Google Dorks And Google Hacking
⭕🔱🇰🇦🇱🇮™🔱⭕Hii buddy ,
Google Hacking techniques and the most popular one is Google Dorks List 2021 also knows as Google Dorking.
Google Dorks List 2021 – Google Hacking Database (Download)
Below is the file which has all the new Google Dorks that you can use for your Google hacking techniques.
2021/2020 Google Dorks List Download
🍎How to use Google Dorks for Credit Cards Details🍎
Step 1: Find Vulnerable Sites Using Google Dorks
We will use Google Dorks for getting credit card details by simply filtering the Search results containing the saved credit cards details.
Type the below code into your Google Search Bar:-
inurl:”.php?cat=”+intext:”Paypal”
Wondering what this weird thing is?
This is a basic Google dork code to get info about Paypal credit card.
Simply “inurl:” will filter the Google search results with websites having ” .php?cat “.
Whereas the intext will filter the search results containing the text”Paypal“.
After searching for the above Google Dork you will get a ton of websites containing various details about the Paypal payments.
The above Google dork is not only the single and most relevant Google Dork, there are a lot of others.
inurl:”.php?id=” intext:”Chekout”
inurl:”.php?id=” intext:”/Buy now/”
inurl:”.php?id=” intext:”/Payment Successful/”
inurl:”.php?id=” intext:”/Delivery address/”
inurl:”.php?id=” intext:”/Payment method/”
inurl:”.php?id=” intext:”/store/”
inurl:”.php?id=” intext:”/Delivery time/”
inurl:”.php?id=” intext:”/add to kart/”
inurl:”.php?id=” intext:”/Proceed to payment/”
inurl:”.php?id=” intext:”/Keep shoping/”
Also check out: List of 1000+Fresh Google Dorks
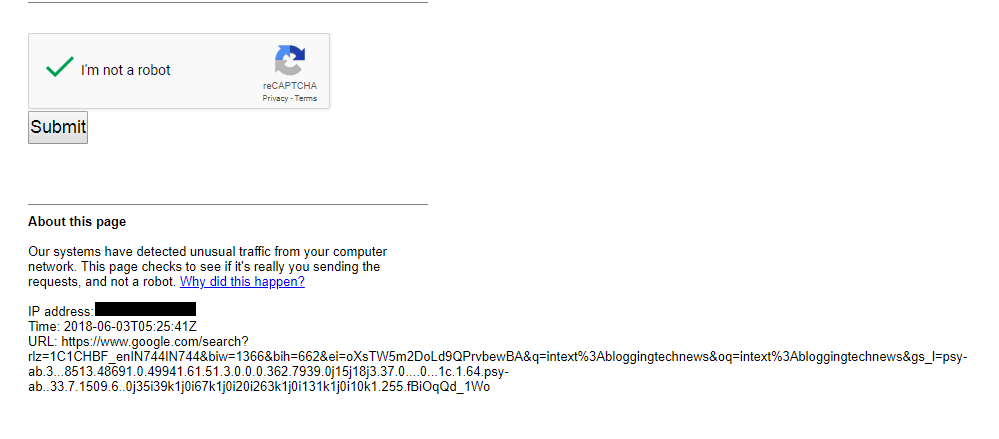
When entering these Google Dorks for credit card details you can get a warning from Google like below:
Don’t worry, fill the Captcha and you are good to go again.
Step 2: Use SQL In
jection to Login after getting the Google Dorks for credit card detail:

