1e87cvplz938w7vyea1e9rwsc8mespa3j5 Private Key
⚡ 👉🏻👉🏻👉🏻 INFORMATION AVAILABLE CLICK HERE 👈🏻👈🏻👈🏻
For information about ASP.NET Core, see ASP.NET Core Data Protection.
This walkthrough demonstrates how to encrypt and decrypt content. The code examples are designed for a Windows Forms application. This application does not demonstrate real world scenarios, such as using smart cards. Instead, it demonstrates the fundamentals of encryption and decryption.
This walkthrough uses the following guidelines for encryption:
Use the Aes class, a symmetric algorithm, to encrypt and decrypt data by using its automatically generated Key and IV.
Use the RSA asymmetric algorithm to encrypt and decrypt the key to the data encrypted by Aes. Asymmetric algorithms are best used for smaller amounts of data, such as a key.
If you want to protect data on your computer instead of exchanging encrypted content with other people, consider using the ProtectedData class.
The following table summarizes the cryptographic tasks in this topic.
Creating a Windows Forms application
Lists the controls that are required to run the application.
Declares string path variables, the CspParameters, and the RSACryptoServiceProvider to have global context of the Form class.
Creates an asymmetric public and private key value pair and assigns it a key container name.
Displays a dialog box to select a file for encryption and encrypts the file.
Displays a dialog box to select an encrypted file for decryption and decrypts the file.
Gets the full key pair using the key container name.
Saves the key to an XML file with only public parameters.
Loads the key from an XML file into the key container.
Lists procedures for testing this application.
You need the following components to complete this walkthrough:
Most of the code examples in this walkthrough are designed to be event handlers for button controls. The following table lists the controls required for the sample application and their required names to match the code examples.
Double-click the buttons in the Visual Studio designer to create their event handlers.
Add the following code as part of the declaration of the class Form1. Edit the string variables for your environment and preferences.
This task creates an asymmetric key that encrypts and decrypts the Aes key. This key was used to encrypt the content and it displays the key container name on the label control.
Add the following code as the Click event handler for the Create Keys button (buttonCreateAsmKeys_Click).
This task involves two methods: the event handler method for the Encrypt File button (buttonEncryptFile_Click) and the EncryptFile method. The first method displays a dialog box for selecting a file and passes the file name to the second method, which performs the encryption.
The encrypted content, key, and IV are all saved to one FileStream, which is referred to as the encryption package.
The EncryptFile method does the following:
Creates a Aes symmetric algorithm to encrypt the content.
Creates an RSACryptoServiceProvider object to encrypt the Aes key.
Uses a CryptoStream object to read and encrypt the FileStream of the source file, in blocks of bytes, into a destination FileStream object for the encrypted file.
Determines the lengths of the encrypted key and IV, and creates byte arrays of their length values.
Writes the Key, IV, and their length values to the encrypted package.
The encryption package uses the following format:
You can use the lengths of the key and IV to determine the starting points and lengths of all parts of the encryption package, which can then be used to decrypt the file.
Add the following code as the Click event handler for the Encrypt File button (buttonEncryptFile_Click).
Add the following EncryptFile method to the form.
This task involves two methods, the event handler method for the Decrypt File button (buttonDecryptFile_Click), and the DecryptFile method. The first method displays a dialog box for selecting a file and passes its file name to the second method, which performs the decryption.
The Decrypt method does the following:
Creates an Aes symmetric algorithm to decrypt the content.
Reads the first eight bytes of the FileStream of the encrypted package into byte arrays to obtain the lengths of the encrypted key and the IV.
Extracts the key and IV from the encryption package into byte arrays.
Creates an RSACryptoServiceProvider object to decrypt the Aes key.
Uses a CryptoStream object to read and decrypt the cipher text section of the FileStream encryption package, in blocks of bytes, into the FileStream object for the decrypted file. When this is finished, the decryption is completed.
Add the following code as the Click event handler for the Decrypt File button.
Add the following DecryptFile method to the form.
This task saves the key created by the Create Keys button to a file. It exports only the public parameters.
This task simulates the scenario of Alice giving Bob her public key so that he can encrypt files for her. He and others who have that public key will not be able to decrypt them because they do not have the full key pair with private parameters.
Add the following code as the Click event handler for the Export Public Key button (buttonExportPublicKey_Click).
This task loads the key with only public parameters, as created by the Export Public Key button, and sets it as the key container name.
This task simulates the scenario of Bob loading Alice's key with only public parameters so he can encrypt files for her.
