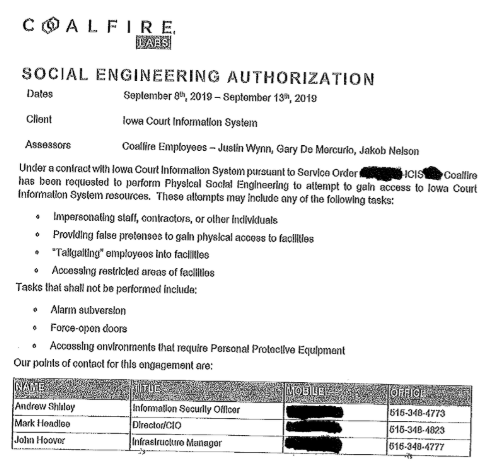
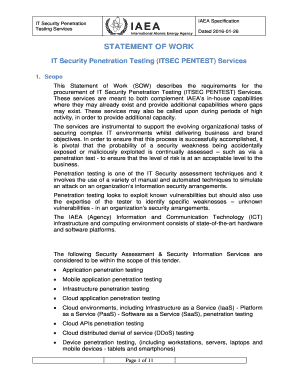
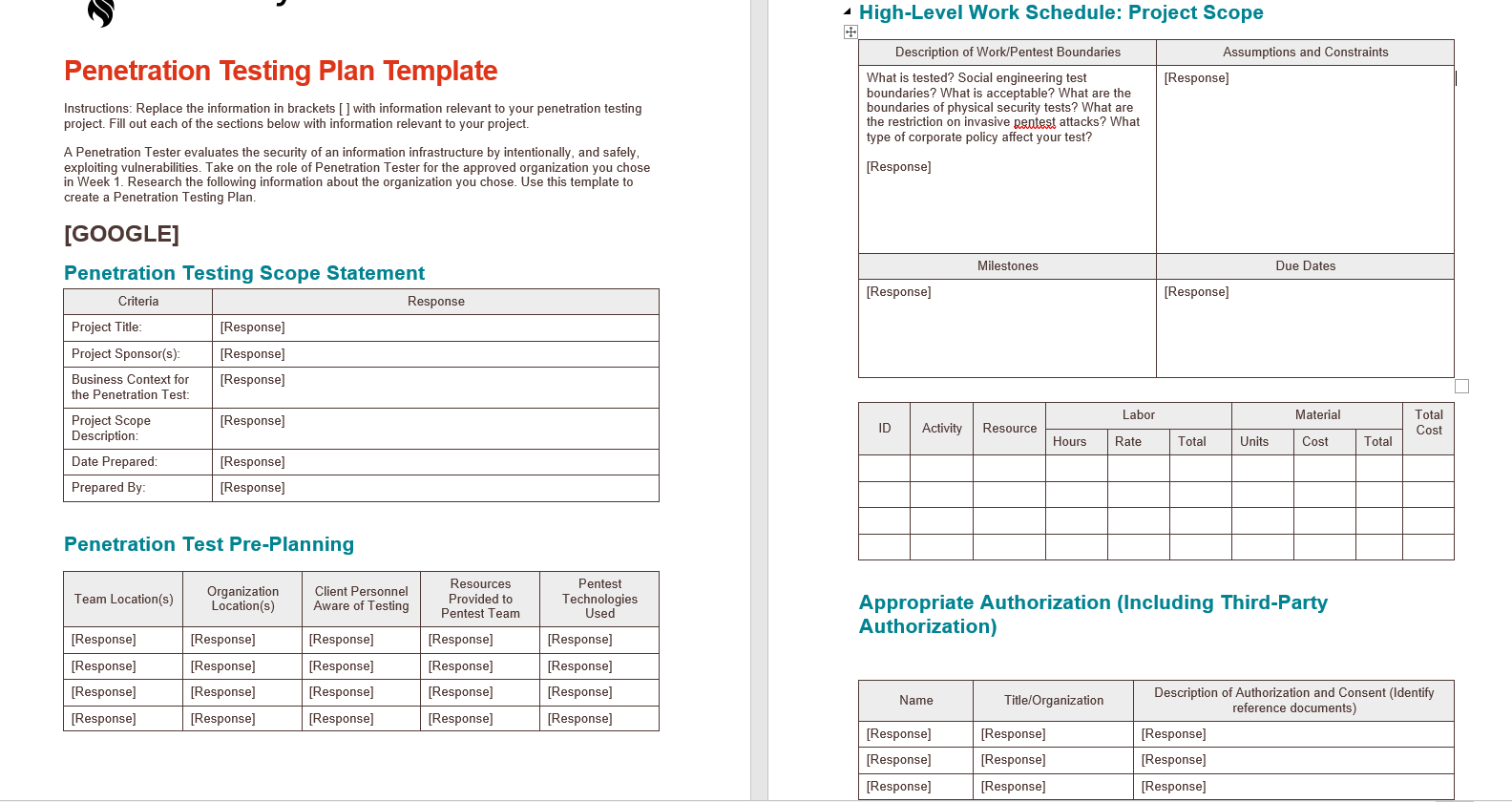
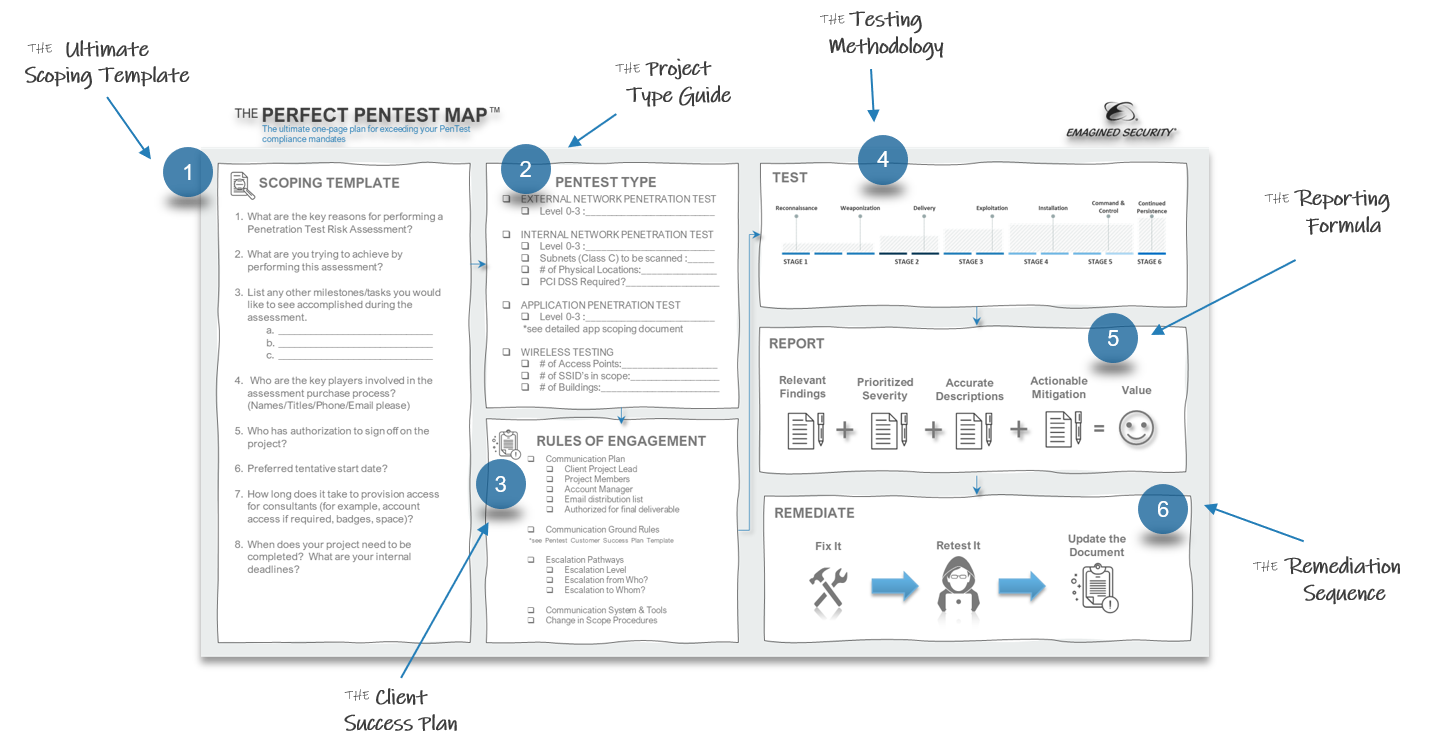
