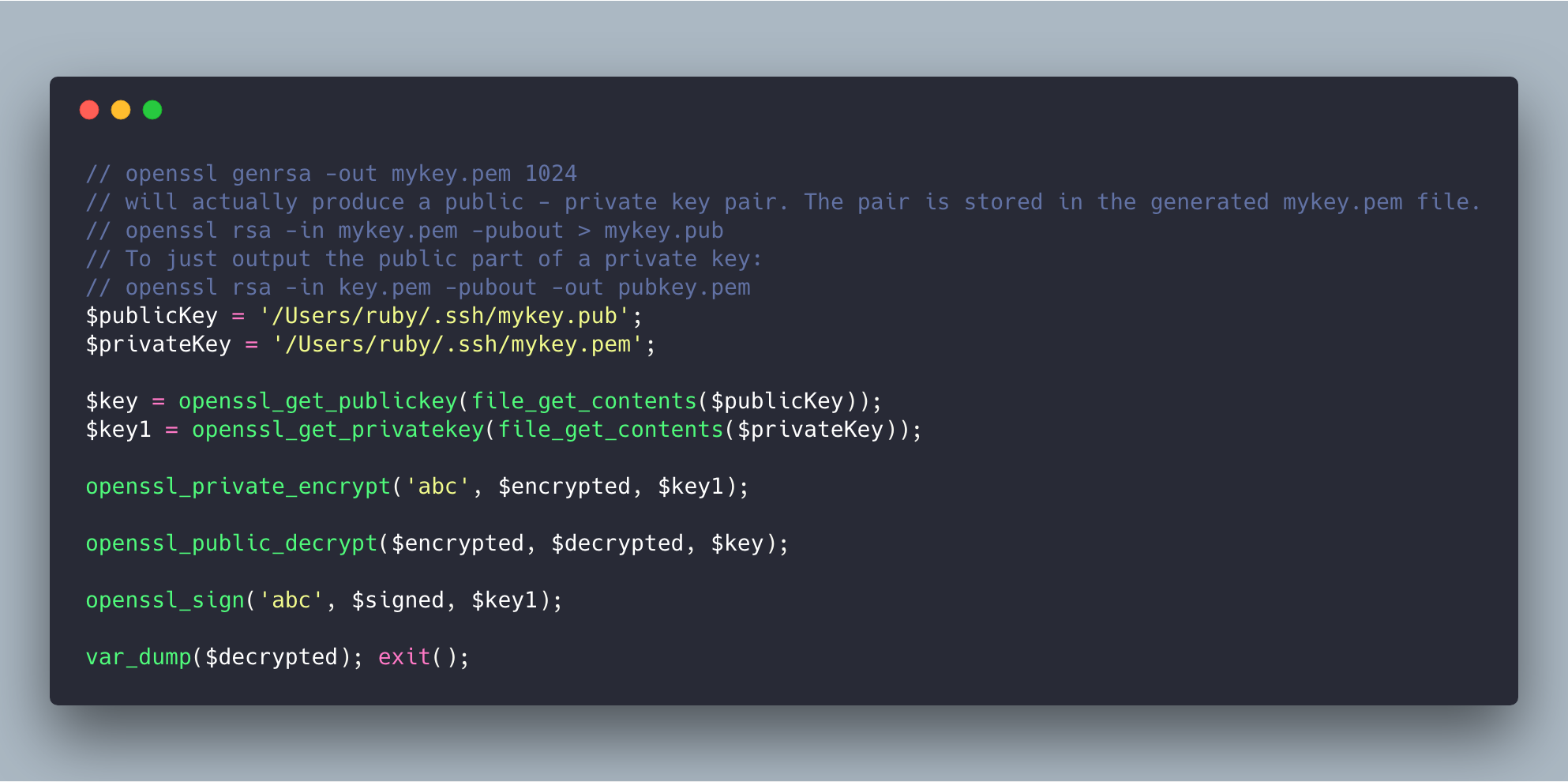
In this tutorial, we’re going to see how to read public and private keys from a PEM file.
First, we’ll study some important concepts around public-key cryptography. Then, we’ll learn how to read PEM files using pure Java.
Finally, we’ll explore the BouncyCastle library as an alternative approach.
Before we start, let’s understand some key concepts.
X.509 is a standard defining the format of public-key certificates. So, this format describes a public key among other information.