Add the following code as the Click event handler for the Import Public Key button (buttonImportPublicKey_Click).
This task sets the key container name to the name of the key created by using the Create Keys button. The key container will contain the full key pair with private parameters.
This task simulates the scenario of Alice using her private key to decrypt files encrypted by Bob.
Add the following code as the Click event handler for the Get Private Key button (buttonGetPrivateKey_Click).
After you have built the application, perform the following testing scenarios.
Click the Create Keys button. The label displays the key name and shows that it is a full key pair.
Click the Export Public Key button. Note that exporting the public key parameters does not change the current key.
Click the Encrypt File button and select a file.
Click the Decrypt File button and select the file just encrypted.
Close the application and restart it to test retrieving persisted key containers in the next scenario.
Click the Import Public Key button. The label displays the key name and shows that it is public only.
Click the Encrypt File button and select a file.
Click the Decrypt File button and select the file just encrypted. This will fail because you must have the private key to decrypt.
This scenario demonstrates having only the public key to encrypt a file for another person. Typically that person would give you only the public key and withhold the private key for decryption.
Click the Get Private Key button. The label displays the key name and shows whether it is the full key pair.
Click the Decrypt File button and select the file just encrypted. This will be successful because you have the full key pair to decrypt.
Feedback will be sent to Microsoft: By pressing the submit button, your feedback will be used to improve Microsoft products and services. Privacy policy.
Represents the abstract base class from which all implementations of the Advanced Encryption Standard (AES) must inherit.
Learn how to decrypt data in .NET, using a symmetric algorithm or an asymmetric algorithm.
Accesses the managed version of the Rijndael algorithm. This class cannot be inherited.
Provides cryptographic services, including secure encoding and decoding of data, as well as many other operations, such as hashing, random number generation, and message authentication. For more information, see Cryptographic Services.
Performs symmetric encryption and decryption using the Cryptographic Application Programming Interfaces (CAPI) implementation of the Advanced Encryption Standard (AES) algorithm.
Learn how to encrypt data in .NET, using a symmetric algorithm or an asymmetric algorithm.
Understand how to create and manage symmetric and asymmetric keys for encryption and decryption in .NET.
Represents the abstract base class from which all implementations of symmetric algorithms must inherit.
Feedback will be sent to Microsoft: By pressing the submit button, your feedback will be used to improve Microsoft products and services. Privacy policy.
This site is created to check the safety of Bitcoin network, explain how Blockchain works, show problems of algorithm and add some fun to cryptography.
Whole range of Bitcoin and Bitcoin Cash Private Keys, compressed/ uncompressed, SegWit and HD wallet. Whole wallets including YOURS.
Don't believe?
Do you think it's easy to find chest of Bitcoin treasures? Take a chance! Open page with 20 random generated addresses with count of transactions.
A brain wallet is a hashing of passphrase to create a private key. Humans are pretty bad at being original. REALLY bad at being random. We generate random wallets by popular dictionary.
We hope you did not find your address in leaked database. But you can see other users' private keys. These keys are compormised now.
A bitcoin wallet contains a collection of key pairs, each consisting of a private key and a public key. The private key (k) is a number, usually picked at random. From the private key, we use elliptic curve multiplication, a one-way cryptographic function, to generate a public key (K). From the public key (K), we use a one-way cryptographic hash function to generate a bitcoin address (A). In this section we will start with generating the private key, look at the elliptic curve math that is used to turn that into a public key, and finally, generate a bitcoin address from the public key.
A private key is simply a number, picked at random. Ownership and control over the private key is the root of user control over all funds associated with the corresponding bitcoin address. The private key is used to create signatures that are required to spend bitcoins by proving ownership of funds used in a transaction. The private key must remain secret at all times, as revealing it to a third party is equivalent to giving them control over the bitcoins secured by that key.
The private key must also be backed up and protected from accidental loss, since if lost it cannot be recovered and the funds secured by it are forever lost too.
The first and most important step in generating keys is to find a secure source of entropy, or randomness. Creating a bitcoin key is essentially the same as “Pick a number between 1 and 2^256“. The exact method you use to pick that number does not matter as long as it Is not predictable or repeatable.
Bitcoin software uses the underlying operating system’s random number generators to produce 256 bits of entropy (randomness). Usually, the OS random number generator is initialized by a human source of randomness, which is why you may be asked to wiggle your mouse around for a few seconds. For the truly paranoid, nothing beats dice, pencil and paper.