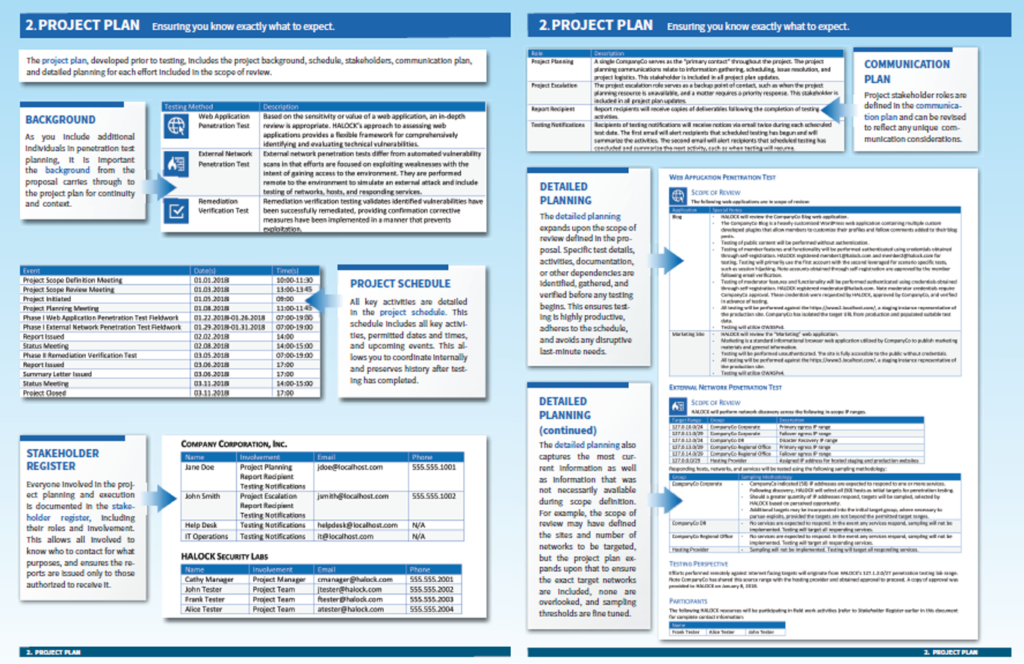
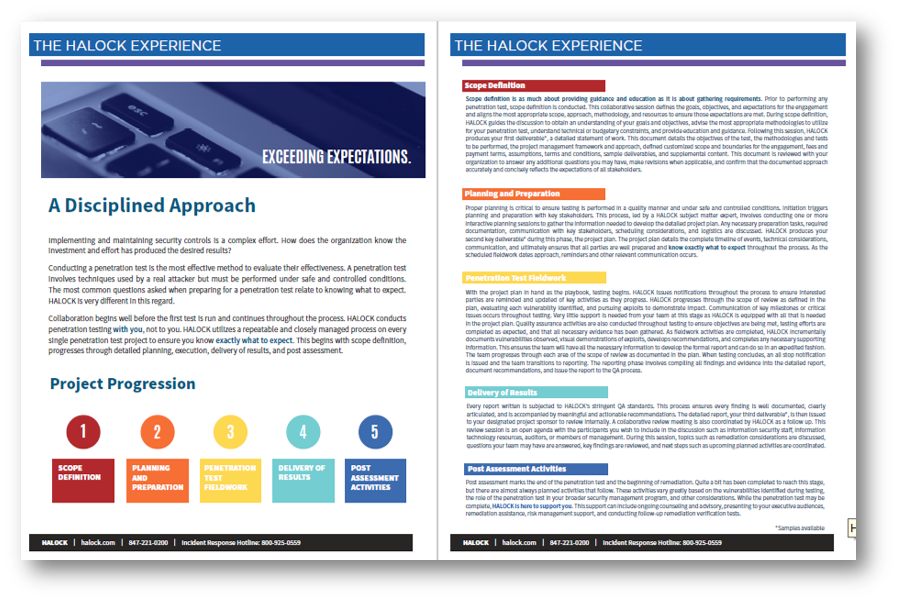
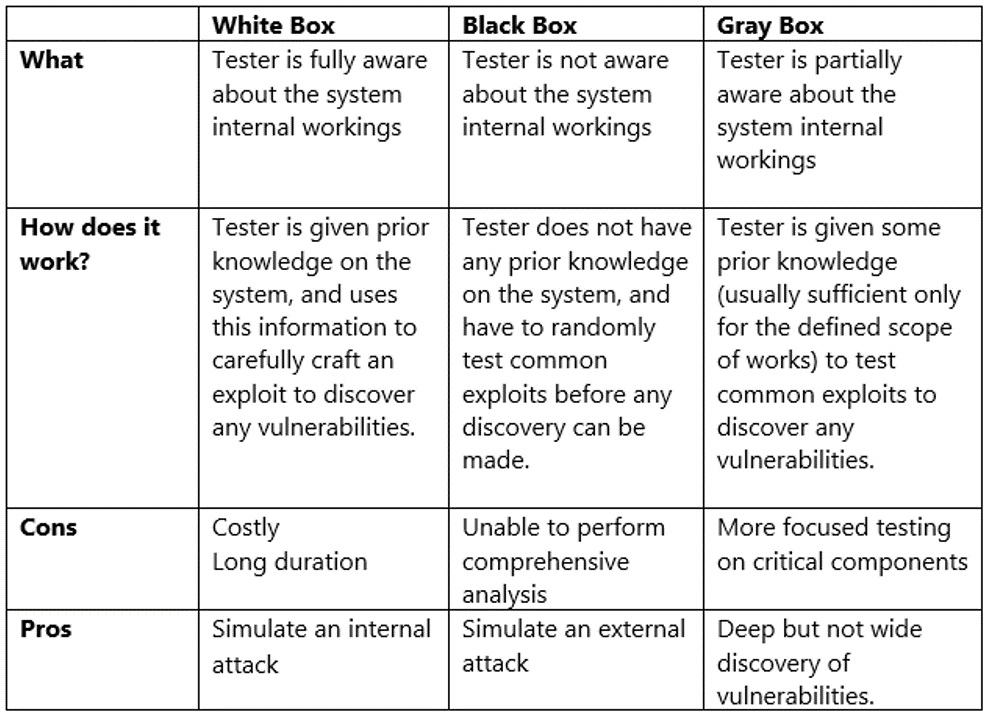
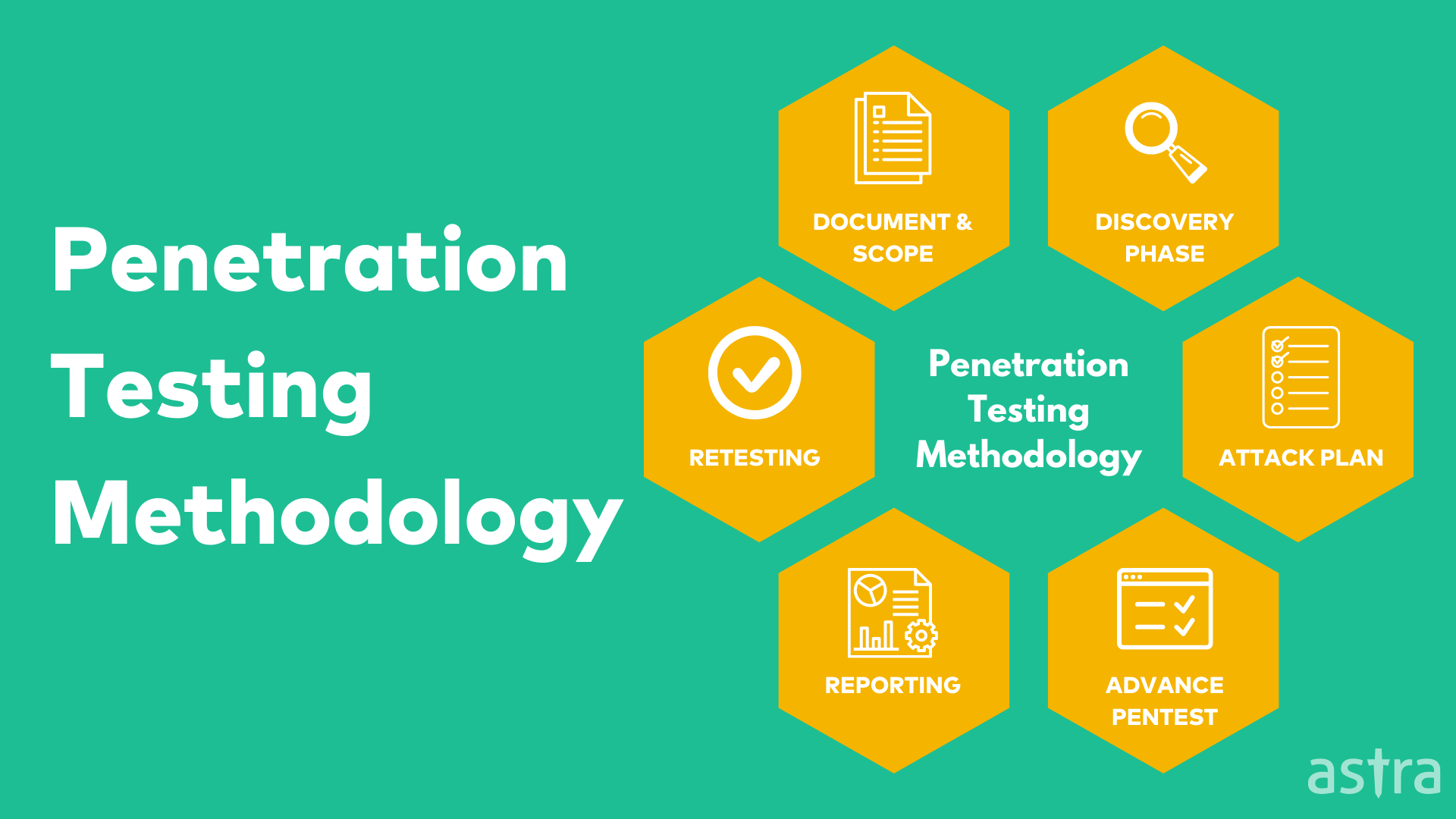
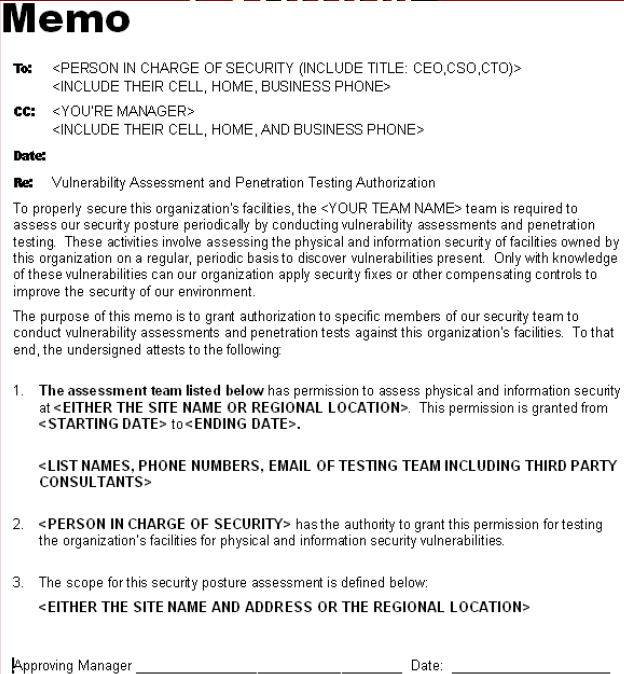
