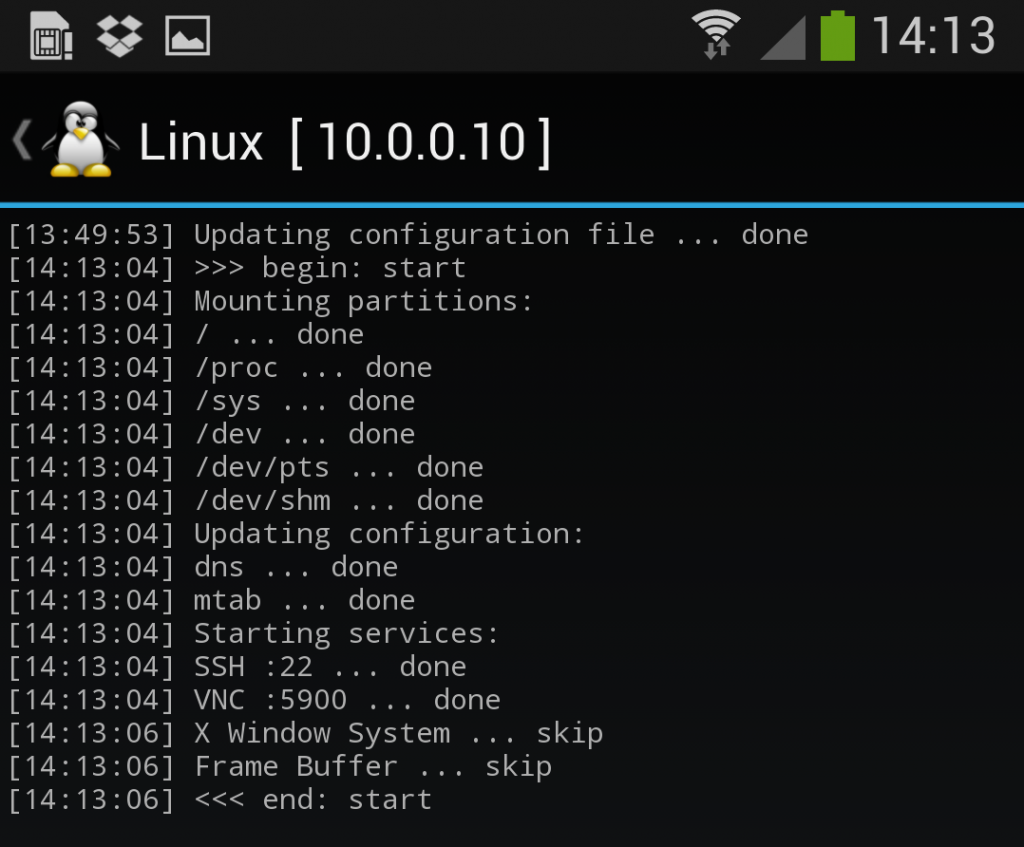
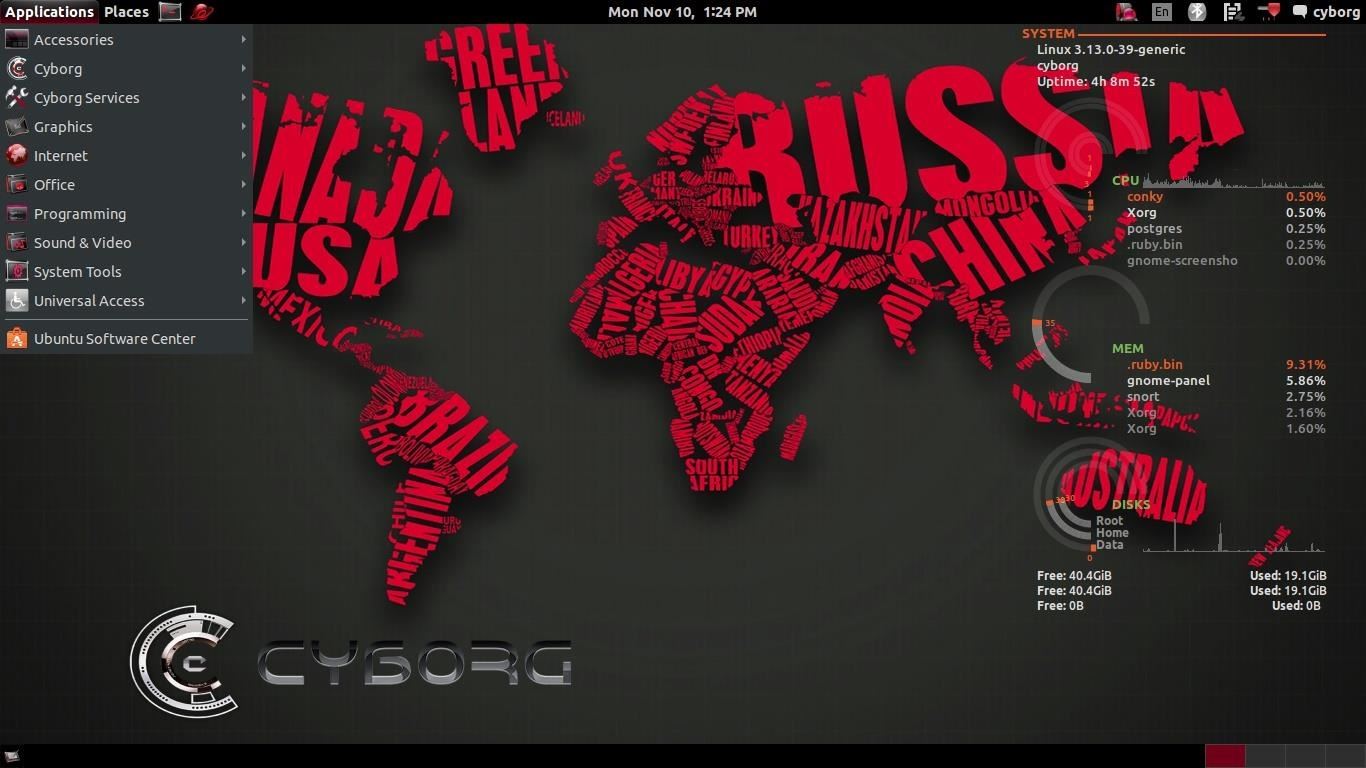
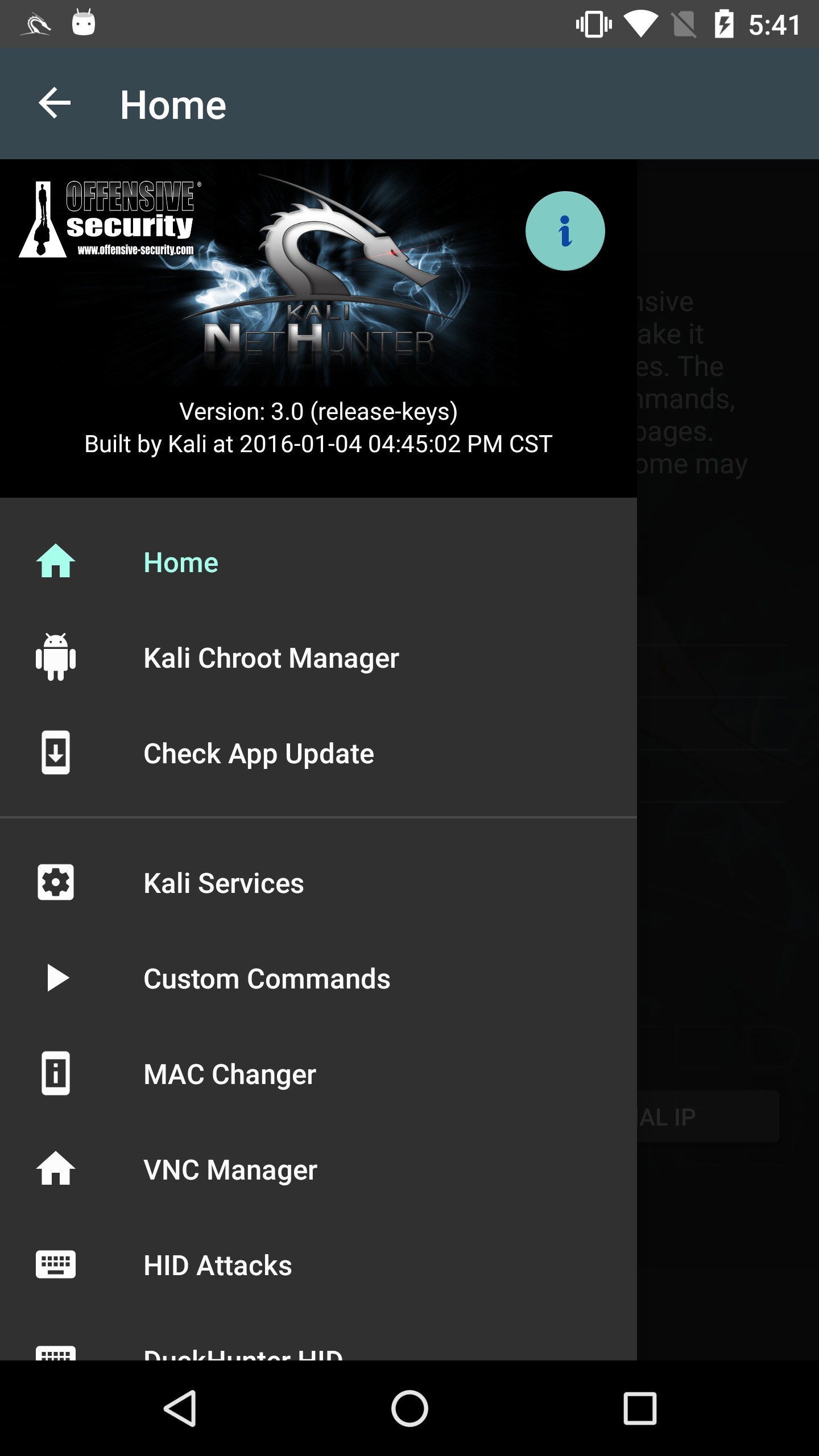