SQL is the common hacking technique used in cracking the logging insecurities.
Injecting a SQL code can bypass the username and password verification by sending a specific code instead of the real username and password.
Suppose you have got a list of websites using Google dorks which you are gonna use to get credit card details of people.
Go to the login page of a particular website and instead of entering the Email Id and password fill both fields with
” or “”=”
After entering the above code press the login button. If your luck is with you have chances of getting logged in into someone’s account.Either read my sql article given in telegram channel @its_me_kali_moments
NOTE: Above topic is only for educational purpose and we don’t appreciate any kind of illegal activities using Google Dorks.
What are search operators?
Google Operators are strings used to narrow the search results downwards. When using search operators and adding the keywords these operators compel search engines to show the specific result.
Now can i make my own dork ?
Yes, you can you just need to be little bit create with this. example if you want to get shopping sites in india then dork is
inurl:”cart.php” intext:shopping” site:in
lets break it :
inurl => in url of website
intext: => in text of website pages or posts
site => search of in domains only.
And get all working google dorks
here ==>@its_me_kali
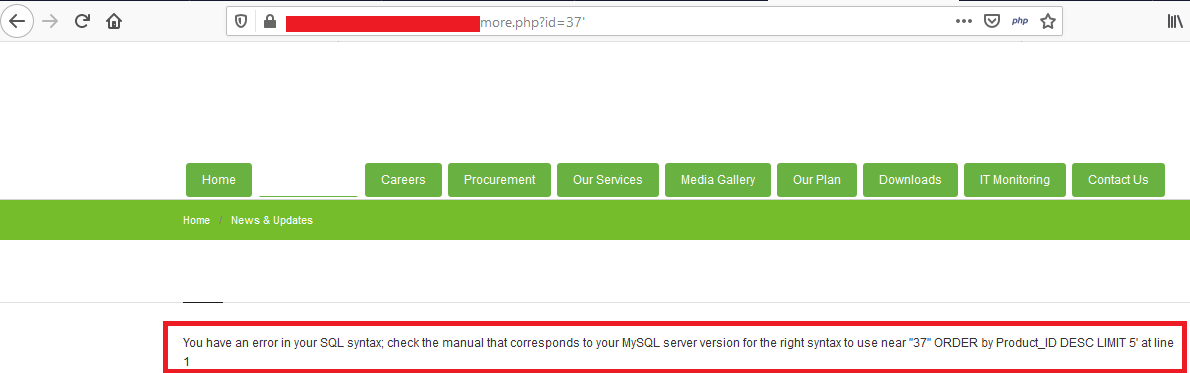
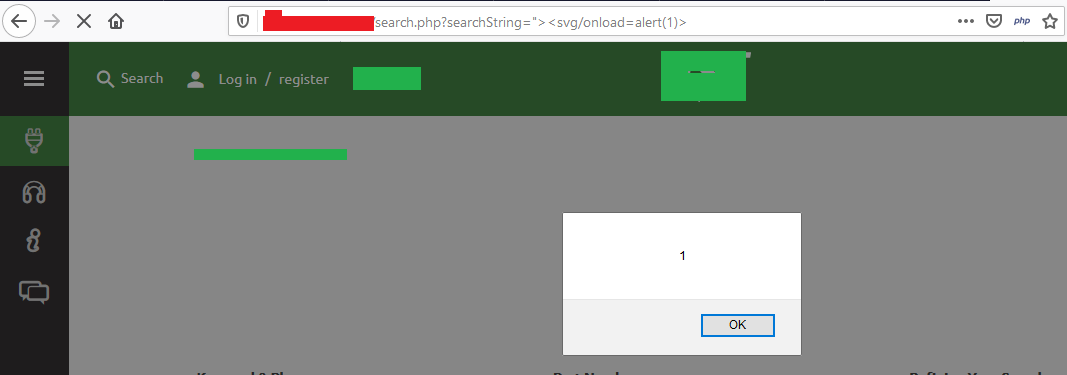
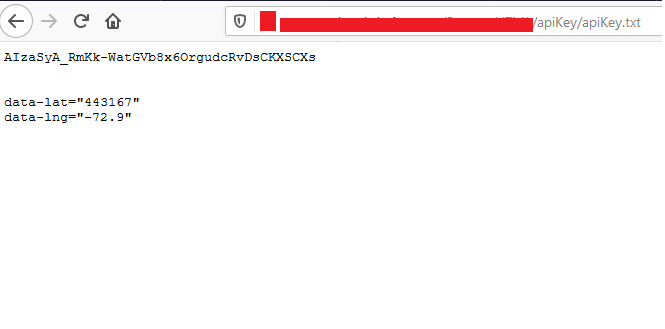
Some of the popular examples for finding websites that are vulnerable to SQL injection, XSS, API keys etc. are
- Dork for SQL Injection - inurl: .php?id=
2. Dork for XSS - inurl:”.php?searchstring=”
3. Dork for API keys - intitle:”index of” api_key OR “api key” OR apiKey
Above are the most common examples of finding some common vulnerabilities on the websites, but this aren’t the limited one.
Still there are many websites that are passing sensitive information using GET method, to make it secure you can use the blocking rules. Commonly, the blocking rules could be setup easily by write some “Disallow” rules at robots.txt file.