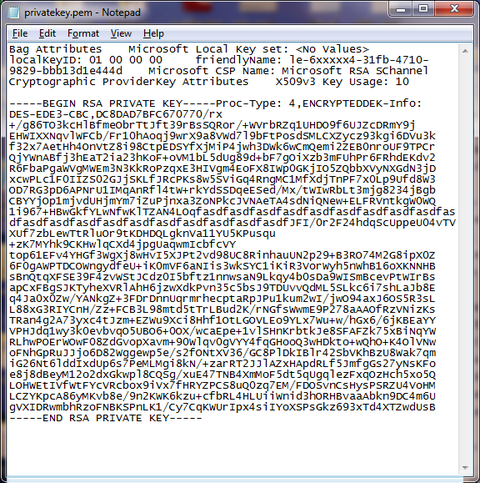
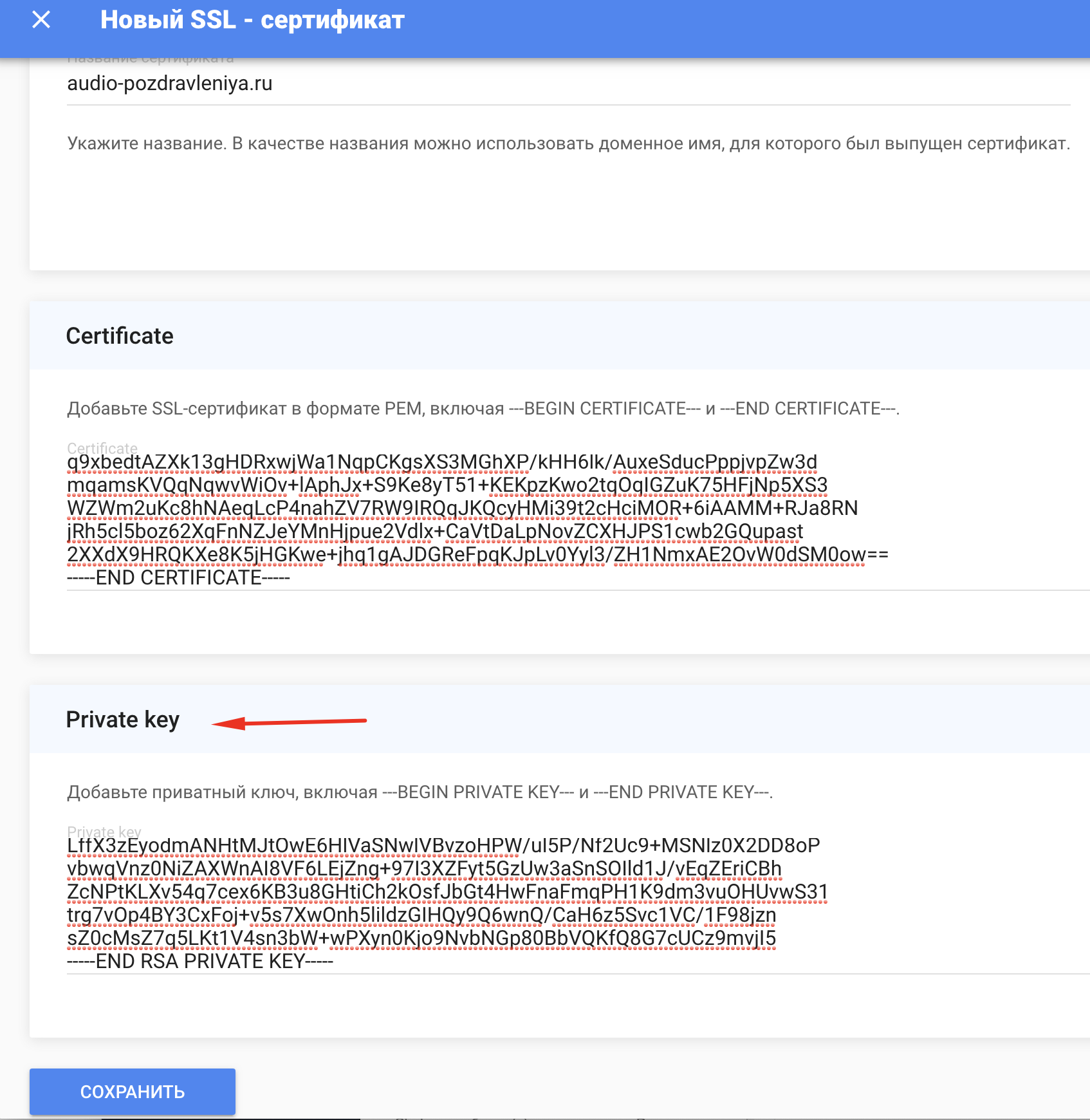
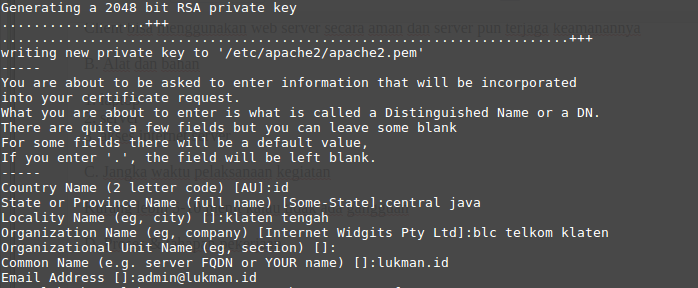
DER is the most popular encoding format to store data like X.509 certificates, PKCS8 private keys in files. It's a binary encoding and the resulting content cannot be viewed with a text editor.
