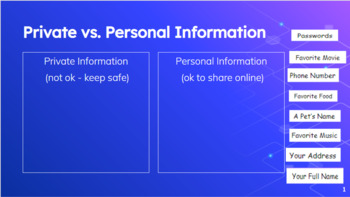
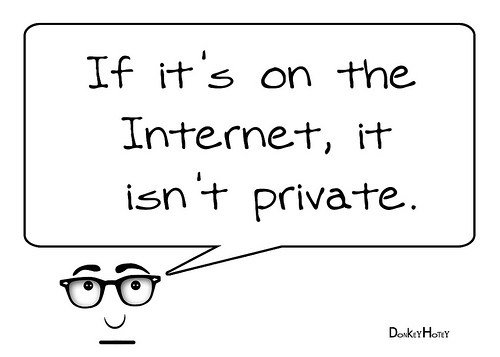
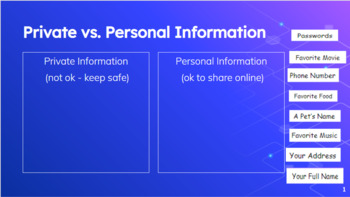
Private Information
👉🏻👉🏻👉🏻 FOR MORE INFORMATION, CLICK HERE 👈🏻👈🏻👈🏻
Gamerchat
Hairy Velma
Sex Family Daddy
Hottewt redhead pornstar
Superhot Kira Queen rides a giant cock
Naked night walk
Free Xl Girls Pics
Private Information






































0">190">281_.jpg">
















































👉🏻👉🏻👉🏻 FOR MORE INFORMATION, CLICK HERE 👈🏻👈🏻👈🏻
Gamerchat
Hairy Velma
Sex Family Daddy
Hottewt redhead pornstar
Superhot Kira Queen rides a giant cock
Naked night walk
Free Xl Girls Pics
Private Information






































0">190">281_.jpg">