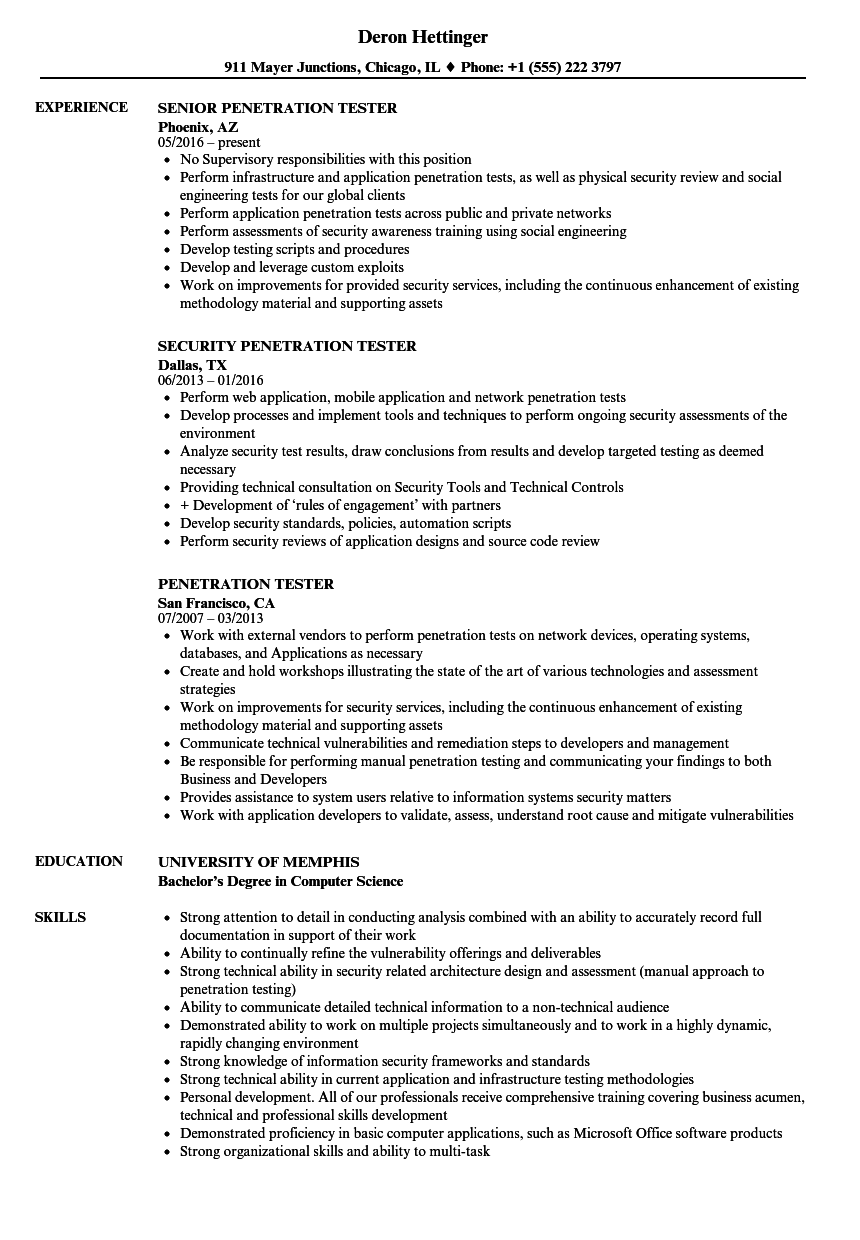
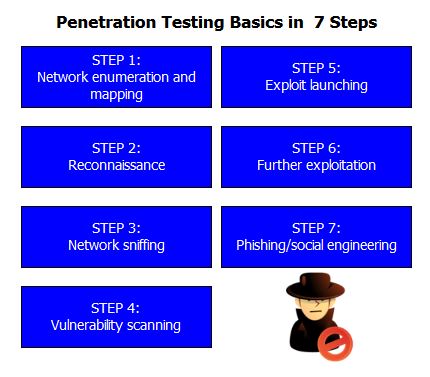
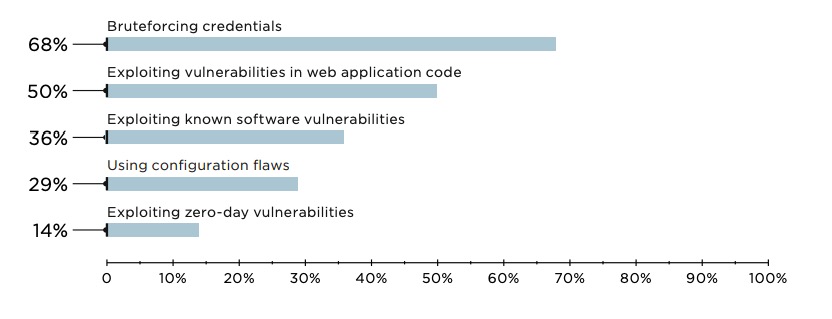
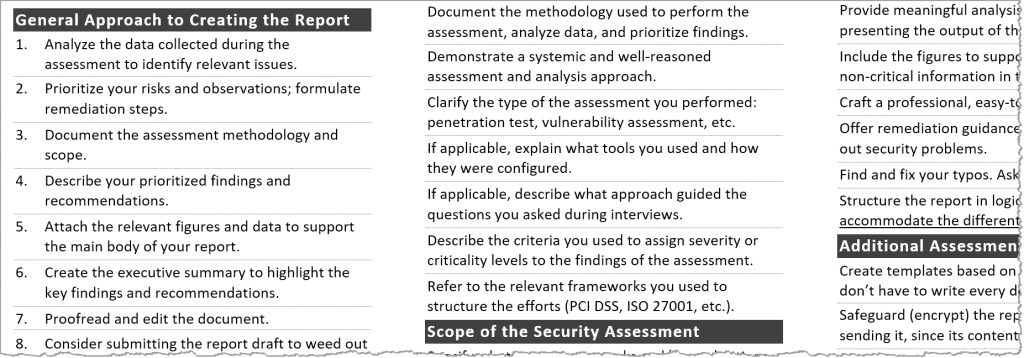