While hunting on a private program I found a request where they were using GET parameter which contained email, some key, ID, my country name etc. So I tried finding email’s of other users on the same site and I got some yahoo email ID’s
- Dork Used for yahoo : site:target.com inurl:’@yahoo.co’ (which will give me .com and .co.in) emails of yahoo

I got an excel sheet containing yahoo emails and phone numbers of the users of that site.
Now I wanted to find some more emails so I enumerated further and got emails of outlook.live and gmail.com
2. Dork Used for outlook : site:target.com inurl:’@live.com’

3. Dork Used for gmail : site:target.com inurl:’@gmail.com’

Some more useful dorks :
- site:<Website> inurl:<GET Parameter>
Example :
i) site:target.com inurl:api_key
ii) site:target.com inurl:email
iii) site:target.com inurl:amount
2. intitle:”index of” “/etc/mysql/”
3. site:”target.com” database.yml
4. inurl:group_concat(username, filetype:php intext:admin
5. inurl:/wwwboard/passwd.txt
6. filetype:reg reg HKEY_CLASSES_ROOT -git
7. inurl:/database* ext:sql intext:index of -site:target.com
This are some of the not so common but useful Google Dorks to find sensitive information of the website. You can also modify this dorks and you can also use more dorks with this dorks.
NOTE : You can prevent a page from appearing in Google Search by including a “noindex” meta tag in the page's HTML code, or by returning a 'noindex' header in the HTTP request.
🍎 HOW TO SEARCH ANY THREAD ON ANONFILES USING GOOGLE DORKS🍎
🍎SIMPLE : site:"anonfile.com" "<search term>"
🍎 EXAMPLE : site:"anonfile.com" "<combos>"
site:"anonfile.com" "<giftcards>"
Google Dorks https://play.google.com/store/apps/details?id=com.rushic24.root.mydork2
🎷🎷SOME OTHER GOOGLE DORKS 🎷🎷
intext:"add you search test here" intitle:"index.of" +(wmv|mpg|avi|mp4|mkv|mov) -inurl:(jsp|pl|php|html|aspx|htm|cf|shtml)
🍎Images :
intext:"add you search test here" intitle:"index.of./" (bmp|gif|jpg|png|psd|tif|tiff) -inurl:(jsp|pl|php|html|aspx|htm|cf|shtml)
🍎Music :
intext:"add you search test here" intitle:"index.of./" (ac3|flac|m4a|mp3|ogg|wav|wma) -inurl:(jsp|pl|php|html|aspx|htm|cf|shtml)
🍎Books :
intitle:"add you search test here" (pdf|epub|mob) "name or title" -inurl:(jsp|pl|php|html|aspx|htm|cf|shtml)
🏴 Popular Google Dork operators
Google’s search engine has its own built-in query language. The following list of queries can be run to find a list of files, find information about your competition, track people, get information about SEO backlinks, build email lists, and of course, discover web vulnerabilities.
Let’s look at the most popular Google Dorks and what they do.
cache: this dork will show you the cached version of any website, e.g.cache: itsmekali.comallintext: searches for specific text contained on any web page, e.g.allintext: hacking toolsallintitle: exactly the same as allintext, but will show pages that contain titles with X characters, e.g.allintitle:"Security Companies"allinurl: it can be used to fetch results whose URL contains all the specified characters, e.g: allinurl client areafiletype: used to search for any kind of file extensions, for example, if you want to search for jpg files you can use:filetype: jpginurl: this is exactly the same asallinurl, but it is only useful for one single keyword, e.g.inurl: adminintitle: used to search for various keywords inside the title, for example,intitle:security toolswill search for titles beginning with “security” but “tools” can be somewhere else in the page.inanchor: this is useful when you need to search for an exact anchor text used on any links, e.g.inanchor:"cyber security"intext: useful to locate pages that contain certain characters or strings inside their text, e.g.intext:"safe internet"link: will show the list of web pages that have links to the specified URL, e.g.link: microsoft.comsite: will show you the full list of all indexed URLs for the specified domain and subdomain, e.g.site:securitytrails.com*: wildcard used to search pages that contain “anything” before your word, e.g.how to * a website, will return “how to…” design/create/hack, etc… “a website”.|: this is a logical operator, e.g."security" "tips"will show all the sites which contain “security” or “tips,” or both words.+: used to concatenate words, useful to detect pages that use more than one specific key, e.g. ititsme+ kali–: minus operator is used to avoiding showing results that contain certain words, e.g. its_me_kali will show pages that use “its_me_kali” in their text, but not those that have the word “Kali”
Google Dork examples
Let’s take a look at some practical examples. You’ll be surprised how easy is to extract private information from any source just by using Google hacking techniques.
🎷Log files🎷
Log files are the perfect example of how sensitive information can be found within any website. Error logs, access logs and other types of application logs are often discovered inside the public HTTP space of websites. This can help attackers find the PHP version you’re running, as well as the critical system path of your CMS or frameworks.
For this kind of dork we can combine two Google operators, allintext and filetype, for example:
allintext:username filetype:log
This will show a lot of results that include username inside all *.log files.
In the results we discovered one particular website showing an SQL error log from a database server that included critical information:
MyBB SQL Error
SQL Error: 1062 - Duplicate entry 'XXX' for key 'username'
Query:
INSERT
INTO XXX (`username`,`password`,`salt`,`loginkey`,`email`,`postnum`,`avatar`,`avatartype`,`usergroup`,`additionalgroups`,`displaygroup`,`usertitle`,`regdate`,`lastactive`,`lastvisit`,`website`,`icq`,`aim`,`yahoo`,`msn`,`birthday`,`signature`,`allownotices`,`hideemail`,`subscriptionmethod`,`receivepms`,`receivefrombuddy`,`pmnotice`,`pmnotify`,`showsigs`,`showavatars`,`showquickreply`,`showredirect`,`tpp`,`ppp`,`invisible`,`style`,`timezone`,`dstcorrection`,`threadmode`,`daysprune`,`dateformat`,`timeformat`,`regip`,`longregip`,`language`,`showcodebuttons`,`away`,`awaydate`,`returndate`,`awayreason`,`notepad`,`referrer`,`referrals`,`buddylist`,`ignorelist`,`pmfolders`,`warningpoints`,`moderateposts`,`moderationtime`,`suspendposting`,`suspensiontime`,`coppauser`,`classicpostbit`,`usernotes`)
VALUES ('XXX','XXX','XXX','XXX','XXX','0','','','5','','0','','1389074395','1389074395','1389074395','','0','','','','','','1','1','0','1','0','1','1','1','1','1','1','0','0','0','0','5.5','2','linear','0','','','XXX','-655077638','','1','0','0','0','','','0','0','','','','0','0','0','0','0','0','0','')
This example exposed the current database name, user login, password and email values to the Internet. We’ve replaced the original values with “XXX”.
Vulnerable web servers
The following Google Dork can be used to detect vulnerable or hacked servers that allow appending “/proc/self/cwd/” directly to the URL of your website.
inurl:/proc/self/cwd
As you can see in the following screenshot, vulnerable server results will appear, along with their exposed directories that can be surfed from your own browser.

