Linken Sphere crack v9.0 | Tutorial & Free Download 2024
| 2024
Download archive with version 8.77 - https://mega.nz/file/4rcRgbbb#zG8Z3K54TD7FoaInKCBMpmew2GMnb9Whongh869Gy3E
Archive password - 2024
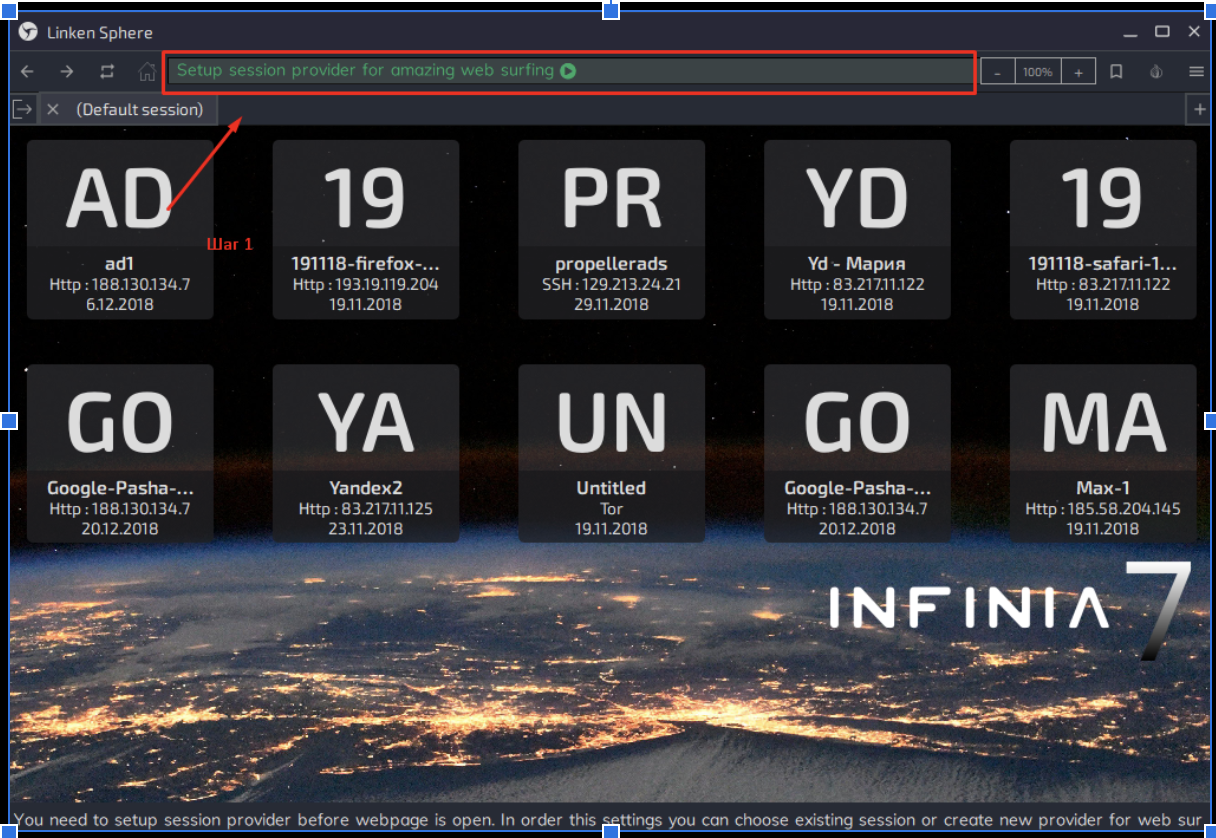
Preparing a work session
So we have authorized in the browser and the question arises, what should we do? What and how to customize?
First we need to create our session for this click on the window of web address.