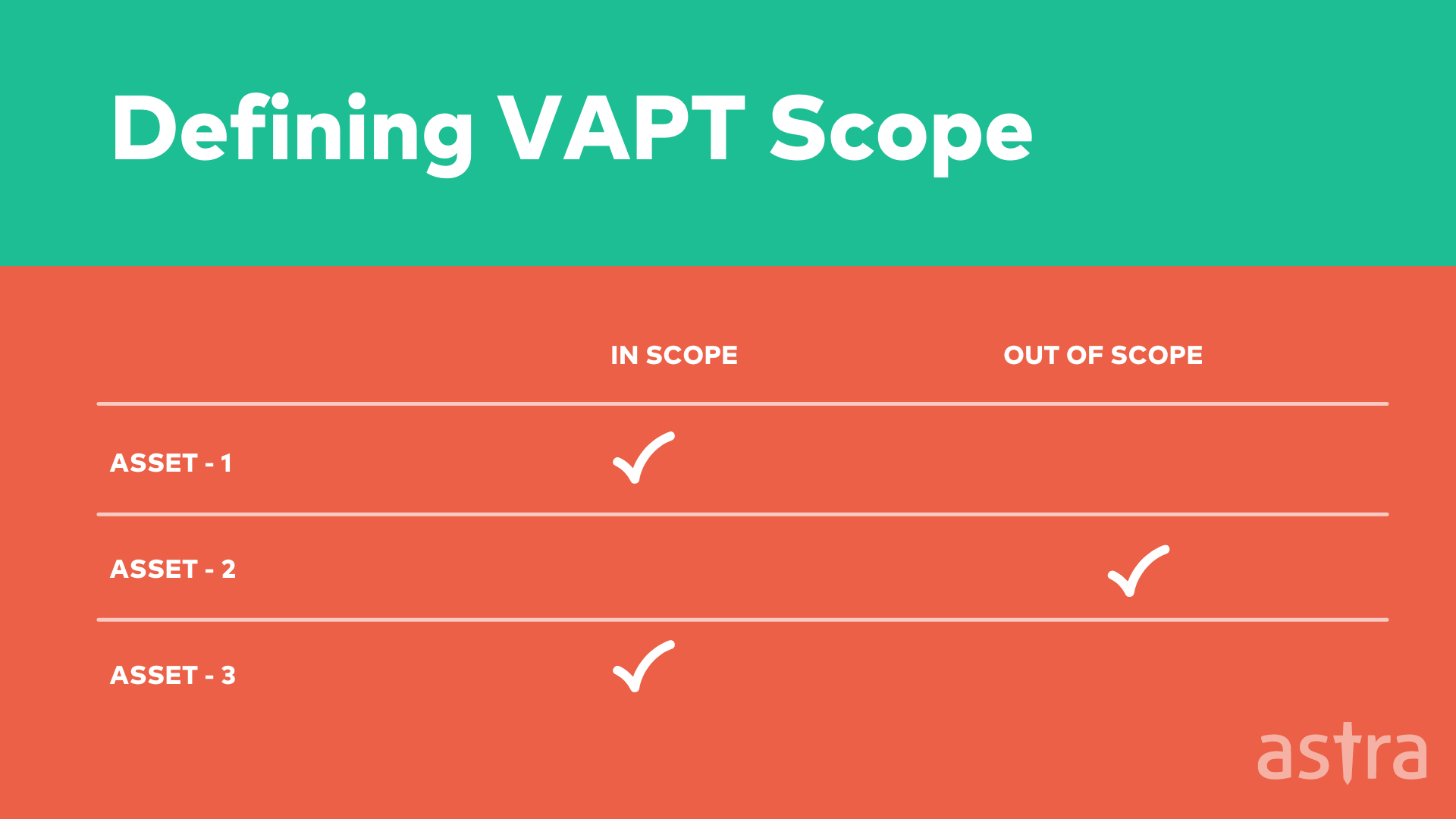
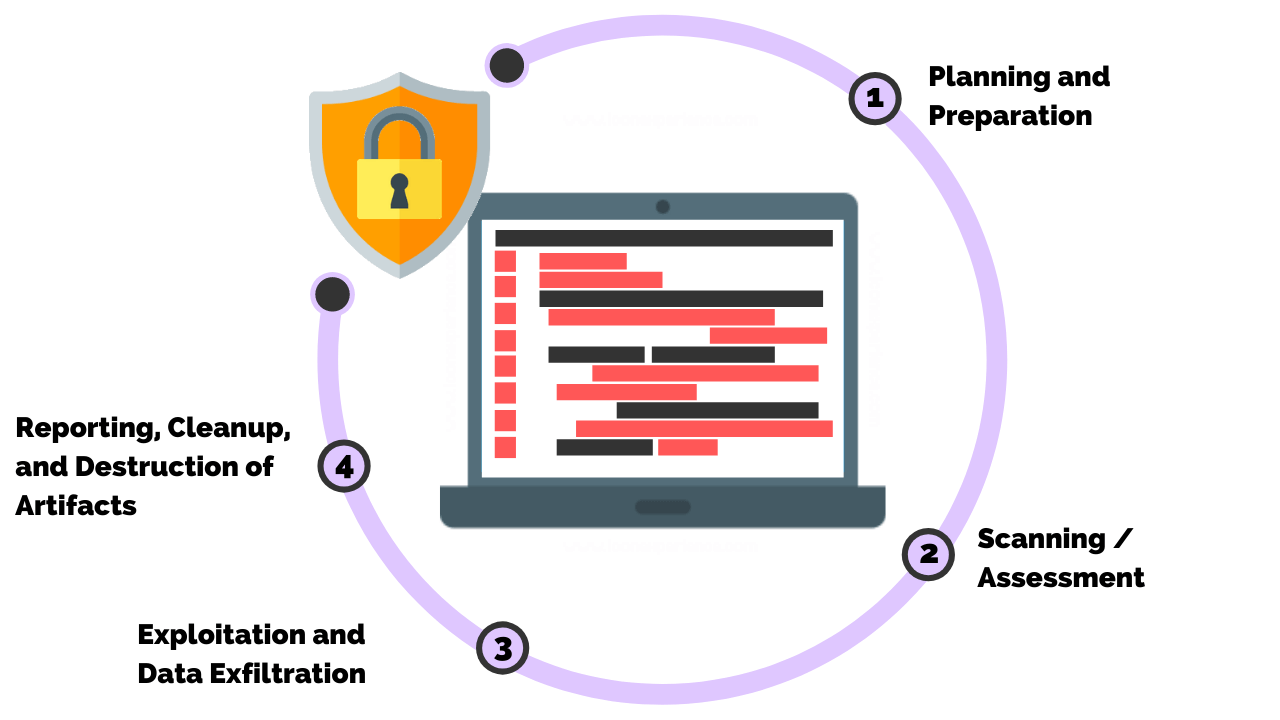
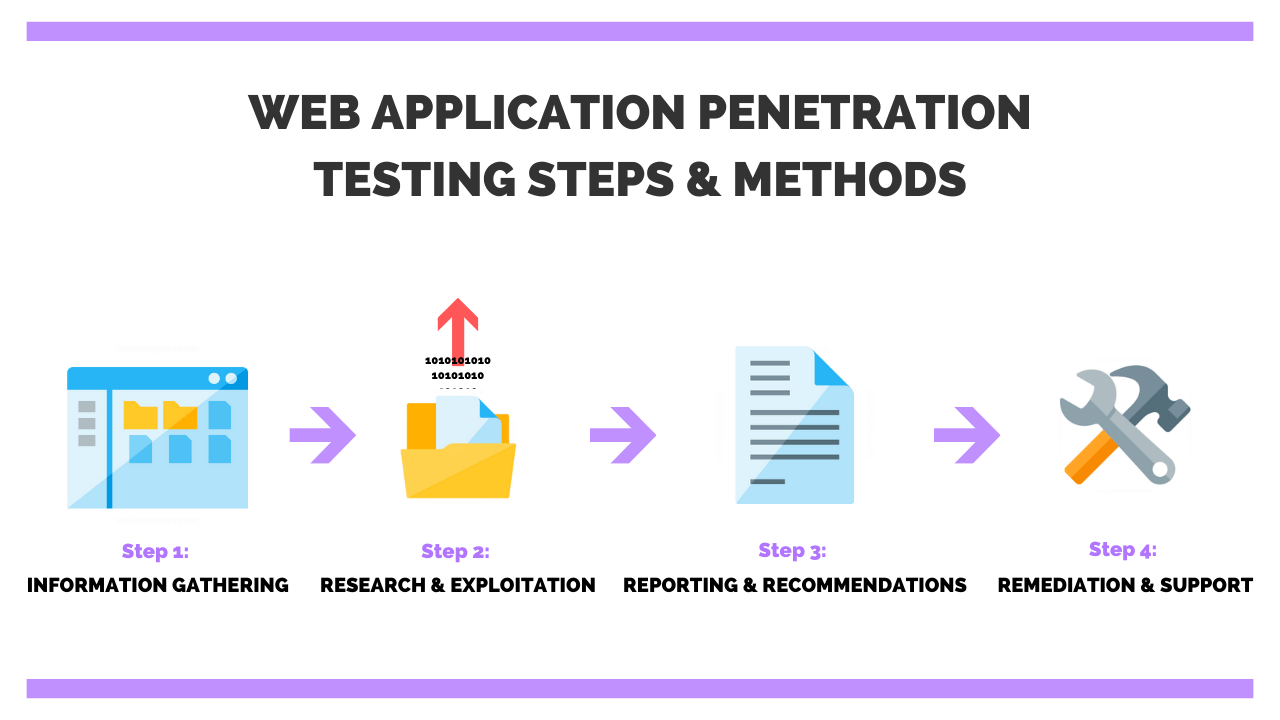
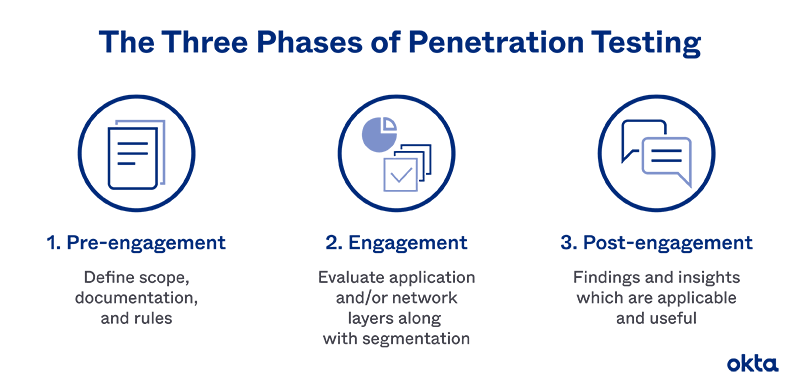
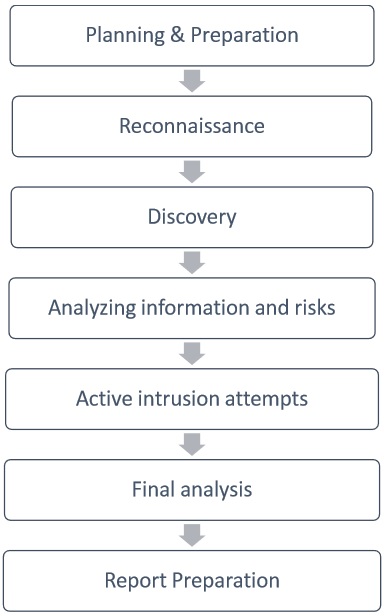
