Honeypots Guide
🇲𝐚𝐣𝐨𝐫🇰𝐚𝐥𝐢™️ 🧡✺💚What Is a Honeypot?
A honeypot is a fake resource that is used to detect or divert information security attacks. A honeypot is a cybersecurity mechanism that uses a manufactured attack target to lure cybercriminals away from legitimate targets.
What are honeynet ?
A honeynet is a network of honeypots that is designed to look like a real network, complete with multiple systems, databases, servers, routers and other digital assets. Since the honeynet, or honeypot system, mimics the sprawling nature of a typical network, it tends to engage cybercriminals for a longer period of time.
A “honeywall” monitors the traffic going in and out of the network and directs it to the honeypot instances. You can inject vulnerabilities into a honeynet to make it easy for an attacker to access the trap.
Types of Honeypots :
1.) Production Honeypot
A production honeypot is the most common type and used to gather intelligence information regarding cyberattacks within a production network. A production honeypot can gather attributes like IP addresses, data breach attempts, dates, traffic, and volume.
2.) Research Honeypot
A more complex type of honeypot, a research honeypot is made to gather information about specific methods and tactics used by attackers. It is also used to uncover the potential vulnerabilities that exist within a system in relation to the tactics applied by attackers
3.) High-Interaction Honeypots
These honeypots do not hold too much data. They are not designed to imitate a full-scale production system, but they do run all the services that a production system would—such as a fully-functional OS. These types of honeypots allow the security teams to see the actions and strategies of intruding attackers in real-time.
4.) Low-Interaction Honeypots
These honeypots are mostly deployed in production environments. By running on a limited number of services, they serve as early detection points for security teams. Low-interaction honeypots are mostly idle, waiting for some activity to happen so they can alert you.
5.) Malware Honeypots
Sometimes attackers try to infect open and vulnerable systems by hosting a malware sample on them. Since the IP addresses of vulnerable systems are not on a threat list, it is easier for attackers to host malware.
6.) Spam Honeypots
These honeypots attract spammers by using open proxies and mail relays. They are used to gather information on new spam and email-based spams since spammers perform tests on mail relays by using them to send emails to themselves.
7.) Client Honeypots
As the name suggests, client honeypots imitate the critical parts of a client's environment to help with more targeted attacks. While there is no read data used for these types of honeypots, they can make any fake host look similar to a legitimate one.
8.) Medium-Interaction Honeypots
As the name suggests, medium-interaction honeypots fall between high and low interaction honeypots. They come with expanded capabilities compared to low interaction honeypots but reduced implementation complexities than high interaction honeypots. They imitate the application layer but don’t have their own operating system. Organizations typically deploy these types of honeypots to stall attackers to give them time to respond to attacks.
9.) Email Honeypots
Email honeypots are a list of email addresses used by email service providers to detect spammers. Typically, accounts inactive over a long period of time are used for this purpose.
10.) Spider Honeypots
These honeypots are used to trap web-crawlers by creating fake web pages and links only reachable by crawlers. Detecting these crawlers can be useful in blocking bot activity.
👀How to implement honeypots ?
Step 1.Install the honeypot software
The first step in implementing a honeypot is to create the right environment. Admins should choose honeypot software they want to use, prepare the infrastructure for that software and install it. Virtual servers and physical servers can host honeypots. When using a physical server, it is important to take the following precautions to ensure it's secure:
Don't use administrator accounts with access to important systems. Use a different account.
Don't store important data on the server, use decoy data instead.
Isolate the physical server from the rest of the network.
Virtual machines are safer because if they are compromised, they can just be shut down quickly and recreated. If using a virtual server, network admins will want to create one or a collection of virtual machines using a hypervisor.
Step 2. Configure firewall and logging policies
The next step in the installation process is to determine which events the honeypot program will monitor. These can include login attempts, file changes and other activity. Admins must set up an alternative logging method, because hackers can change log files if they know where to look for them. To prevent this, log files should be out of sight and in a place hackers wouldn't think to look, such as in the Windows logging tool or some other cloud logging services that store the information outside of the honeypot.