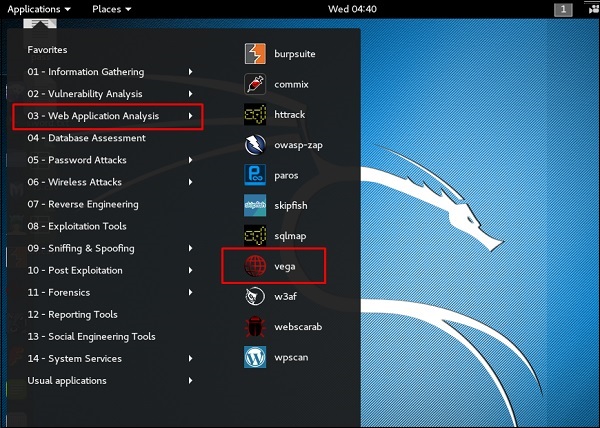
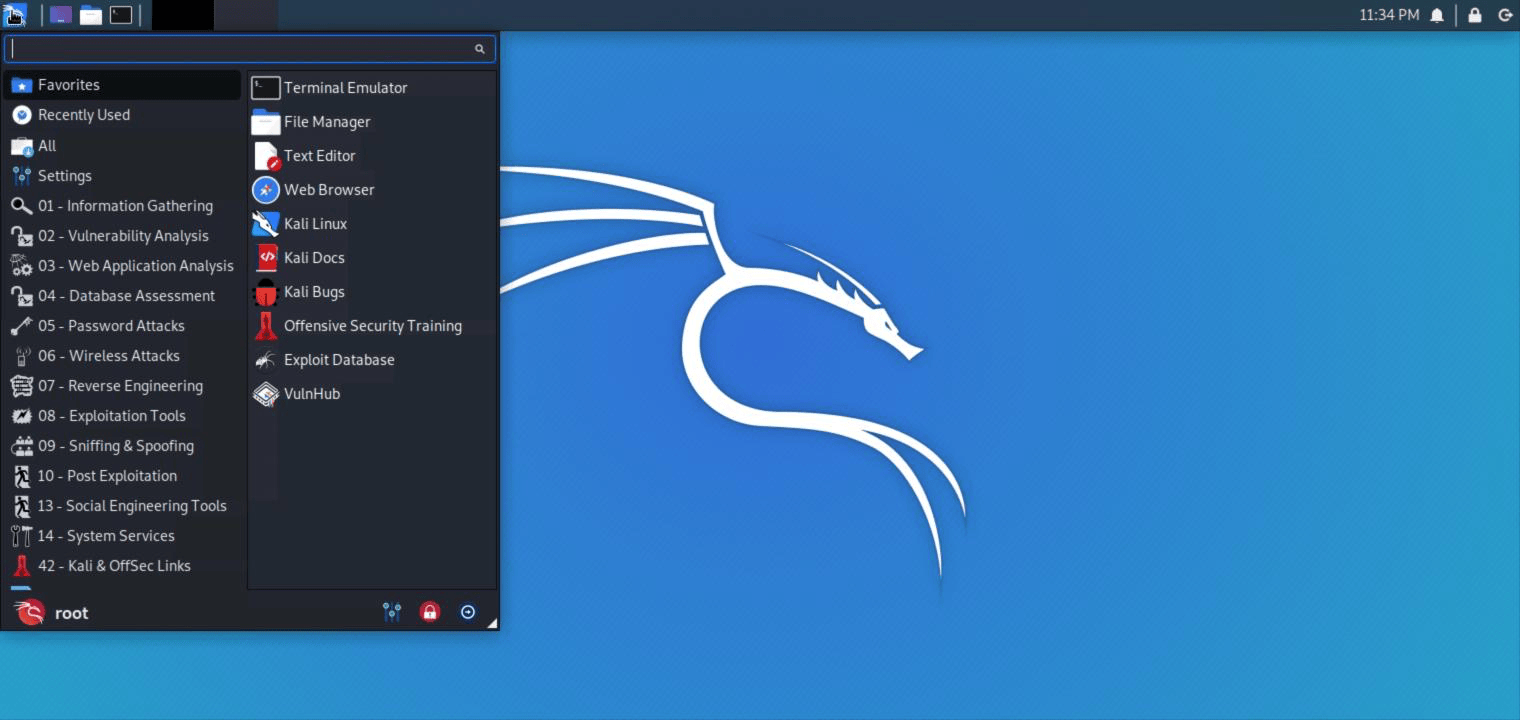