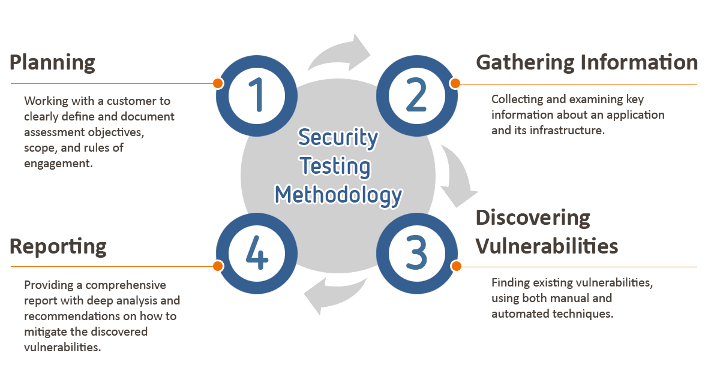
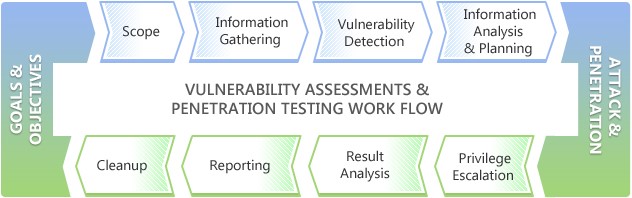
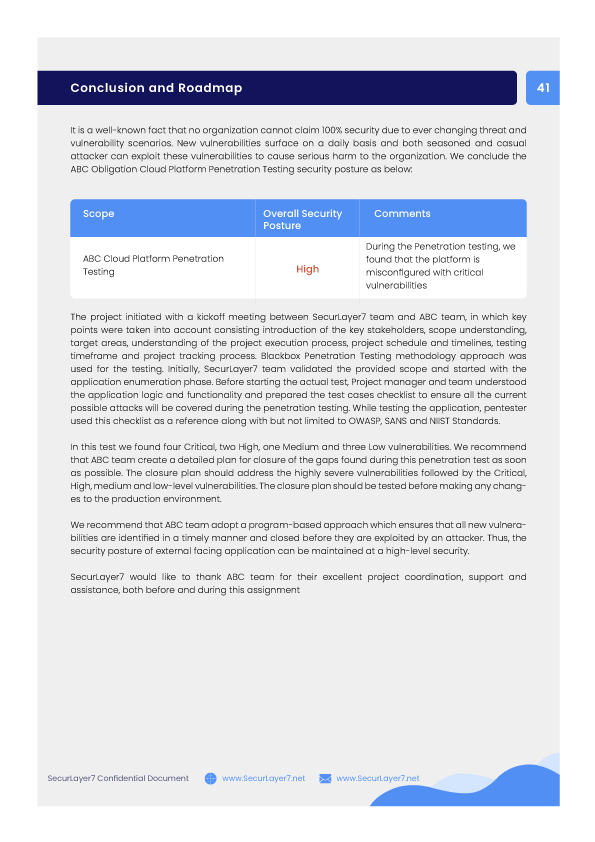
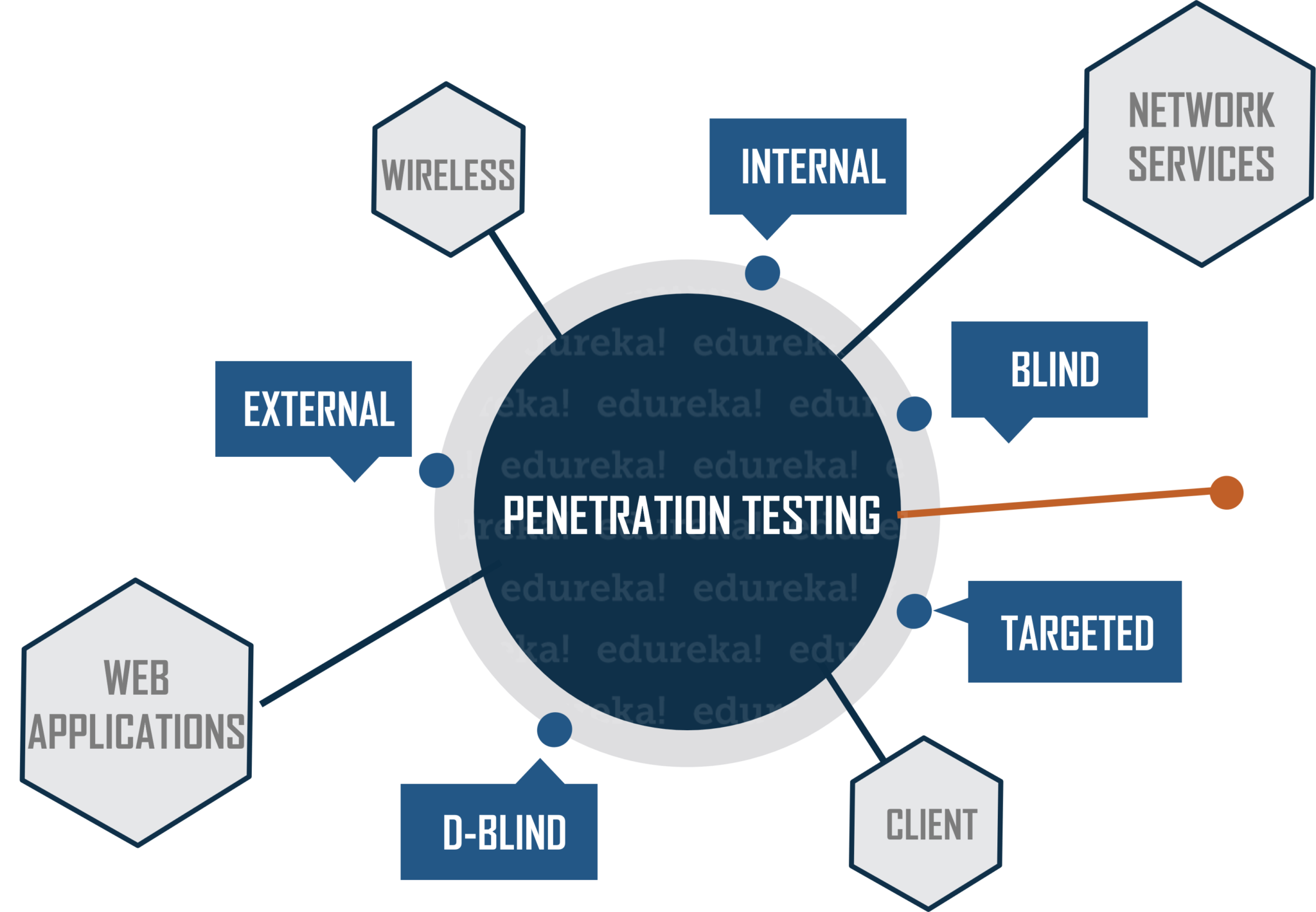