All Bitcoin private keys is simply an integer between number 1 and 115792089237316195423570985008687907852837564279074904382605163141518161494337 or HEX: from 1 to 0xfffffffffffffffffffffffffffffffebaaedce6af48a03bbfd25e8cd0364141. The integer range of valid private keys is governed by the secp256k1 ECDSA standard used by Bitcoin.
We just generate a range of these integers in sequence, divide into pages and show on each page. We can't store it and we have not saved database, because it should be biggest base on the world.
You can find Private key in WIF (Wallet Import/Export Format) and compressed key. Bitcoin addresses in compressed/ uncompressed formats, SegWit (P2SH-P2WPKH) and native Segwit (P2WPKH) addesses start bc1, Pay to script hash (P2SH) starting with 3; legacy Bitcoin Cash addresses and new format.
2016–2021 AllPrivateKeys.com Dive into Bitcoin with
Naked Man Web Online
Classic Movies Tube
Vintage Retro Gallery Ru
Dream Tranny Fucking
Big Photo Erotic
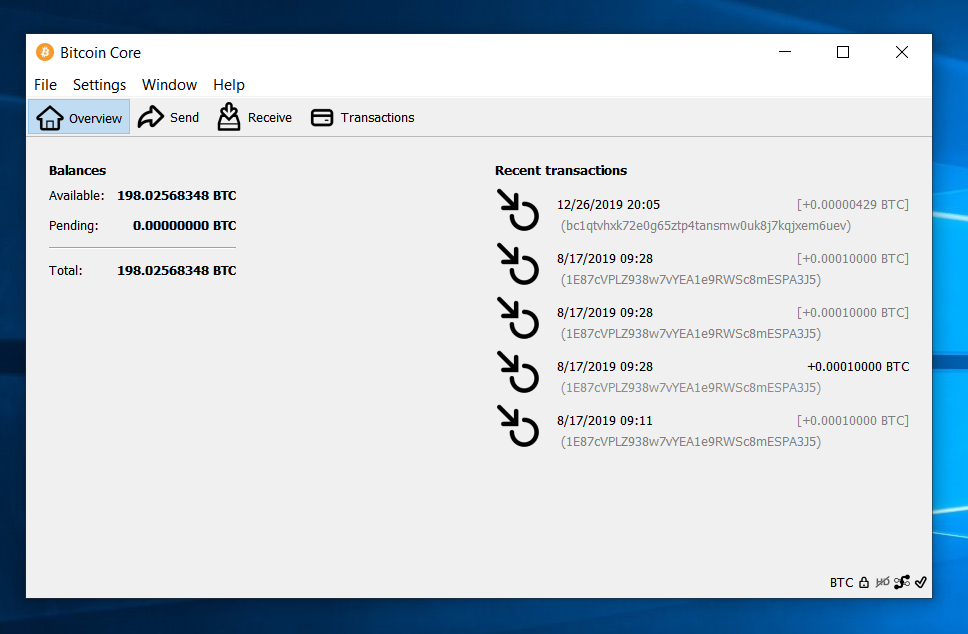
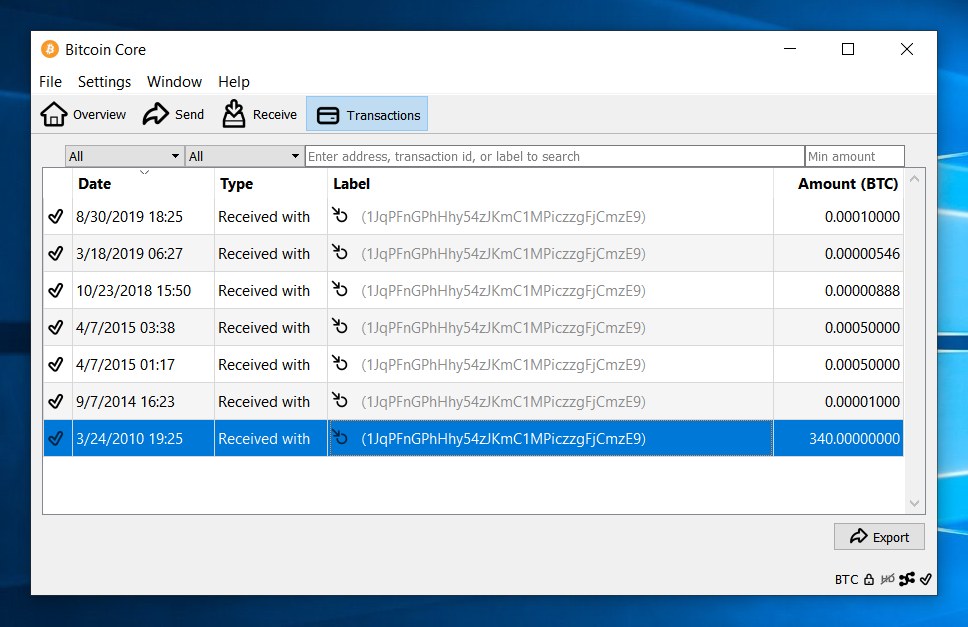
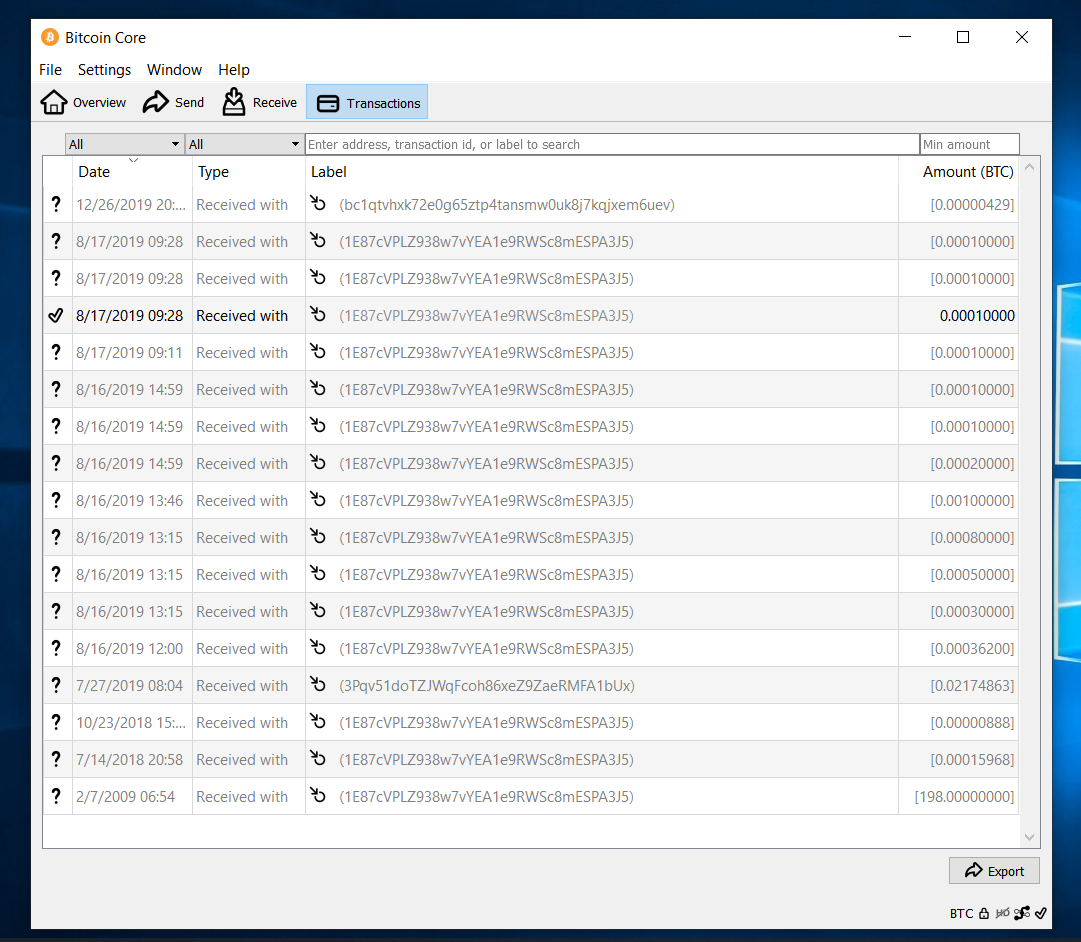
Buy Wallet.dat 198BTC - All private keys
Walkthrough: Creating a Cryptographic Application ...
All Bitcoin private keys and Altcoin private keys.
1E87cVPLZ938w7vYEA1e9RWSc8…
Buy wallet.dat with balance and lost ... - All private keys
Where Is Your Private Key? | DigiCert.com
X509KeyStorageFlags Enum (System.Security.Cryptography ...
How can I find the private key for my SSL certificate ...
RSA.ImportPkcs8PrivateKey(Read…
Что такое CSR | Сгенерировать CSR файл для SSL-сертификат…
1e87cvplz938w7vyea1e9rwsc8mespa3j5 Private Key