Open FTP servers
Google does not only index HTTP-based servers, it also indexes open FTP servers.
With the following dork, you’ll be able to explore public FTP servers, which can often reveal interesting things.
intitle:"index of" inurl:ftp
In this example, we found an important government server with their FTP space open. Chances are that this was on purpose — but it could also be a security issue.

ENV files
.env files are the ones used by popular web development frameworks to declare general variables and configurations for local and online dev environments.
One of the recommended practices is to move these .env files to somewhere that isn’t publicly accessible. However, as you will see, there are a lot of devs who don’t care about this and insert their .env file in the main public website directory.
As this is a critical dork we will not show you how do it; instead, we will only show you the critical results:

You’ll notice that unencrypted usernames, passwords and IPs are directly exposed in the search results. You don’t even need to click the links to get the database login details.
SSH private keys
SSH private keys are used to decrypt information that is exchanged in the SSH protocol. As a general security rule, private keys must always remain on the system being used to access the remote SSH server, and shouldn’t be shared with anyone.
With the following dork, you’ll be able to find SSH private keys that were indexed by uncle Google.
intitle:index.of id_rsa -id_rsa.pub
Let’s move on to another interesting SSH Dork.
If this isn’t your lucky day, and you’re using a Windows operating system with PUTTY SSH client, remember that this program always logs the usernames of your SSH connections.
In this case, we can use a simple dork to fetch SSH usernames from PUTTY logs:
filetype:log username putty
Here’s the expected output:

Email lists
It’s pretty easy to find email lists using Google Dorks. In the following example, we are going to fetch excel files which may contain a lot of email addresses.
filetype:xls inurl:"email.xls"

We filtered to check out only the .edu domain names and found a popular university with around 1800 emails from students and teachers.
site:.edu filetype:xls inurl:"email.xls"
Remember that the real power of Google Dorks comes from the unlimited combinations you can use. Spammers know this trick too, and use it on a daily basis to build and grow their spamming email lists.
Live cameras
Have you ever wondered if your private live camera could be watched not only by you but also by anyone on the Internet?
The following Google hacking techniques can help you fetch live camera web pages that are not restricted by IP.
Here’s the dork to fetch various IP based cameras:
inurl:top.htm inurl:currenttime
To find WebcamXP-based transmissions:
intitle:"webcamXP 5"
And another one for general live cameras:
inurl:"lvappl.htm"
There are a lot of live camera dorks that can let you watch any part of the world, live. You can find education, government, and even military cameras without IP restrictions.
If you get creative you can even do some white hat penetration testing on these cameras; you’ll be surprised at how you’re able to take control of the full admin panel remotely, and even re-configure the cameras as you like.

MP3, Movie, and PDF files
Nowadays almost no one downloads music after Spotify and Apple Music appeared on the market. However, if you’re one of those classic individuals who still download legal music, you can use this dork to find mp3 files:
intitle: index of mp3
The same applies to legal free media files or PDF documents you may need:
intitle: index of pdf intext: .mp4
Weather
Google hacking techniques can be used to fetch any kind of information, and that includes many different types of electronic devices connected to the Internet.
In this case, we ran a dork that lets you fetch Weather Wing device transmissions. If you’re involved in meteorology stuff or merely curious, check this out:
intitle:"Weather Wing WS-2"
The output will show you several devices connected around the world, which share weather details such as wind direction, temperature, humidity and more.

Preventing Google Dorks
There are a lot of ways to avoid falling into the hands of a Google Dork.
These measures are suggested to prevent your sensitive information from being indexed by search engines.
- Protect private areas with a user and password authentication and also by using IP-based restrictions.
- Encrypt your sensitive information (user, passwords, credit cards, emails, addresses, IP addresses, phone numbers, etc).
- Run regular vulnerability scans against your site, these usually already use popular Google Dorks queries and can be pretty effective in detecting the most common ones.
- Run regular dork queries against your own website to see if you can find any important information before the bad guys do. You can find a great list of popular dorks at the Exploit DB Dorks database.
- If you find sensitive content exposed, request its removal by using Google Search Console.
- Block sensitive content by using a robots.txt file located in your root-level website directory.
Using robots.txt configurations to prevent Google Dorking
One of the best ways to prevent Google dorks is by using a robots.txt file. Let’s see some practical examples.
The following configuration will deny all crawling from any directory within your website, which is pretty useful for private access websites that don’t rely on publicly-indexable Internet content.
User-agent: * Disallow: /
You can also block specific directories to be excepted from web crawling. If you have an /admin area and you need to protect it, just place this code inside:
User-agent: * Disallow: /admin/
This will also protect all the subdirectories inside.
Restrict access to specific files:
User-agent: * Disallow: /privatearea/file.htm
Restrict access to dynamic URLs that contain ‘?’ symbol
User-agent: * Disallow: /*?
To restrict access to specific file extensions you can use:
User-agent: * Disallow: /*.php$/
In this case, all access to .php files will be denied.
Advanced Google Dorking Commands
- intitle:"index of" inurl:ftp.
- filetype:txt inurl:"email.txt"
- Live cameras We can use Google to find open cameras that are not access restricted by IP address. The following Google dorks retrieve live cameras web pages.
- inurl:"view.shtml" "Network Camera"
- "Camera Live Image" inurl:"guestimage.html"
filetype:log intext:password after:2021 intext:@gmail.com | @yahoo.com | @hotmail.com
I hope you'll like my post , follow
If you want to learn hacking for a month , just msg me !!!!