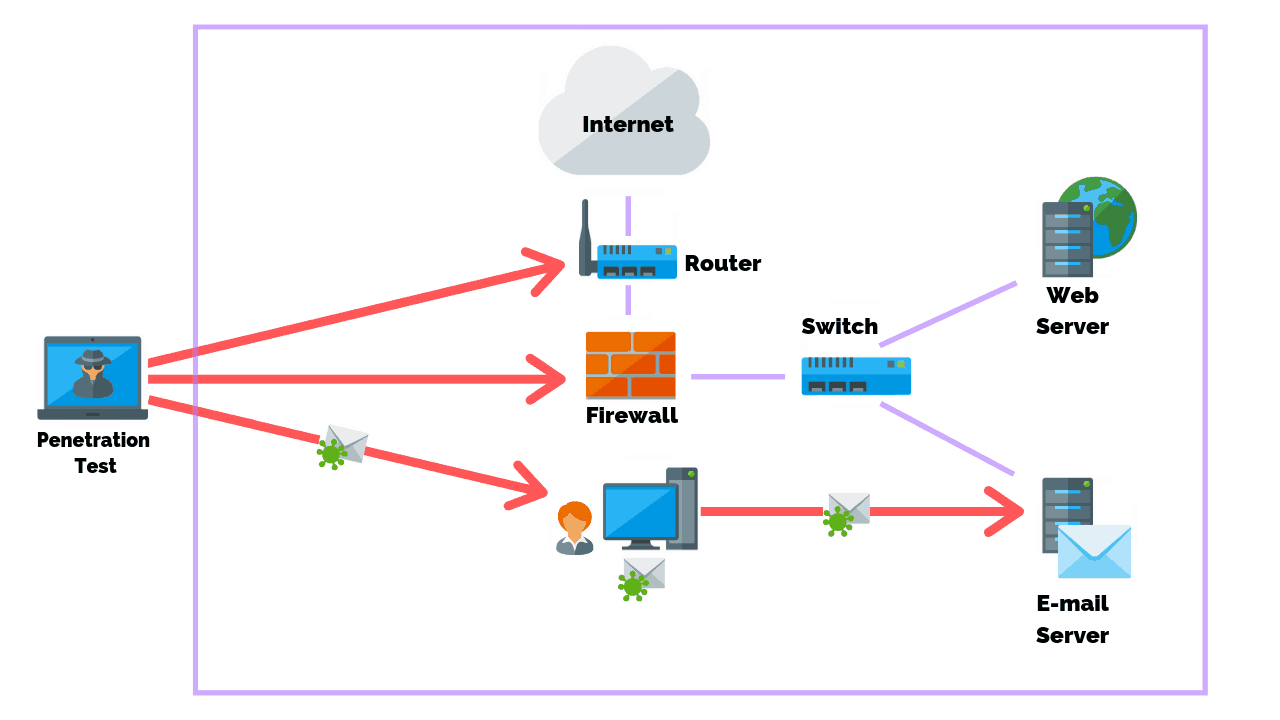
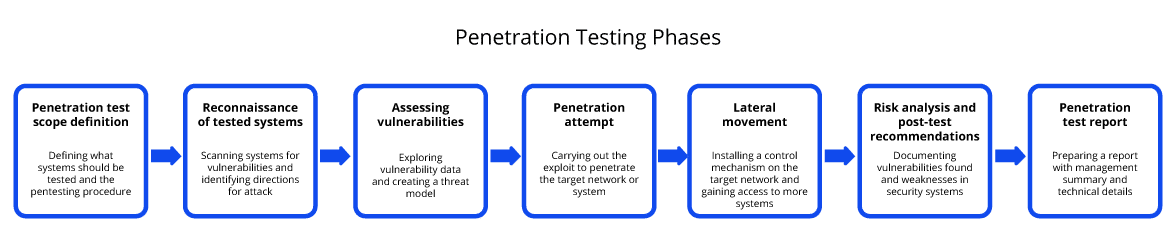
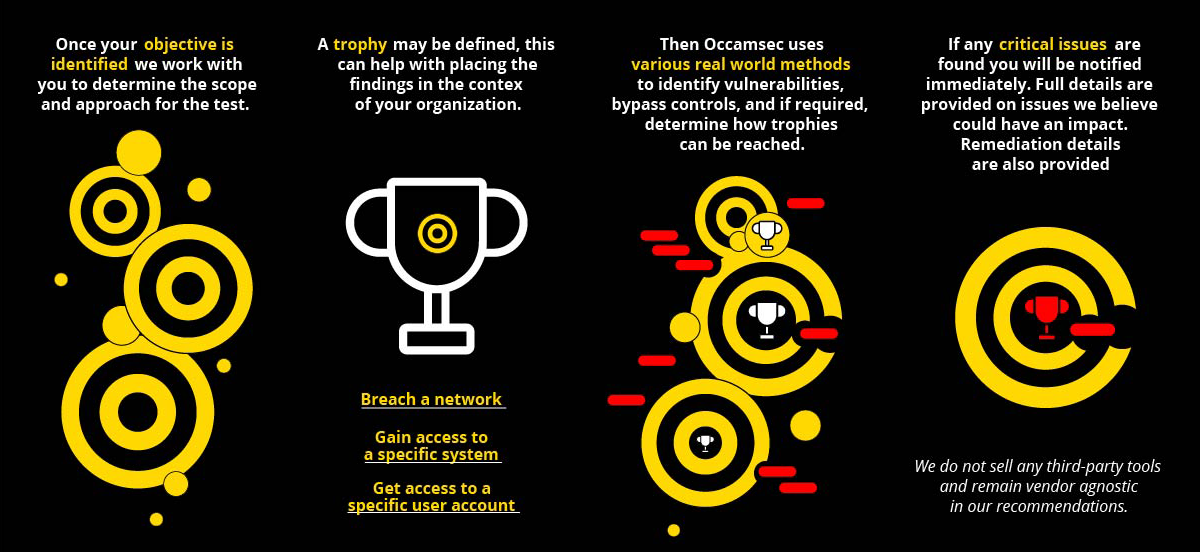
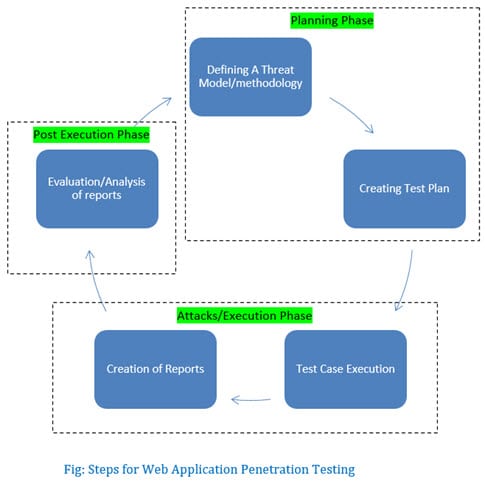
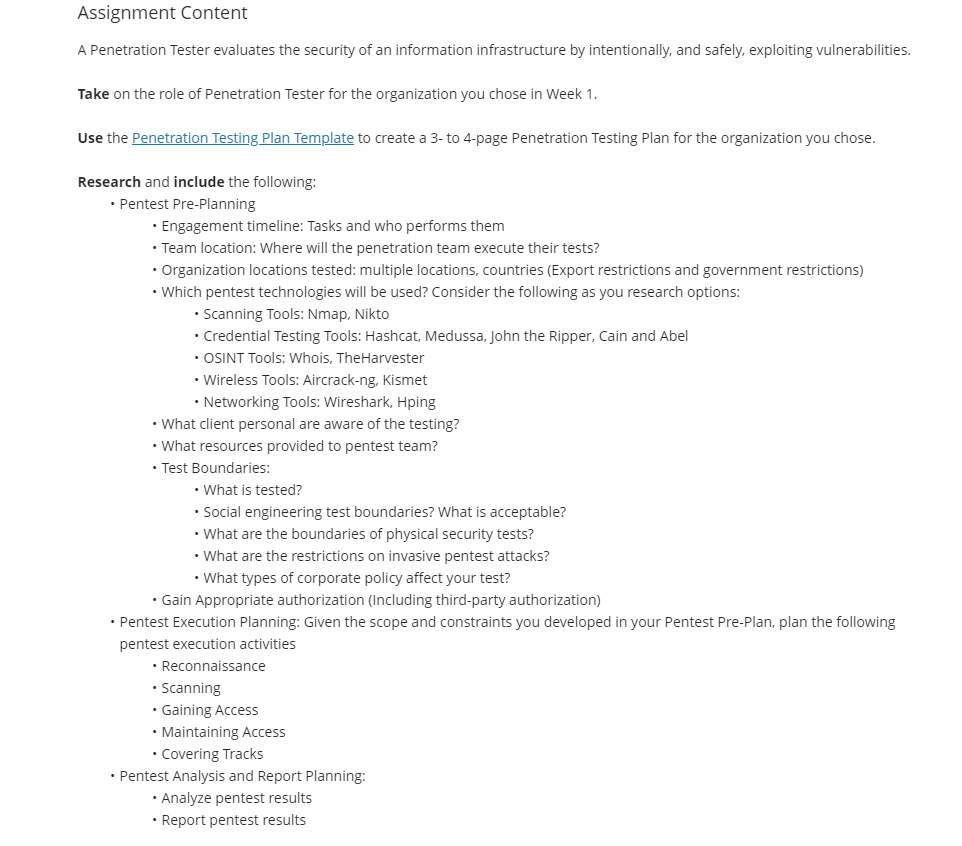