Session setup
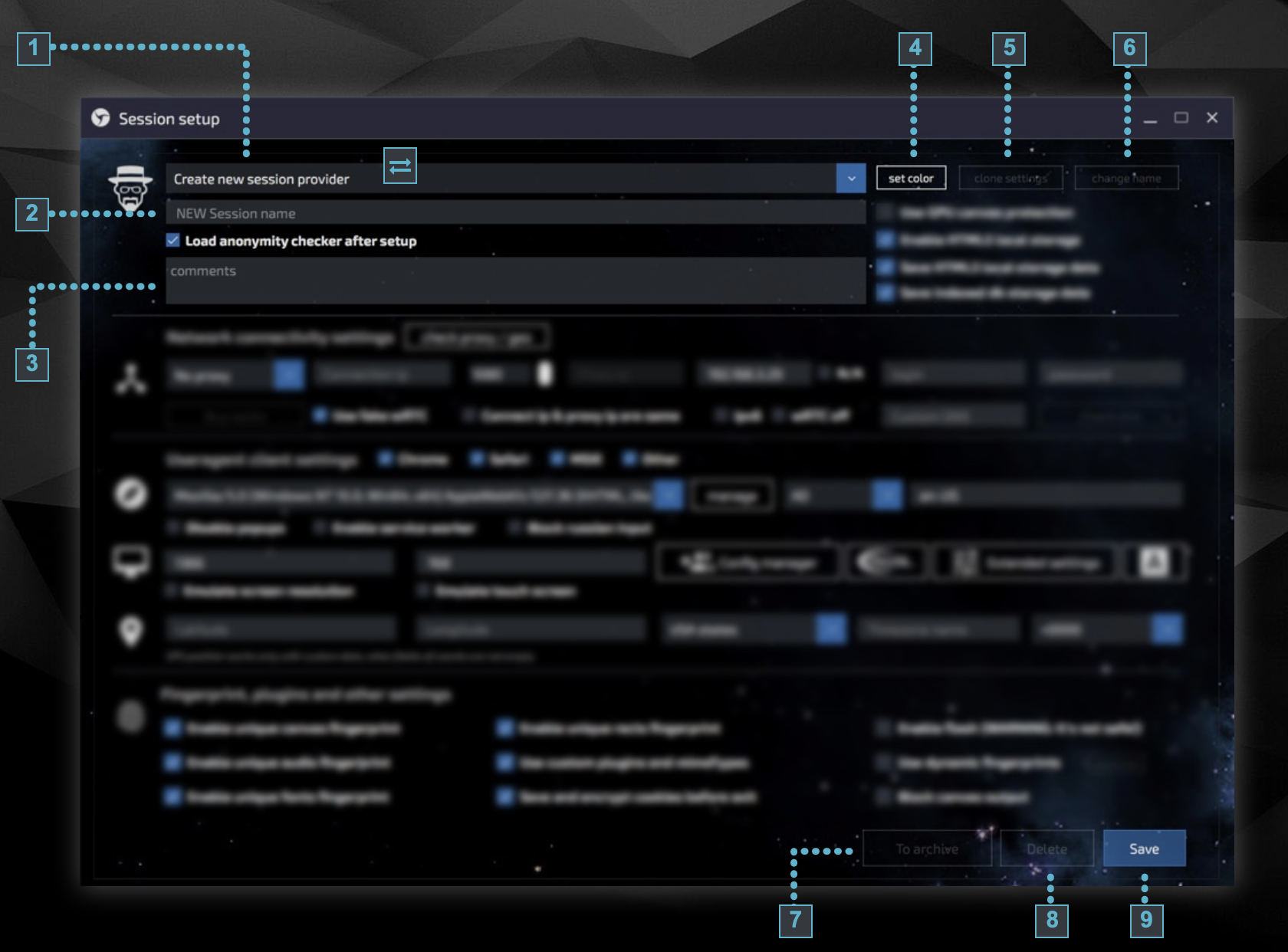
1.Create new session provider - field for activating previously created sessions
2.NEW Session name - field for entering the name of a new session
3.Notes window
4.Setting the color (works like a note)
5.Clone setting - session cloning
6.Cnange name - session renaming
7.To arhive - Send to archive button. Moves the session to the archive, it can be restored later on
8.Delete - Deleting a session
9.Save - session saving
Load anonymity checker after setup - after starting a working session sends you to the site: https://whoer.net
You can use different connection types for different tabs, and they can function in parallel. This greatly simplifies and speeds up your work, as it allows you to keep a connection to an ssh or socks server in parallel tabs with their own anonymity settings and different cookies. Unless otherwise selected when creating a new session, the tab will use the default internet connection.
Please note, you do not need to use any additional software to work with different types of connections - the whole set of software for multithreaded proxying is included in the browser and starts working together with it. You don't need to run and configure anything else - the built-in proxifier will automatically apply the necessary parameters.
