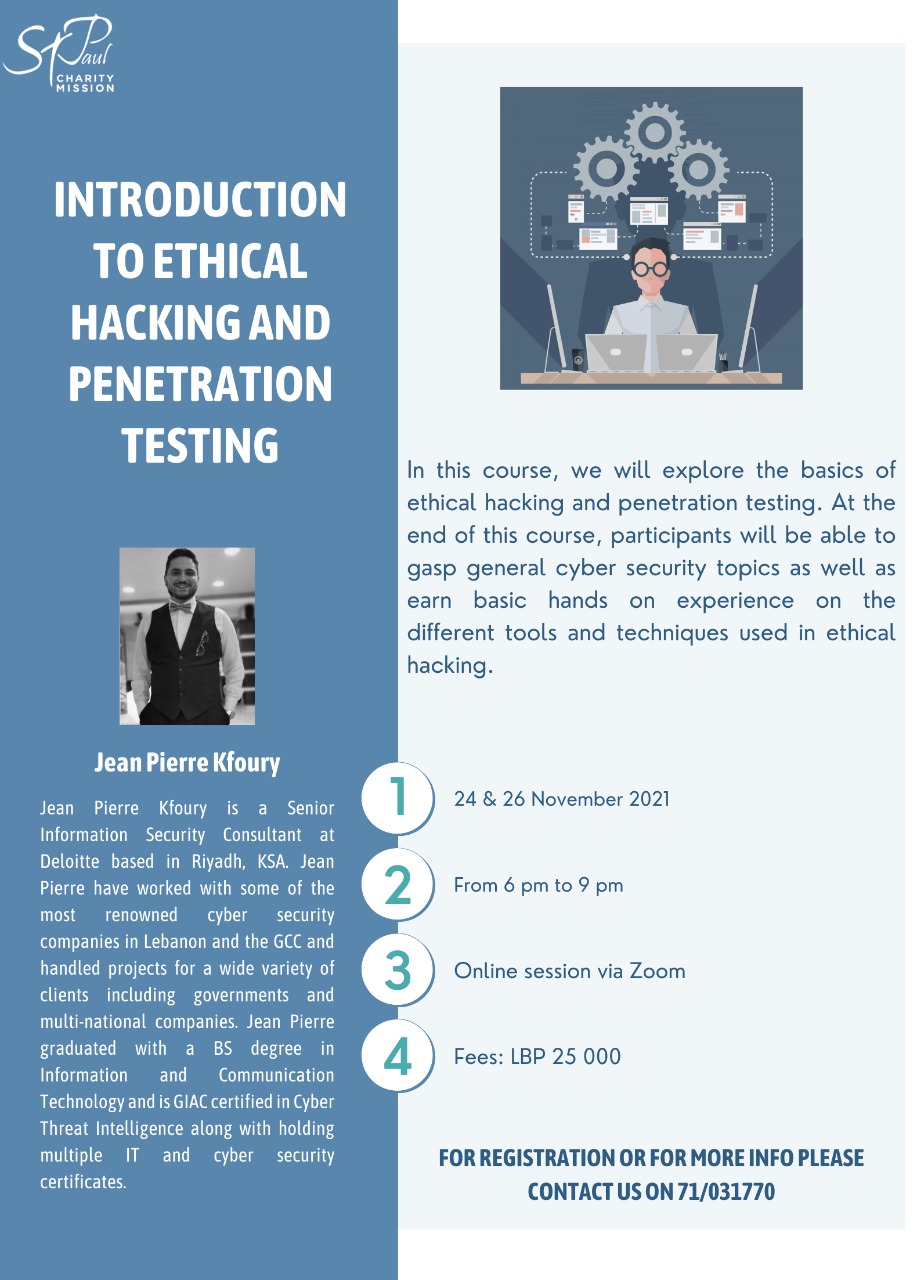
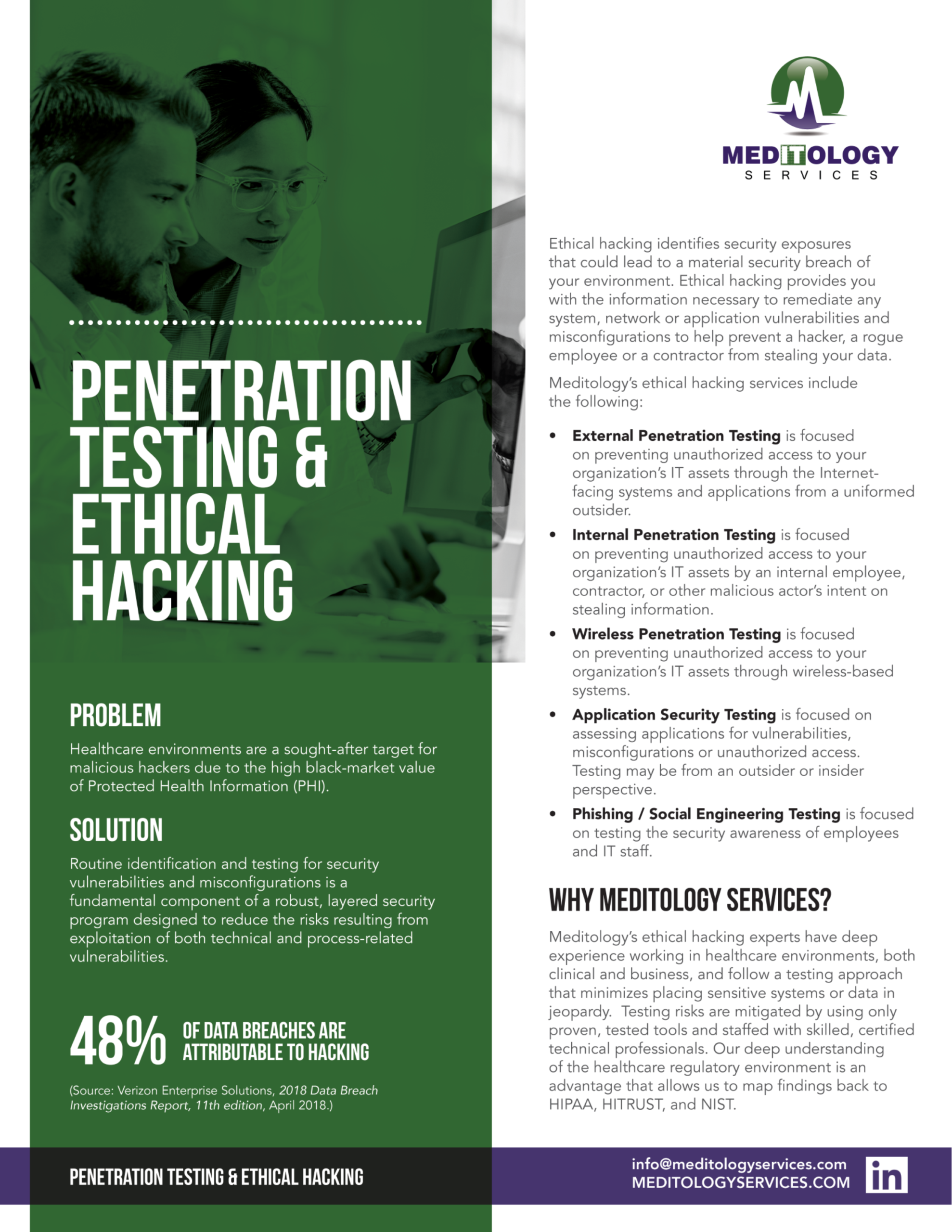
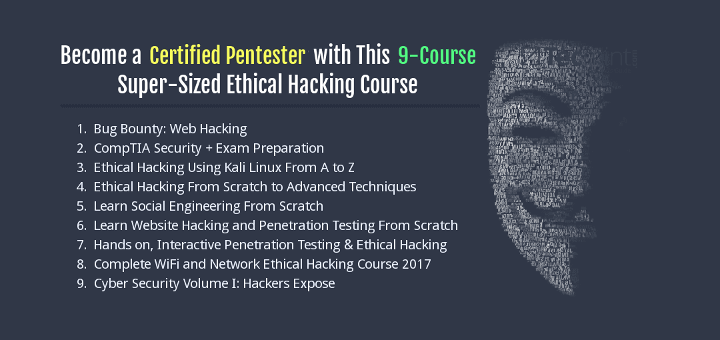
Ethical Hacking Penetration Testing

👉🏻👉🏻👉🏻 FOR MORE INFORMATION, CLICK HERE 👈🏻👈🏻👈🏻
Thai Ladyboys Galleries
Drunk Wife Tits
Licker Porn
Busty Brunette Screwing With Her Bf
Astounding arse in web camera
Bbw Bent Over Ass Outdoors
Aletta Ocean
Ethical Hacking Penetration Testing
204">203">200_.jpg">















70">
-Penetration-Testing-or-Red-Team-Engagement.png">



204">203">200_.jpg">



.png)





































70">