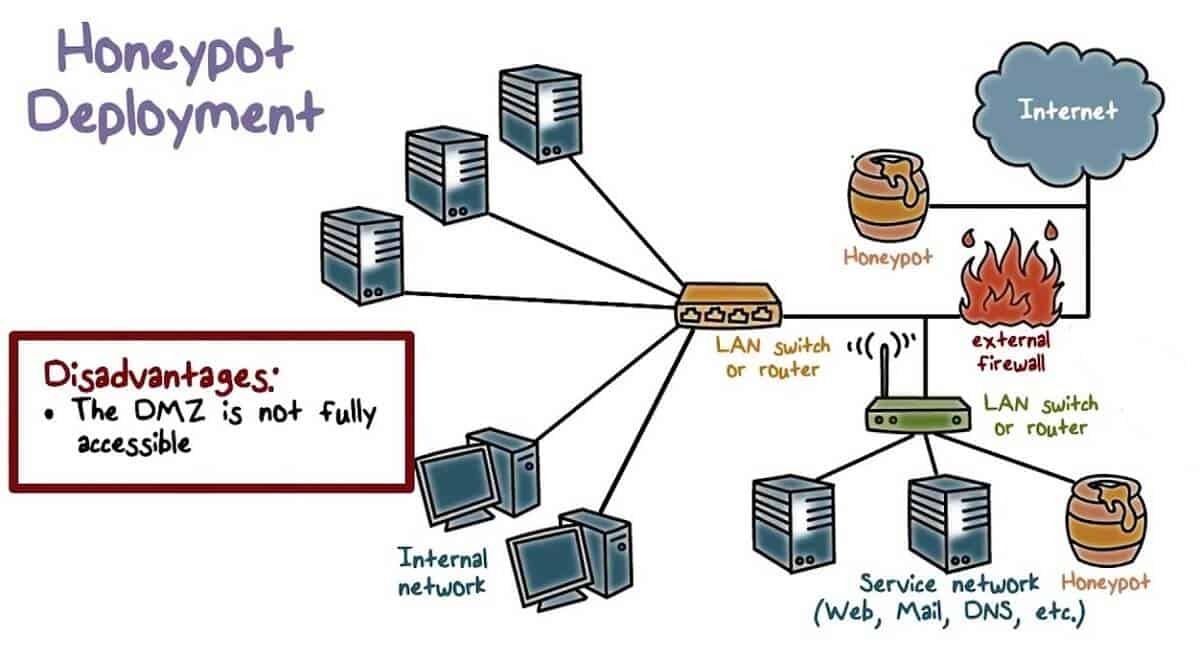
The honeypot itself is placed outside the internal firewall, but inside of the DMZ. The external firewall should be configured so that only the ports necessary to access the honeypot are open, and all others are closed. This approach will direct traffic toward the open network where the honeypot is and not the internal network behind the firewall.
Step 3. Configure the honeypot
In contrast to the internal firewall, the honeypot is vulnerable. It should have several ports open and invite attackers in. However, admins should not open all the ports. Doing so will make it obvious to attackers that they are not on a critical server, and they will leave, or worse, they will manipulate the honeypot to their advantage.
Step 4. Testing
Port scanners, such as Nmap and penetration testing tools, are useful for testing a honeypot setup. Attackers will often undertake their own port scan to look for vulnerabilities in a target network. Network admins can use Nmap to see what attackers see when they are poking around.
Next, admins should perform some activity inside the honeypot and then review server logs to check that everything logged properly. For example, if an IDS is running, it might automatically block a port scan attempt and show that the port as unavailable, alerting the attacker that the port is defended and encourage them to go elsewhere.These issues should be fixed before putting a honeypot into production. The honeypot must be able to lure attackers in and capture as much information as possible, and any impediment to that should be removed. After initial testing, put the honeypot into production, monitor it closely and fine-tune the configuration.
👀Honeypot Course : https://t.me/ethicsec/325
Top Best Honeypot Tools
💘Attivo Inc.'s ThreatDefend.
This honeypot and deception tool has automatic learning capabilities. It profiles visible virtual local area networks (VLAN) to customize the decoys it deploys. It can detect techniques hackers use to move laterally into the enterprise network. It specializes in working with advanced persistent threats (APT), which are designed to beat traditional security controls.
💘Gianluca Brindisi's Wordpot
This honeypot is designed to enhance WordPress security. Users can detect files that hackers use to gather technical information about -- also known as fingerprinting -- a WordPress page. Wordpot can install custom plugins to emulate common vulnerabilities in WordPress. It is accessible using a command-line interface (CLI).
💘The Honeynet Project's Ghost USB
This open source honeypot looks like a USB storage drive on the network. It attracts and monitors malware that spreads through these devices. Users can access Ghost USB through a GUI or a CLI.
💘Honeynet Project's Glastopf
This low-interaction, open source honeypot emulates a vulnerable web server. It runs on Python, PHP and MySQL, and it can emulate thousands of vulnerabilities.
💘The Honeynet Project's Snare and Tanner
It is an open source web application honeypot that enables the user to convert a webpage to an attack surface. Snare records events and sends them to Tanner, which decides how Snare should respond to the threat. Users can change multiple sensors at once to adapt to evolving threats.
💘HoneyThing
This open source internet of things (IOT) honeypot acts as a modem or router and supports the customer premises equipment (CPE) WAN Management Protocol and runs on Allegro's RomPager web server. With it, users can emulate common IoT vulnerabilities such as the Misfortune Cookie router vulnerability to attract attackers. HoneyThing features an easy-to-use web-based interface instead of a CLI.
💘KeyFocus Ltd.'s KFSensor
This IDS includes a Windows-based honeypot. KFSensor is preconfigured to monitor common ports, such as TCP, UDP and ICMP, and emulate common services, such as Microsoft Telnet Service. It enables administrators to watch attackers without exposing any real services.
Some other Honeypot Tools :
Database Honeypots
- Delilah — Elasticsearch Honeypot written in Python (originally from Novetta).
- ESPot — Elasticsearch honeypot written in NodeJS, to capture every attempts to exploit CVE-2014–3120.