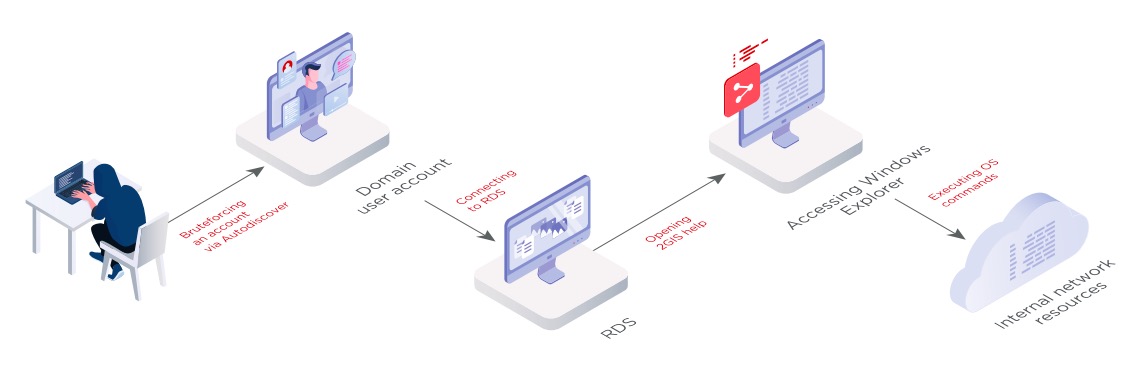
Penetration testing scope of work

🛑 👉🏻👉🏻👉🏻 FOR MORE INFORMATION, CLICK HERE 👈🏻👈🏻👈🏻
Anna Kendrick Naked Tits - Sex Teenagers
Webcam chick slow masturbation
Drunk Girl Fucked Stranger
Scent Of A Woman Torrent
Mature In Pantyhose
Mom Bend Over Panties Down
Frat Men Videos
Penetration testing scope of work