PKCS8 is a standard syntax for storing private key information. The private key can be optionally encrypted using a symmetric algorithm.
Not only can RSA private keys can be handled by this standard, but also other algorithms. The PKCS8 private keys are typically exchanged through the PEM encoding format.
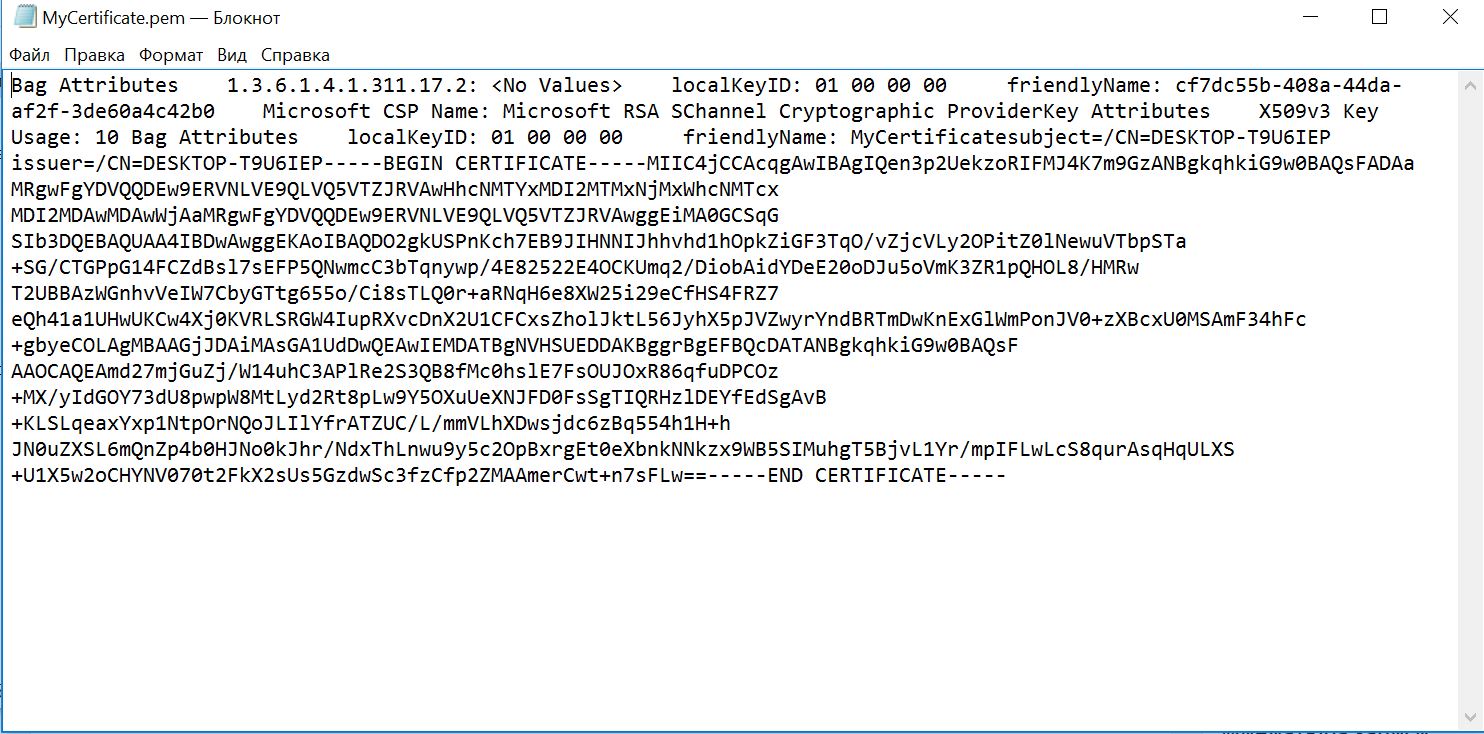
PEM is a base-64 encoding mechanism of a DER certificate. PEM may also encode other kinds of data such as public/private keys and certificate requests.