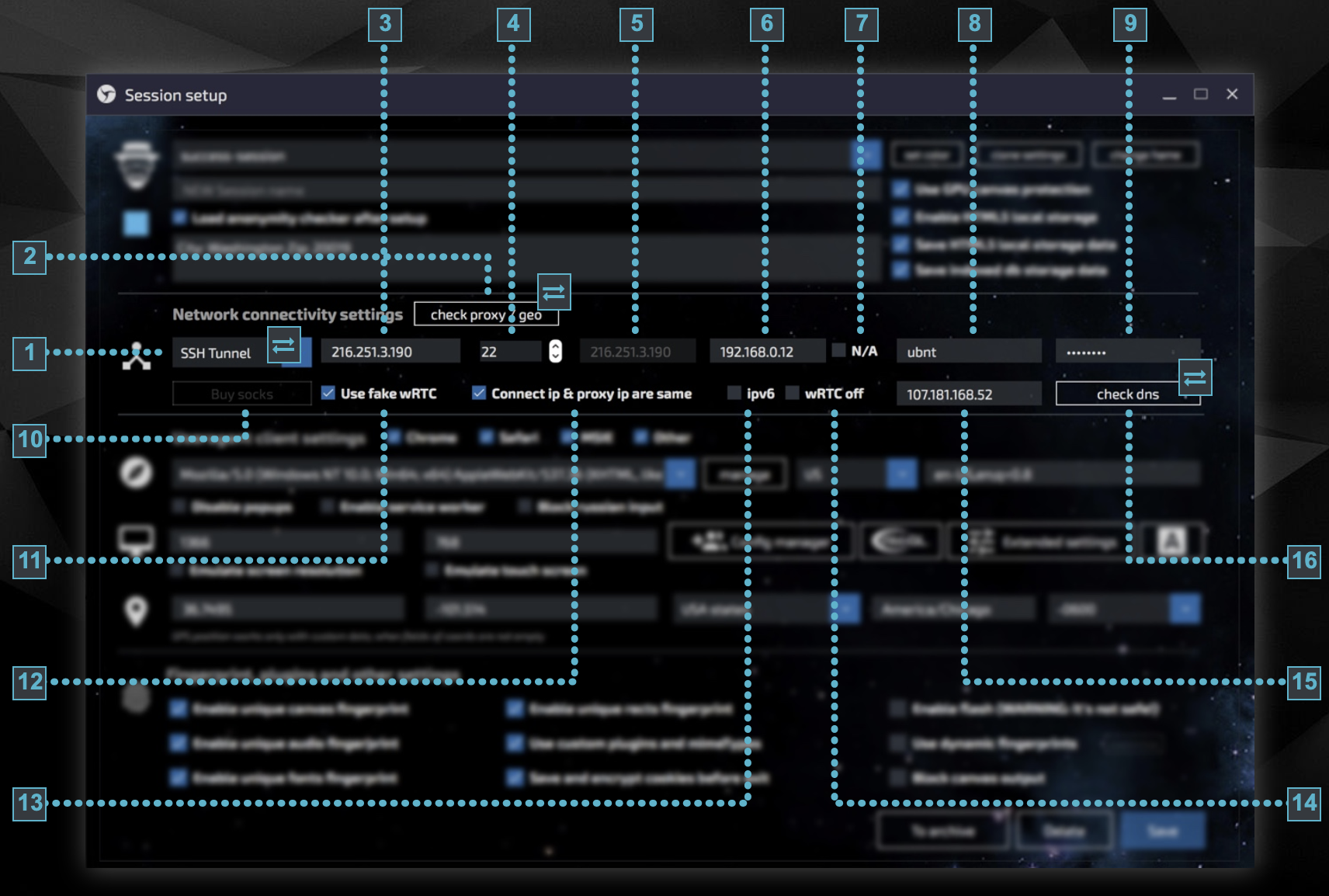
1.Connection type:
No proxy - this is clear, it uses the direct connection of your computer
Tor - connection is made using Tor network
Http - using http proxy connection
Socks5: connection to proxy via SOCKS5.
"The main difference between http and Socks5 is that https is for browsers (web surfing), and SOCKS5 is for applications, games, programs."
Dynamic socks5: connection to work with mobile SOCKS, when you change IP it automatically reloads the page to spoof WebRTC. The heck of it.
SSH Tunnel: using an SSH connection. Same as http, but considered more anonymous and a more glitchy option.
Tor + SSH Tunnel: using TOR chain before connecting to SSH, if you really need to hide yourself.