- Elastic honey — Simple Elasticsearch Honeypot.
- HoneyMysql — Simple Mysql honeypot project.
- MongoDB-HoneyProxy — MongoDB honeypot proxy.
- NoSQLpot — Honeypot framework built on a NoSQL-style database.
- mysql-honeypotd — Low interaction MySQL honeypot written in C.
- MysqlPot — MySQL honeypot, still very early stage.
- pghoney — Low-interaction Postgres Honeypot.
- sticky_elephant — Medium interaction postgresql honeypot.
Web honeypots
- Bukkit Honeypot — Honeypot plugin for Bukkit.
- EoHoneypotBundle — Honeypot type for Symfony2 forms.
- Glastopf — Web Application Honeypot.
- Google Hack Honeypot — Designed to provide reconnaissance against attackers that use search engines as a hacking tool against your resources.
- Laravel Application Honeypot — Simple spam prevention package for Laravel applications.
- Nodepot — NodeJS web application honeypot.
- Servletpot — Web application Honeypot.
- Shadow Daemon — Modular Web Application Firewall / High-Interaction Honeypot for PHP, Perl, and Python apps.
- StrutsHoneypot — Struts Apache 2 based honeypot as well as a detection module for Apache 2 servers.
- WebTrap — Designed to create deceptive webpages to deceive and redirect attackers away from real websites.
- basic-auth-pot (bap) — HTTP Basic Authentication honeypot.
- bwpot — Breakable Web applications honeyPot.
- django-admin-honeypot — Fake Django admin login screen to notify admins of attempted unauthorized access.
- drupo — Drupal Honeypot.
- honeyhttpd — Python-based web server honeypot builder.
- phpmyadmin_honeypot — Simple and effective phpMyAdmin honeypot.
- shockpot — WebApp Honeypot for detecting Shell Shock exploit attempts.
- smart-honeypot — PHP Script demonstrating a smart honey pot.
- Snare/Tanner — successors to Glastopf
- Snare — Super Next generation Advanced Reactive honeypot.
- Tanner — Evaluating SNARE events.
- stack-honeypot — Inserts a trap for spam bots into responses.
- tomcat-manager-honeypot — Honeypot that mimics Tomcat manager endpoints. Logs requests and saves attacker’s WAR file for later study
WordPress honeypots
- HonnyPotter — WordPress login honeypot for collection and analysis of failed login attempts.
- HoneyPress — Python based WordPress honeypot in a Docker container.
- wp-smart-honeypot — WordPress plugin to reduce comment spam with a smarter honeypot.
- wordpot — WordPress Honeypot.
Service Honeypots
- AMTHoneypot — Honeypot for Intel’s AMT Firmware Vulnerability CVE-2017–5689.
- Ensnare — Easy to deploy Ruby honeypot.
- HoneyPy — Low interaction honeypot.
- Honeygrove — Multi-purpose modular honeypot based on Twisted.
- Honeyport — Simple honeyport written in Bash and Python.
- Honeyprint — Printer honeypot.
- Lyrebird — Modern high-interaction honeypot framework.
- MICROS honeypot — Low interaction honeypot to detect CVE-2018–2636 in the Oracle Hospitality Simphony component of Oracle Hospitality Applications (MICROS).
- RDPy — Microsoft Remote Desktop Protocol (RDP) honeypot implemented in Python.
- SMB Honeypot — High interaction SMB service honeypot capable of capturing wannacry-like Malware.
- Tom’s Honeypot — Low interaction Python honeypot.
- WebLogic honeypot — Low interaction honeypot to detect CVE-2017–10271 in the Oracle WebLogic Server component of Oracle Fusion Middleware.
- WhiteFace Honeypot — Twisted based honeypot for WhiteFace.
- honeycomb_plugins — Plugin repository for Honeycomb, the honeypot framework by Cymmetria.
- honeyntp — NTP logger/honeypot.
- honeypot-camera — Observation camera honeypot.
- honeypot-ftp — FTP Honeypot.
- honeytrap — Advanced Honeypot framework written in Go that can be connected with other honeypot software.
- pyrdp — RDP man-in-the-middle and library for Python 3 with the ability to watch connections live or after the fact.
- troje — Honeypot that runs each connection with the service within a seperate LXC container.
What is Canary Honeypot System ?
A canary honeypot is a system that mimics a production system and is deployed to serve as an early detection mechanism in the event of a network breach. These honeypots can operate in two different formats; either as an exploitable or non-exploitable honeypot.

What are Canary Tokens ?
Canary tokens are significantly different in that they are embedded in files and designed to trigger alerts when an attacker accesses them.If an attacker attempts to penetrate your system and engages with a canary device, a message is automatically sent to whomever you choose, typically through a text message, email, or another notification system. At that point, admins or other users become aware of the attack and can take precautions or mitigation measures as needed. With a canary token, if an attacker opens the file or Uniform Resource Locator (URL) with the token embedded, information about the attacker and the token automatically gets transmitted to your network’s defenders. Canary tokens and devices can therefore provide incident responders with valuable information regarding the methodology and identities of the attackers.

Canary Token Website: https://www.canarytokens.org/generate