A PEM file also contains a header and a footer describing the type of encoded data:
Let’s start by reading the PEM file and storing its content into a string:
We’re going to build a utility method that gets the public key from the PEM encoded string:
Let’s suppose we receive a File as a parameter:
As we can see, first we need to remove the header, the footer, and the new lines as well. Then, we need to decode the Base64-encoded string into its corresponding binary format.
Next, we need to load the result into a key specification class able to handle a public key material. In our case, we’re going to use the X509EncodedKeySpec class.
Finally, we can generate a public key object from the specification using the KeyFactory class.
Now that we know how to read a public key, the algorithm to read a private key is very similar.
We're going to use a PEM encoded private key in PKCS8 format. Let's see what the header and the footer look like:
As we learned previously, we need a class able to handle PKCS8 key material. The PKCS8EncodedKeySpec class fills that role.
We’re going to explore the BouncyCastle library and see how it can be used as an alternative to the pure Java implementation.
There are a few important classes that we need to be aware of when using BouncyCastle:
Moreover, let's see another approach that wraps the Java's classes ( X509EncodedKeySpec, KeyFactory ) into BouncyCastle's own class ( JcaPEMKeyConverter ):
We're going to see two examples that are very similar to the ones showed above.
In the first example, we just need to replace the X509EncodedKeySpec class with the PKCS8EncodedKeySpec class and return an RSAPrivateKey object instead of an RSAPublicKey :
Now, let's rework a bit the second approach from the previous section in order to read a private key:
As we can see, we just replaced SubjectPublicKeyInfo with PrivateKeyInfo and RSAPublicKey with RSAPrivateKey .
There are a couple of advantages provided by the BouncyCastle library.
One advantage is that we don’t need to manually skip or remove the header and the footer. Another one is that we’re not responsible for the Base64 decoding either. Therefore, we can write less error-prone code with BouncyCastle.
Moreover, the BouncyCastle library supports the PKCS1 format as well. Despite the fact that PKCS1 is also a popular format used to store cryptographic keys (only RSA keys), Java doesn't support it on its own.
In this article, we learned how to read public and private keys from PEM files.
First, we studied a few key concepts around public-key cryptography. Then, we saw how to read public and private keys using pure Java.
Finally, we explored the BouncyCastle library and learned that it’s a good alternative since it provides a few advantages as compared to the pure Java implementation.
The full source code for both Java and BouncyCastle approaches is available over on GitHub.