Sphere socks
2.Button to check validity of connection.
3.Server address field for connection
4.Port field for connection (by default 22 is used for SSH connections). 4.
5.Public WebRTC. Field for manually entering the outgoing WebRTC leak address when proxying the connection. The checkbox must be unchecked before entering the desired IP in the field. Just leave this field untouched, the ip of your proxy should be entered there.
6.Local WebRTC. Field for specifying local ip-address - you can specify any necessary local address transmitted via WebRTC leak. Function for cunning assholes who want to mislead the FSB following you in our case we just specify the ip address of our proxy. Just check the "N/A" checkbox.
7. Disabling local WebRTC.
8 and 9 login and password from our proxy
10. Button to buy sox directly in the browser (expected)
11.Use fake wRTC - leave this function enabled, it allows you to hide your ip by one more wRTC parameter (something related to image).
12.Copnest ip & proxy ip are the same - Disable option to set the correct IP address to leak through WebRTC in case the incoming and outgoing IP address of the connection are different. We talked about this in section 5
13. Option to use IPV6 proxy. I will say from practice that ipV6 often lags.
14. Allows you to disable WebRTC. If we check this box, we can simply hide our WebRTC settings, which will be suspicious for the anti-fraud system and a high probability that the whole screen will be crooked.
15.Field for entering user DNS. In case the sox or tunnel does not have its own DNS or if you need to replace it, you have the opportunity to write the desired address in this field. In short, these are deep settings of your proxy, it is better not to go there.
16.Button to check the validity of manually set DNS
Anonymity
1.Canvas GPU Protection - Uses color profile changing technology to anonymize Canvas. Allows manual swap checks to pass, but may not be acceptable for use with some automatic AF systems. Leave enabled.
2.Use Local Storage - Local Storage. Used to store data between user sessions. Unlike cookies, data is stored locally and is not transferred to the web server. I think it should be left in.
3.Save local storage data - Allows you to save local storage data and use it after a browser reload (without this option, local storage data is cleared after closing the browser). I think it should be left.
4.Store IndexedDB data - IndexedDB is a storage of large amounts of structured data on the client. The option allows data to be stored for use after the browser is reloaded. I think it should be left in.
5.Disable popups - When using some sessions you may find it necessary to block popups. This option allows you to disable the creation of popups on the page. Leave it
6.Enable service worker - This is a special service for web content. Service worker performs some cache manipulations and in OTR mode this option should be disabled for security reasons. If a certain site is working with errors, you can activate this option, but in other cases we recommend to use the browser without it. Leave this option blank.
7.Block russian input - Block Cyrillic characters Allows you to block Cyrillic characters when typing on the site (not blocked in the URL)Leave this option blank.
8.Canvas spoofing - Enable Canvas spoofing (if this option is disabled, the real data of your device is taken) ON or OFF in item 17.
9.Audio Swap - Enable Audio swap (if this option is disabled, the real data of your device is taken).
10.Font Swap - Enable font swapping (if the option is off, it takes the real data of your device) INCLUDED
(Note, if you use config, fonts are not generated, but taken from config)
11.Spoofing by clientRects - Enable spoofing by clientRects (if this option is off, the real data of your device is taken)
12.Spoofing by plugins - Enable user fingerprint spoofing by plugins and supported file types INCLUDED
13.Encrypting and saving cookies - Encrypts and saves cookies of the current session after exiting the tab. It allows you not only to save cookies with the possibility of their further uploading, but also to keep them in encrypted form to increase the security of work. The use of individual cookies allows you to conveniently work in multithreaded mode without the need to constantly download and upload them, as well as without using a large number of portable browsers. INCLUDE.
14.Flash support - Enabling Flash. As you know, currently available technologies do not allow you to fully use the means of anonymization when working with Flash. Nevertheless, for experienced users who know where and when its use is possible, the option to activate it has been left. By default, this menu item is inactive, but you can turn it on if you need it. OFF if you need strong anonymity.
15.Use dynamic fingerprints - Allows you to disable saving static fingerprints for a specific session. When this checkbox is activated, the session will have new fingerprints every time you click save. OFF
16.Configuring Dynamic Footprints
17.Block Canvas - Some sites may be more loyal to disallowing Canvas fingerprint tracking than Canvas spoofing. This feature allows you to activate a ban on taking a given print. INCLUDE.