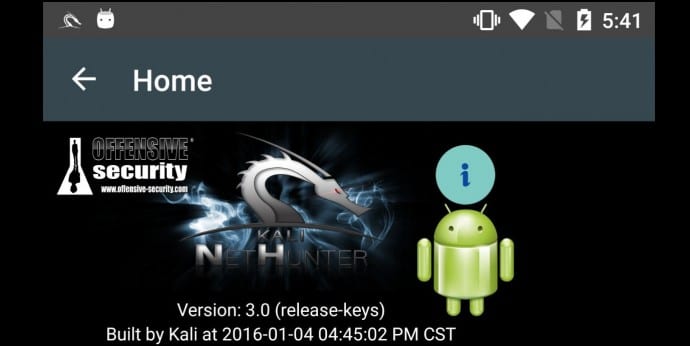
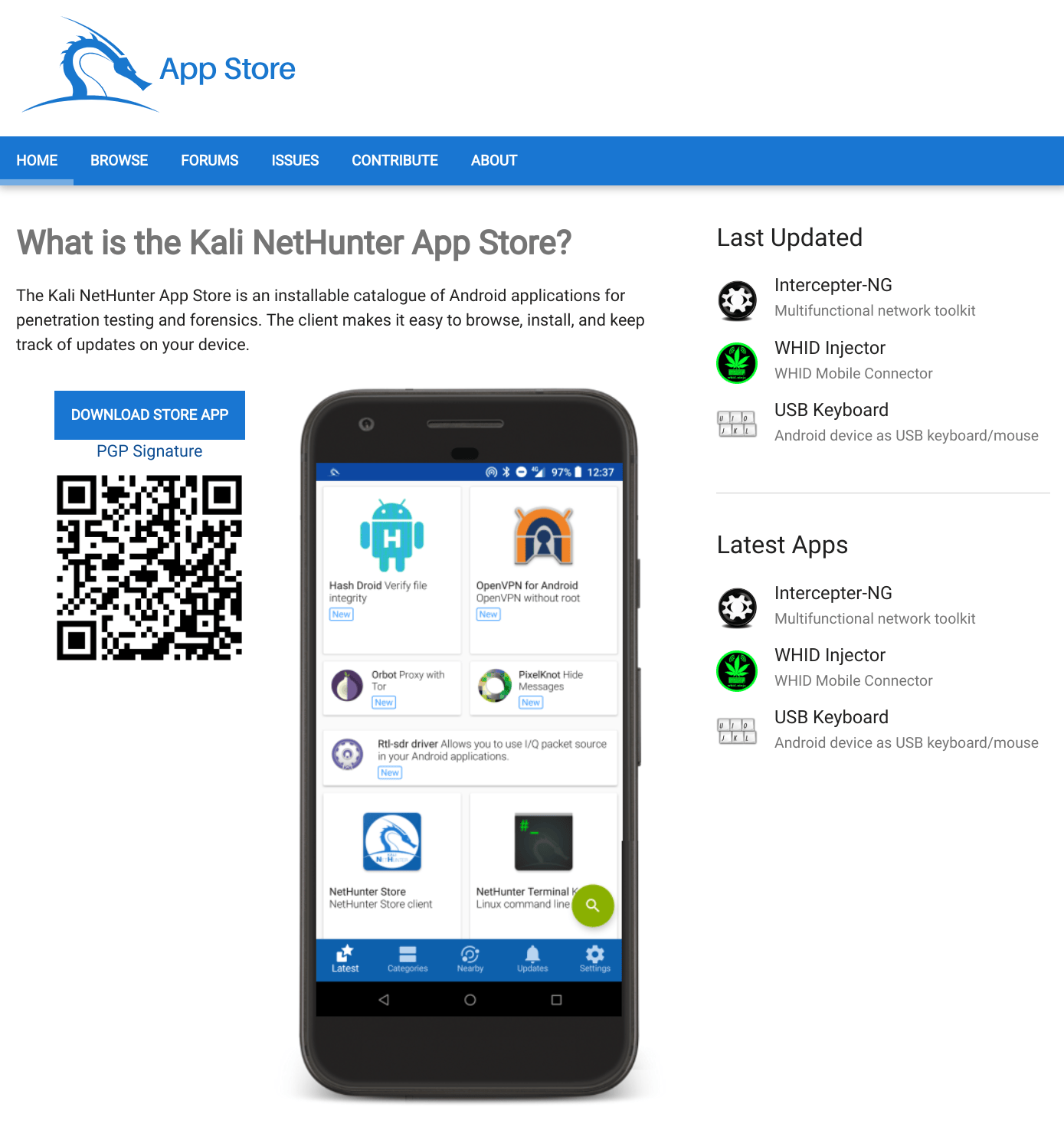
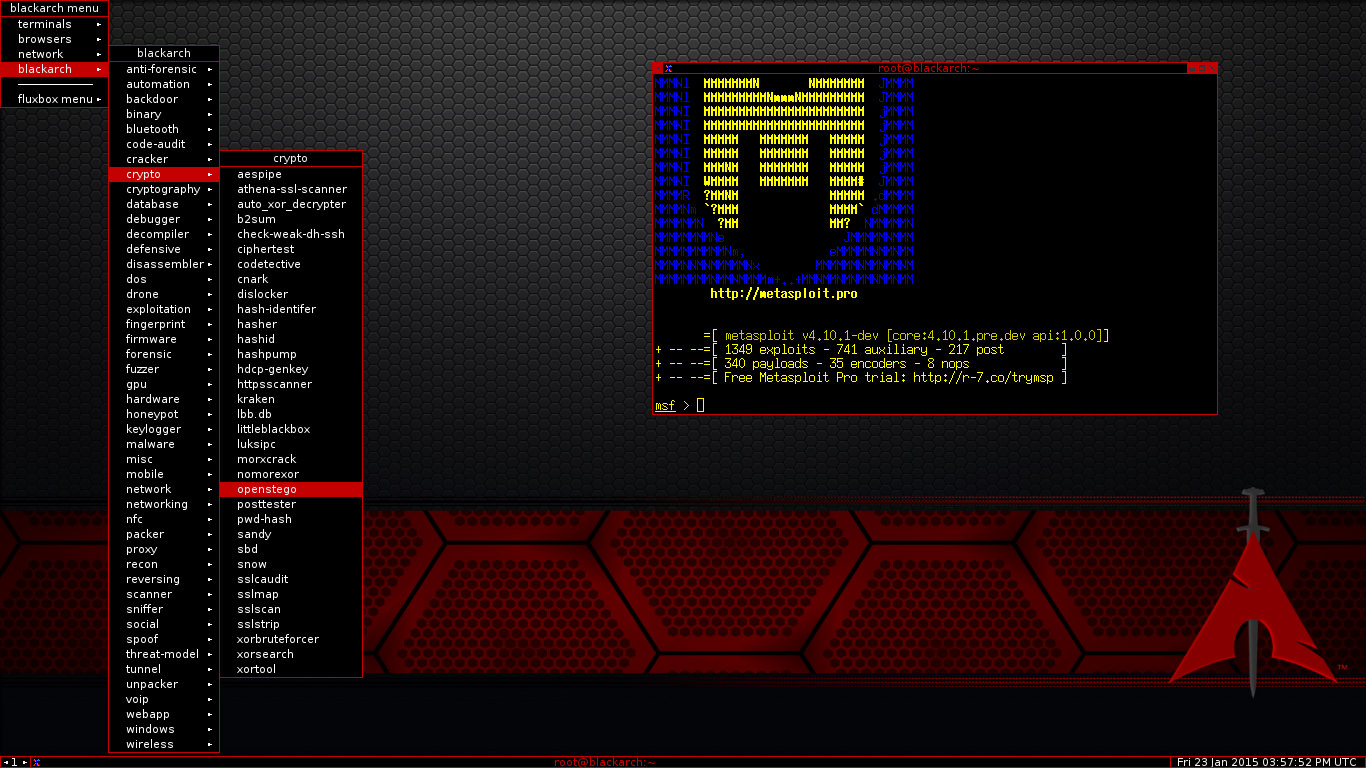
Kali Linux Penetration Testing Mobile

💣 👉🏻👉🏻👉🏻 FOR MORE INFORMATION, CLICK HERE 👈🏻👈🏻👈🏻
Adventure Time Fionna Naked
Soloflesh Personal Satisfaction Device
Micro Bikini Abby Cross
Teen Cute Pic
GF Rubbing Cum-Gap Down
abee4849
Apricot Guest Book
Kali Linux Penetration Testing Mobile





























































70">