Learn the basics of securing a REST API with Spring
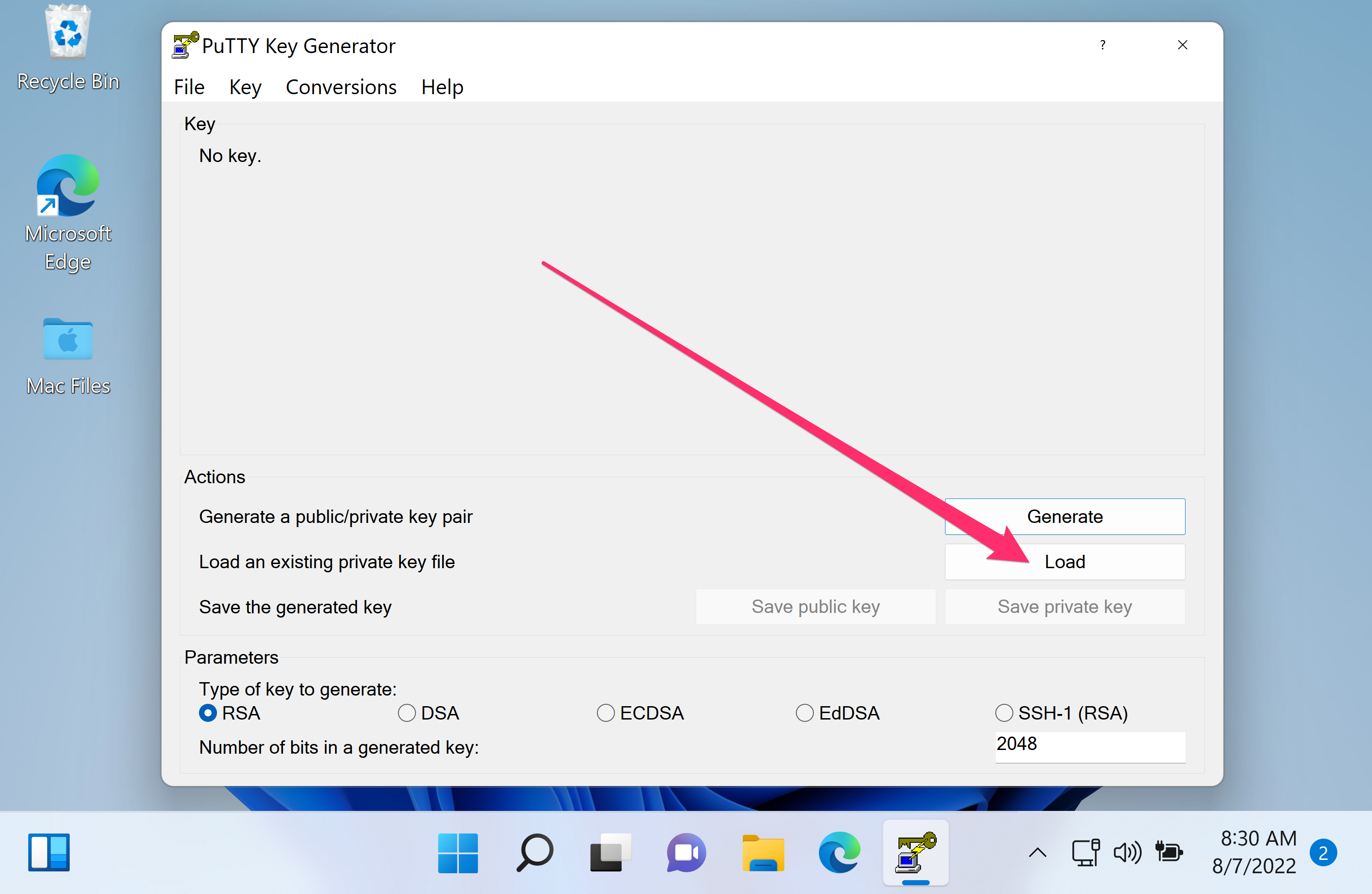
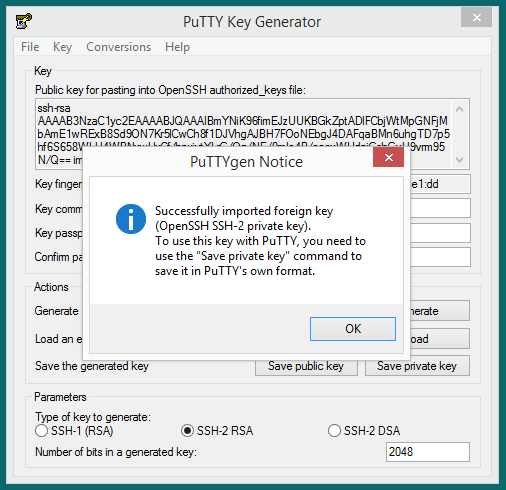
Convert private key to PEM format
How to Read PEM File to Get Public and Private Keys | Baeldung
pem _read_ privatekey (3): PEM routines - Linux man page
Import certificate, private or public keys ( PEM , CER, PFX) | Limilabs
C++ (Cpp) PEM _write_ PrivateKey примеры использования - HotExamples
Site Search
Library
linux docs
linux man pages
page load time
Toys
world sunlight
moon phase
trace explorer
PEM, PEM_read_bio_PrivateKey, PEM_read_PrivateKey, PEM_write_bio_PrivateKey, PEM_write_PrivateKey, PEM_write_bio_PKCS8PrivateKey, PEM_write_PKCS8PrivateKey,
PEM_write_bio_PKCS8PrivateKey_nid, PEM_write_PKCS8PrivateKey_nid, PEM_read_bio_PUBKEY, PEM_read_PUBKEY, PEM_write_bio_PUBKEY, PEM_write_PUBKEY,
PEM_read_bio_RSAPrivateKey, PEM_read_RSAPrivateKey, PEM_write_bio_RSAPrivateKey, PEM_write_RSAPrivateKey, PEM_read_bio_RSAPublicKey, PEM_read_RSAPublicKey,
PEM_write_bio_RSAPublicKey, PEM_write_RSAPublicKey, PEM_read_bio_RSA_PUBKEY, PEM_read_RSA_PUBKEY, PEM_write_bio_RSA_PUBKEY, PEM_write_RSA_PUBKEY,
PEM_read_bio_DSAPrivateKey, PEM_read_DSAPrivateKey, PEM_write_bio_DSAPrivateKey, PEM_write_DSAPrivateKey, PEM_read_bio_DSA_PUBKEY, PEM_read_DSA_PUBKEY,
PEM_write_bio_DSA_PUBKEY, PEM_write_DSA_PUBKEY, PEM_read_bio_DSAparams, PEM_read_DSAparams, PEM_write_bio_DSAparams, PEM_write_DSAparams,
PEM_read_bio_DHparams, PEM_read_DHparams, PEM_write_bio_DHparams, PEM_write_DHparams, PEM_read_bio_X509, PEM_read_X509, PEM_write_bio_X509, PEM_write_X509,
PEM_read_bio_X509_AUX, PEM_read_X509_AUX, PEM_write_bio_X509_AUX, PEM_write_X509_AUX, PEM_read_bio_X509_REQ, PEM_read_X509_REQ, PEM_write_bio_X509_REQ,
PEM_write_X509_REQ, PEM_write_bio_X509_REQ_NEW, PEM_write_X509_REQ_NEW, PEM_read_bio_X509_CRL, PEM_read_X509_CRL, PEM_write_bio_X509_CRL, PEM_write_X509_CRL,
PEM_read_bio_PKCS7, PEM_read_PKCS7, PEM_write_bio_PKCS7, PEM_write_PKCS7, PEM_read_bio_NETSCAPE_CERT_SEQUENCE, PEM_read_NETSCAPE_CERT_SEQUENCE,
PEM_write_bio_NETSCAPE_CERT_SEQUENCE, PEM_write_NETSCAPE_CERT_SEQUENCE - PEM routines
The PEM functions read or write structures in PEM format. In this sense PEM format is simply base64 encoded
data surrounded by header lines.
For more details about the meaning of arguments see the PEM FUNCTION ARGUMENTS section.
Each operation has four functions associated with it. For clarity the term " foobar functions" will be used to collectively refer to the
PEM_read_bio_foobar() , PEM_read_foobar() , PEM_write_bio_foobar() and PEM_write_foobar() functions.
The PrivateKey functions read or write a private key in PEM format using an EVP_PKEY structure. The write routines use
"traditional" private key format and can handle both RSA and DSA private keys. The read functions can additionally transparently
handle PKCS#8 format encrypted and unencrypted keys too.
PEM_write_bio_PKCS8PrivateKey() and PEM_write_PKCS8PrivateKey() write a private key in an EVP_PKEY structure in PKCS#8
EncryptedPrivateKeyInfo format using PKCS#5 v2.0 password based encryption algorithms. The cipher argument specifies the encryption algoritm to use:
unlike all other PEM routines the encryption is applied at the PKCS#8 level and not in the PEM headers. If cipher is
NULL then no encryption is used and a PKCS#8 PrivateKeyInfo structure is used instead.
PEM_write_bio_PKCS8PrivateKey_nid() and PEM_write_PKCS8PrivateKey_nid() also write out a private key as a PKCS#8 EncryptedPrivateKeyInfo
however it uses PKCS#5 v1.5 or PKCS#12 encryption algorithms instead. The algorithm to use is specified in the nid parameter and should be the
NID of the corresponding OBJECT IDENTIFIER (see NOTES section).
The PUBKEY functions process a public key using an EVP_PKEY structure. The public key is encoded as a
SubjectPublicKeyInfo structure.
The RSAPrivateKey functions process an RSA private key using an RSA structure. It handles the same formats as the
PrivateKey functions but an error occurs if the private key is not RSA .
The RSAPublicKey functions process an RSA public key using an RSA structure. The public key is encoded using a PKCS#1
RSAPublicKey structure.
The RSA_PUBKEY functions also process an RSA public key using an RSA structure. However the public key
is encoded using a SubjectPublicKeyInfo structure and an error occurs if the public key is not RSA .
The DSAPrivateKey functions process a DSA private key using a DSA structure. It handles the same formats as the
PrivateKey functions but an error occurs if the private key is not DSA .
The DSA_PUBKEY functions process a DSA public key using a DSA structure. The public key is encoded using
a SubjectPublicKeyInfo structure and an error occurs if the public key is not DSA .
The DSAparams functions process DSA parameters using a DSA structure. The parameters are encoded using a foobar
structure.
The DHparams functions process DH parameters using a DH structure. The parameters are encoded using a PKCS#3
DHparameter structure.
The X509 functions process an X509 certificate using an X509 structure. They will also process a trusted X509 certificate but any trust settings are
discarded.
The X509_AUX functions process a trusted X509 certificate using an X509 structure.
The X509_REQ and X509_REQ_NEW functions process a PKCS#10 certificate request using an X509_REQ structure. The X509_REQ write functions
use CERTIFICATE REQUEST in the header whereas the X509_REQ_NEW functions use NEW CERTIFICATE REQUEST (as
required by some CAs). The X509_REQ read functions will handle either form so there are no X509_REQ_NEW read functions.
The X509_CRL functions process an X509 CRL using an X509_CRL structure.
The PKCS7 functions process a PKCS#7 ContentInfo using a PKCS7 structure.
The NETSCAPE_CERT_SEQUENCE functions process a Netscape Certificate Sequence using a NETSCAPE_CERT_SEQUENCE
structure.
The PEM functions have many common arguments.
The bp BIO parameter (if present) specifies the BIO to read from or write to.
The fp FILE parameter (if present) specifies the FILE pointer to read from or write to.
The PEM read functions all take an argument TYPE **x and return a TYPE * pointer. Where
TYPE is whatever structure the function uses. If x is NULL then the parameter is ignored. If x is not
NULL but *x is NULL then the structure returned will be written to *x . If neither x nor *x is
NULL then an attempt is made to reuse the structure at *x (but see BUGS and EXAMPLES sections).
Irrespective of the value of x a pointer to the structure is always returned (or NULL if an error occurred).
The PEM functions which write private keys take an enc parameter which specifies the encryption algorithm to use, encryption is done
at the PEM level. If this parameter is set to NULL then the private key is written in unencrypted form.
The cb argument is the callback to use when querying for the pass phrase used for encrypted PEM structures (normally only private
keys).
For the PEM write routines if the kstr parameter is not NULL then klen bytes at kstr are used as the
passphrase and cb is ignored.
If the cb parameters is set to NULL and the u parameter is not NULL then the u parameter is interpreted
as a null terminated string to use as the passphrase. If both cb and u are NULL then the default callback routine is used which
will typically prompt for the passphrase on the current terminal with echoing turned off.
The default passphrase callback is sometimes inappropriate (for example in a GUI application) so an alternative can be supplied. The callback
routine has the following form:
Although the PEM routines take several arguments in almost all applications most of them are set to 0 or NULL .
Read a certificate in PEM format from a BIO:
The old PrivateKey write routines are retained for compatibility. New applications should write private keys using the
PEM_write_bio_PKCS8PrivateKey() or PEM_write_PKCS8PrivateKey() routines because they are more secure (they use an iteration count of 2048 whereas
the traditional routines use a count of 1) unless compatibility with older versions of OpenSSL is important.
The PrivateKey read routines can be used in all applications because they handle all formats transparently.
A frequent cause of problems is attempting to use the PEM routines like this:
This old PrivateKey routines use a non standard technique for encryption.
The private key (or other data) takes the following form:
After this is the base64 encoded encrypted data.
The encryption key is determined using EVP_bytestokey() , using salt and an iteration count of 1. The IV used is the value of
salt and *not* the IV returned by EVP_bytestokey() .
The PEM read routines in some versions of OpenSSL will not correctly reuse an existing structure. Therefore the following:
The read routines return either a pointer to the structure read or NULL if an error occurred.
The write routines return 1 for success or 0 for failure.
Homemade Porn Online
Erotic Oral Sex
Hot Nurse Fucked Hard
Black Oral Sex
Young Missionary Sex